What is Zeus Virus?
Zeus, Zbot, or ZeuS is a Trojan horse malware that runs on all versions of Windows based OS. Even though it is capable of many malicious and criminal tasks, but is majorly executed to steal banking information, i.e., Banking id and password, credit card number – using the keystroke logging and form grabbing.
What is “Zeus Virus detected" warning all about?
The reason you are here reading this article is because your system might have given you a warning saying “Zeus Virus” detected or you might have heard about it in the recent news.
So, is this warning real? Is your system infected with Zeus Virus?
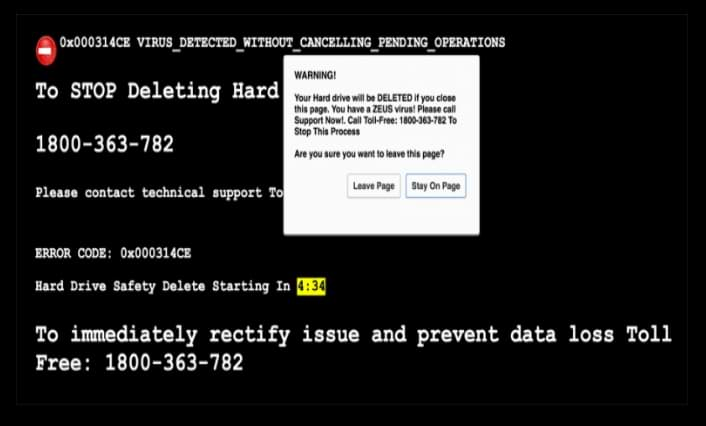
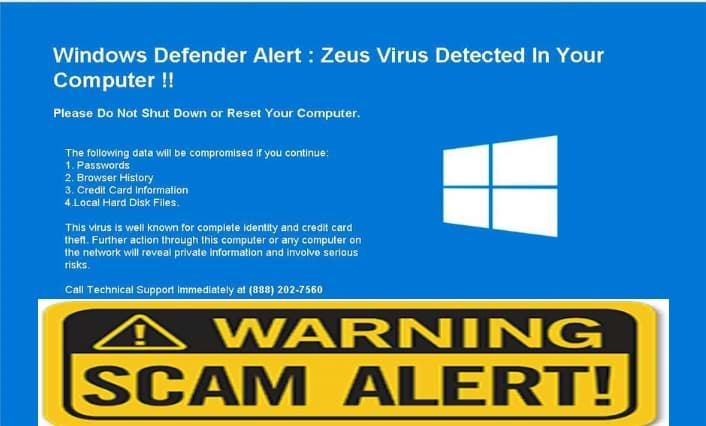
The “Zeus Virus” warning or popup is nothing but a tech support scam done while viewing an infected website or through a widespread malicious program called Adware. This campaign specifically targets Windows OS.
This would make you believe that all your credentials are at risk and if an action is not taken immediately, all your details will be taken away from the computer.
Technically, these adware’s use complicated coding to by-pass the usual firewall of the computer they are designed to insert such fake pop-ups on the victim's computer which enables the malware developers to make money by scaring and fooling people.
End goal of such Adware campaign
Adware is particularly designed to make money. Once an Adware program has infected a computer, it would inject small codes into the pages which you visit very often like your banking account or any social media. This code will create numerous advertisement banners some may include fake security warnings like “Zeus Virus” or insert a sponsored ad on the pages you are viewing.
Web browsers are always under the radar
When your computer is infected with an adware, all your web browsers like Google Chrome, Mozilla Firefox, Internet Explorer, and MS Edge may redirect you to fake security warnings or to sponsored advertisement banners.
Beware of the scammers
Users are Provided with a Toll-free number +1-884-859-0337 asking to immediately contact Apple Care. They will then guide the user through the malware removal process by taking control of the user’s computer. But, what they really do is infect the system with some malware and change the system settings.
Beware the "Zeus Virus" error is nothing but a scam pop-up like any other advertisement pop-up, it has nothing to do with Apple. These technicians will claim to be Apple certified technicians and they will show the user how badly their system is messed up and by scaring the user they would trick the user into paying them for the fix.
It’s a scam but you still have an adware
Although an adware might not damage any files or Windows system, it will certainly annoy you with the frequent notification or ad banner.

