Why is "Pushokey.com" categorized as a Browser Hijacker?
Browser hijackers are malicious programs which enter into your computer to modify default internet and browser settings. A new search engine (with malicious add-ons/extensions) downloads into your computer to replace existing homepage so that it’ll frequently display lots of intrusive pop-up ads, fake alerts, and annoying notifications.
These advertisements are displayed by installed adware programs or through less than reputable third-party websites that are showing them to generate advertising revenue.
This will result in poor system performance, slow response time as ads would be the priority, which will result in slow internet speed.
As you are here reading this article, we can only assume that you have been frequently redirected to “Pushokey.com" by your web browser and that you want to know more about it.
As the article advances, you will come to know how to remove “Pushokey.com" from a web browser and also the reasons behind it being categorized as malicious.
What is "Pushokey.com” pop-up ad?
“Pushokey.com" is nothing more than a browser hijacker or you can also call it a backdoor for other malware and threats.
This redirect will change the default homepage and search engine for your web browser to http://Pushokey.com.
This "Browser Hijacker" was installed on your PC with a freeware software with an end-goal to authorize the installation of "adware," a malicious program, and it leaves no clue to the user about the existence of malware in their device.
A web browser will display fake update alerts, coupon offers, ad banner, and pop-up ads from “Pushokey.com" when it is infected with adware and you will also face frequent redirects to its malicious portal.
With each click on pop-up ads, there are high chances that the cyber attackers are earning money via PPC and also injecting viruses and malware on the system.
These pop-ups and annoying notifications are the results of well-targeted open source adware which at present seems to have no end!
The redirects and ad pop-ups are considered as an attack on a user’s browsing experience.
Besides, the ad-supported software can be used to accumulate a wide variety of personal and sensitive information such as IP addresses, banking details, password, and login credentials.
This personal information, later, may be sold to third parties which can lead to serious privacy violations, financial loss or even theft.
The Purpose
Without the user's consent or knowledge, browser hijackers such as Pushokey.com change the browser settings or modify the internet browsing settings. They are a type of malware which ultimately aims at harming and infecting the machine.
The Common Symptoms:
- Fake alerts, notifications, and pop-ups to update your system.
- The built-in search box changes to 'Pushokey.com' Search page (http://Pushokey.com).
- New tabs open in browser to display ads, pop-up or search results would always end up with displaying online advertisement banners.
- Via " Pushokey.com " browser redirects to the third party or unsecured websites.
- It also leads to irrelevant web search redirections and remarkably affects your web browsing experience.
- Automatic download of executable files from a third party and untrustworthy websites.

Things to Remember:
- Always pay attention before installing software as it comes with additional installs (optional) such as adware.
- Watch out carefully when you agree to install.
- Always opt for custom installation and deselect everything that doesn’t appear to be familiar. Especially, an optional software that you never intended to download.
- Do not install any software that you don’t trust.
The instructions given below are purely for the Windows computer users.
Information
As there are a lot of steps mentioned along with some programs, this malware removal guide may look a bit immense. This guide is detailed just to provide a clear and easy brief about the instructions that a non-technical person can also understand.
Note: Perform these steps in the mentioned order along. Also, follow the prescribed software for the same.
REMOVAL STEP 1:
Follow the Best steps to delete Pushokey.com from Google Chrome and Mozilla Firefox.