Adware is not a virus and it will not harm any of your personal files, but on the other hand, it is a widespread malicious program that generates many such pop-ups and the most shocking fact about an adware program is that it would weaken the firewall of your computer internally and would make way for other malicious programs which include spyware, ransomware, and other malicious programs.
How does an Adware spread?
- Initially, adware installs into a computer via browser hijackers.
- When computers are impacted by a browser hijacker it would make way for other malware and one of the very common malwares these days is Adware.
- Malware authors have developed such tools which can diagnose IP address and distinguish computers based on their security levels and infect them accordingly. In this case, the computers running on the legacy products or outdated security end up being the favorite targets of hackers.
- It can contaminate the PC through restricted websites or through infected websites. In this case, having a good security will help the user to block such websites.
- Adware can get into a computer through portable devices like USB stick, portable hard drives or through any other transferable media.
- Hackers can also infect a computer using freeware programs, this has become the easiest and quickest way of infecting a computer without the user’s consent.
Common symptoms of adware include:
- The web browser would more show signs of instability and frequent crashes.
- The default configuration of the web browser is modified i.e. the default home page and the default search engine is changed.
- A victim might see new extensions and add-on toolbar in the top panel of your web browser.
- Whenever the victim tries to open anything he is been redirected to some random website which may either display advertisement banners or would give fake security warnings.
- Poor program execution, moderate reaction time as the ads would fly out of the blue.
- Even if the web browsers are not active the infected computer would display ads which would result in system crashes from time to time or PC would boot up for unknown reasons.
- Security program and the inbuilt firewall is crippled.
- New icons are added to desktop pretending to be for some kind of security.
Things to Remember:
- Always pay attention while installing software as it comes with additional installs (optional) such as adware.
- Watch out carefully when you agree to install.
- Opt for custom installation always and deselect everything that doesn’t appear to be familiar. Especially, an optional software that you never intended to download.
- Do not install any software that you don’t trust.
The instructions given below are purely for the Windows users.
Information
As there are a lot of steps mentioned along with some programs, this malware removal guide may look a bit immense. This guide is detailed just to provide a clear and easy brief about the instructions that a non-technical person can also understand.
Note: Perform these steps in the mentioned order along. Also, follow the prescribed software for the same.
Follow these steps to remove adware redirect:
Automatic Removal:
Use Malware Crusher to remove the "adware".
'Malware Crusher': is one of the best and most commonly used anti-malware software for Windows (obviously for 100 good reasons). Almost costing you nothing in comparison to other anti-malware software's, this tool is capable of removing various kind of mishaps on your machine.
Important: Malware Crusher is free and is recommended as the most impactful tool when it comes to fighting against malware.
Follow the mentioned steps to scan and remove "adware" and other malicious programs from your computer completely.
'Download' Malware Crusher by clicking on the link given below.
'Click to Download-Malware Crusher'
This link will open a new tab from where you can download Malware Crusher.
Now install the downloaded Malware Crusher setup by double-clicking on the downloaded file.
1. Install Malware Crusher
Install Malware Crusher setup. Once the installation process is complete, it will start downloading and installing the updates from the server.
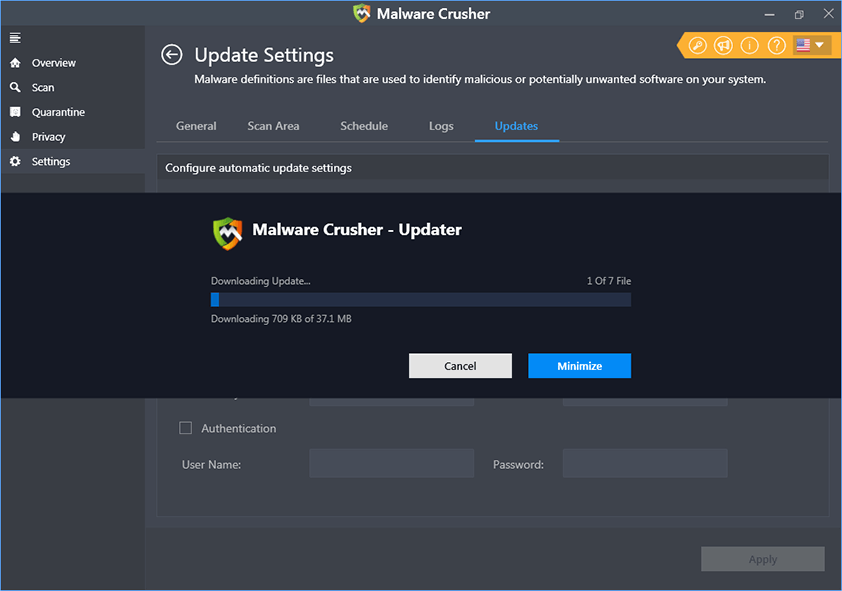
2. Let Scan Run
Once the update is finished, it will start scanning your computer from the detection of "adware" and other malicious programs.
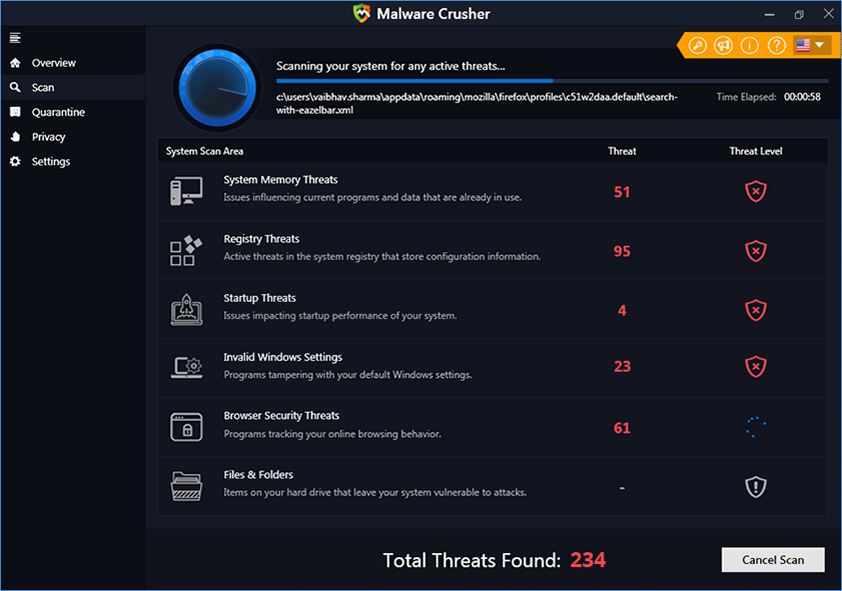
3. View & Remove The Detected Threats
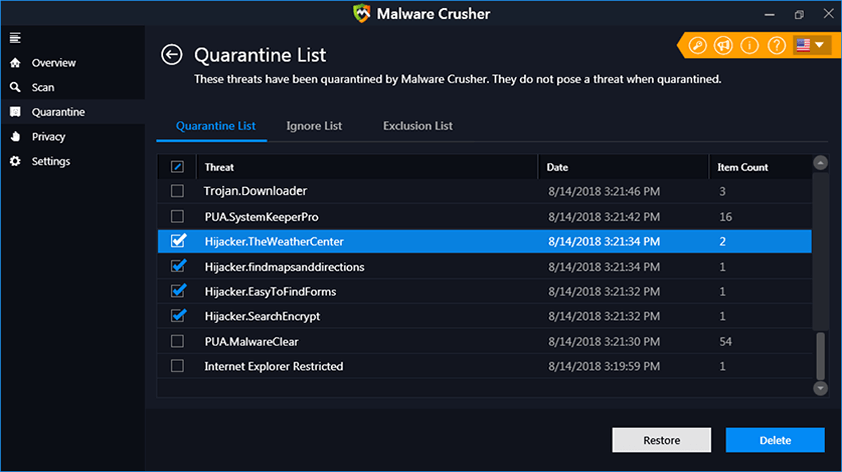
Once the scan is completed the found threats will appear on your screen as shown below. You can also view the log of the detected items.
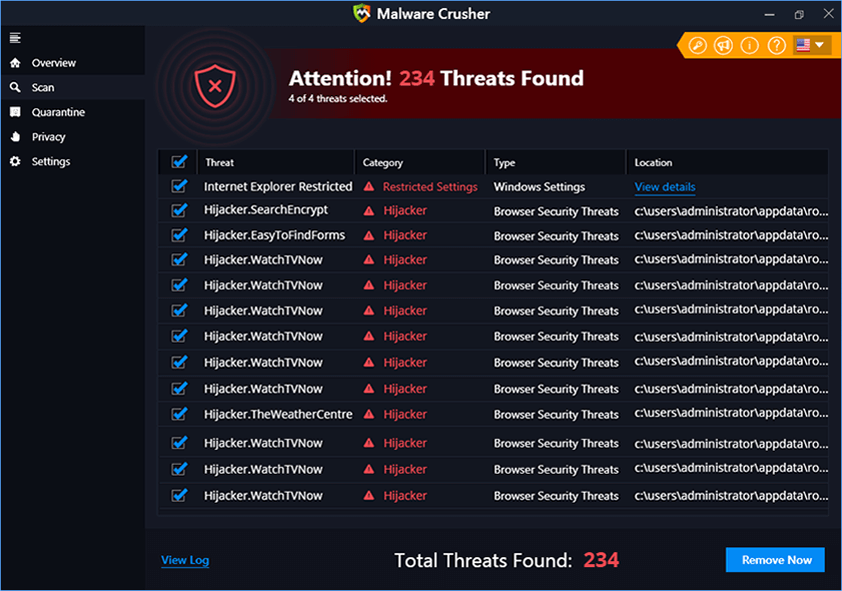
Click on the Remove Now button to get rid of all the malicious programs.
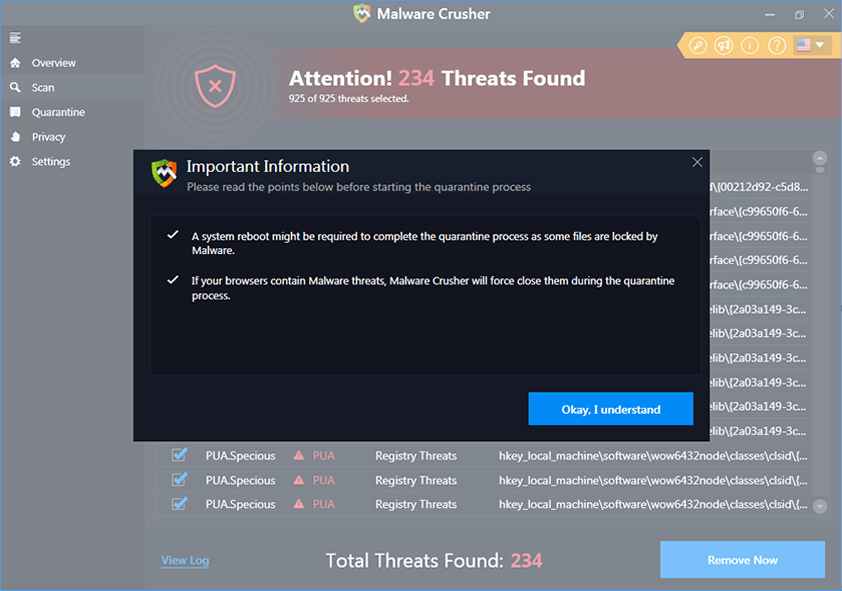
A system reboot might be required once the scan is complete. Finally, click on the Okay, I understand button to initiate the cleaning.
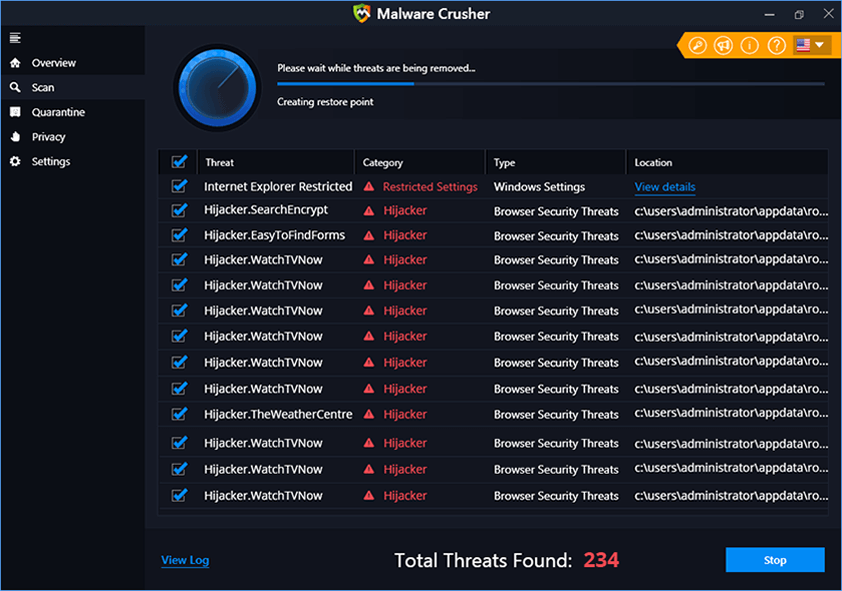
4. Creating Restore Point
Malware Crusher will create a restore point before cleaning the found threats (in case you need to reverse the actions).
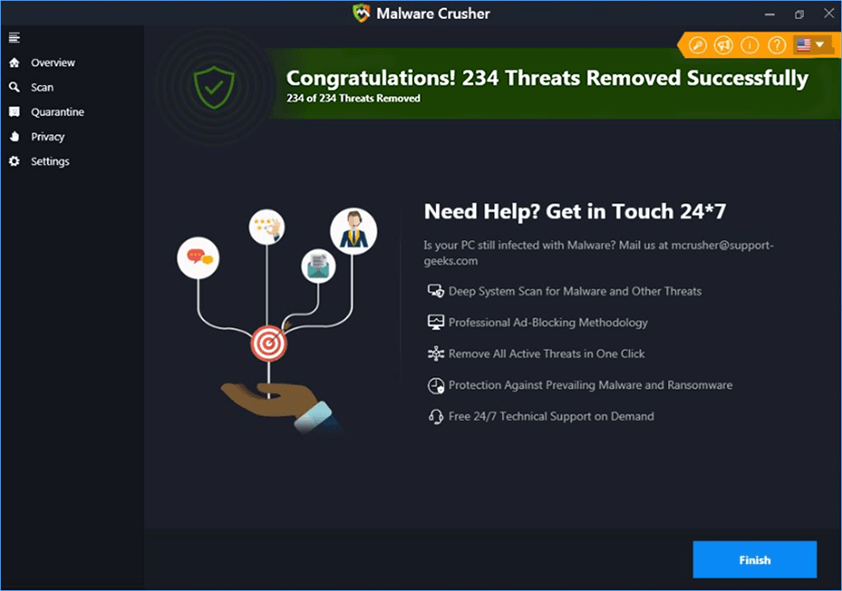
5. Congratulations! Threats Removed Successfully
Malware Crusher has successfully scanned and removed all the malicious programs on your computer. Click the Finish Button to close Malware Crusher and make sure that you scan your system once a week with Malware Crusher to Keep it Safe.
6. Restore The Removed Items.
You can restore the cleaned items by selecting desired items and clicking the Restore button. In case if you click on the Delete button the backup will be deleted.
Conclusion :
We believe now your system is free from "adware". In case, if you are still facing any issues, repeat the above-given steps to make sure your system is clean and free of infections.
Tips to Prevent virus and malware from Infecting Your System:
- Enable your popup blocker: Pop-ups and ads on the websites are the most adoptable tactic used by cybercriminals or developers with the core intention to spread malicious programs.
So, avoid clicking uncertain sites, software offers, pop-ups etc. and Install a powerful ad- blocker for Chrome, Mozilla, and IE
- Keep your Windows Updated: To avoid such infections, we recommend that you should always keep your system updated through automatic windows update.By doing this you can keep your device free from virus.According to the survey, outdated/older versions of Windows operating system are an easy target.
- Third-party installation: Try to avoid freeware download websites as they usually install bundled of software with any installer or stub file.
- Regular Backup: Regular and periodical backup helps you to keep your data safe in case the system is infected by any kind of virus or any other infection.Thus always backup important files regularly on a cloud drive or an external hard drive.
- Always have an Anti-Virus: Precaution is better than cure. We recommend that you install an antivirus like ITL Total Security or a good Malware Removal Tool like Download Virus RemovalTool