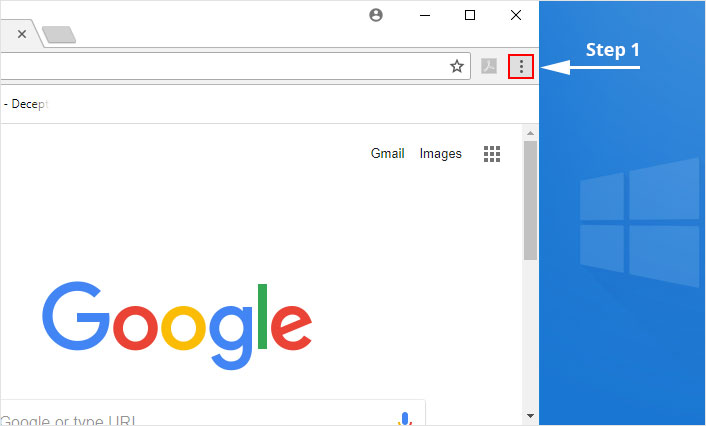
1. Click on the Customize and control menu icon at the top right corner of Google Chrome.
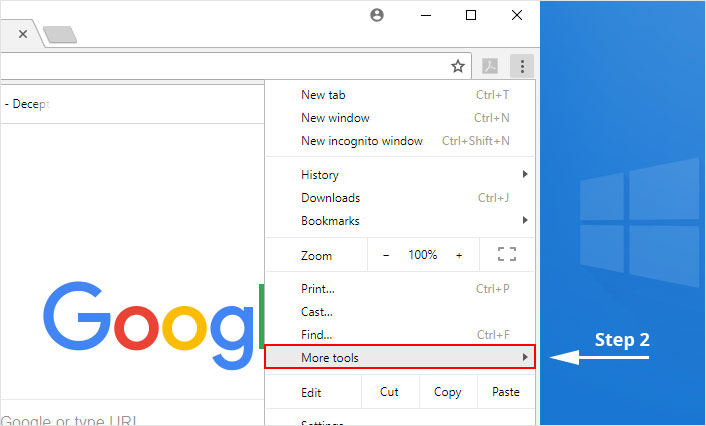
2. Select "More tools" from the menu.
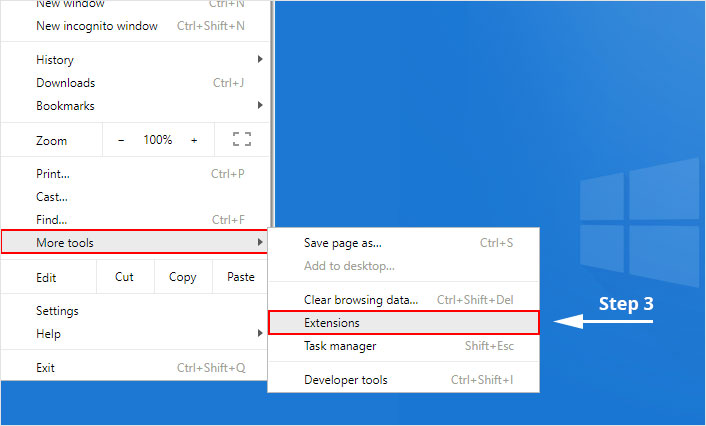
3. Select "Extensions" from the side menu.
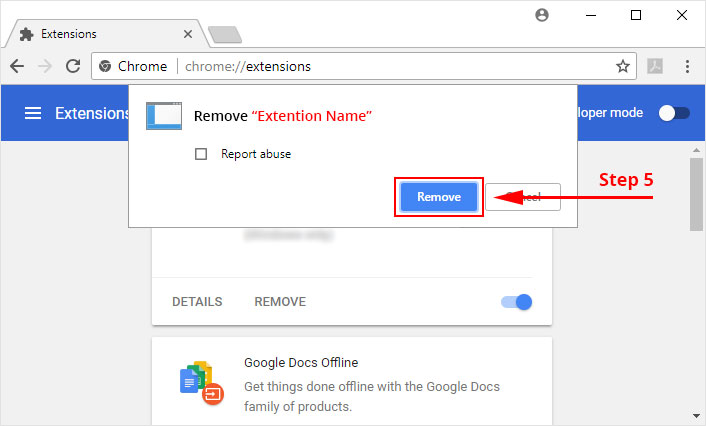
4. Click the remove button next to the extension you wish to remove.
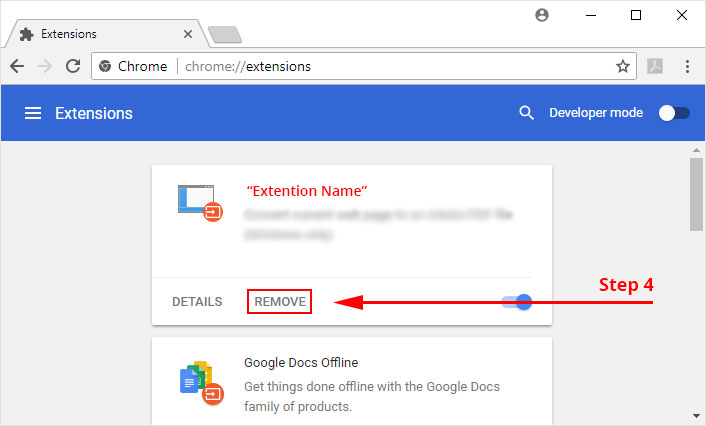
5. It will confirm again, click “remove” and the extension is finally out of the system.
Now that we have successfully eliminated the malicious browser extension, we need to create a robust firewall to avoid any such thing that makes our system and privacy vulnerable to various online threats.
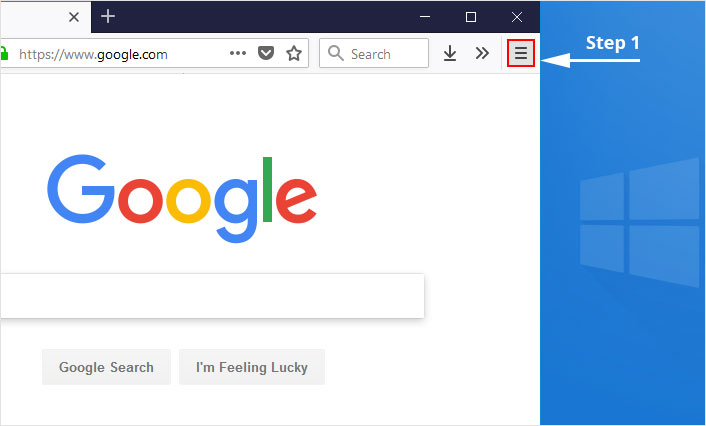
1. Click on the “menu” button at the top right corner.
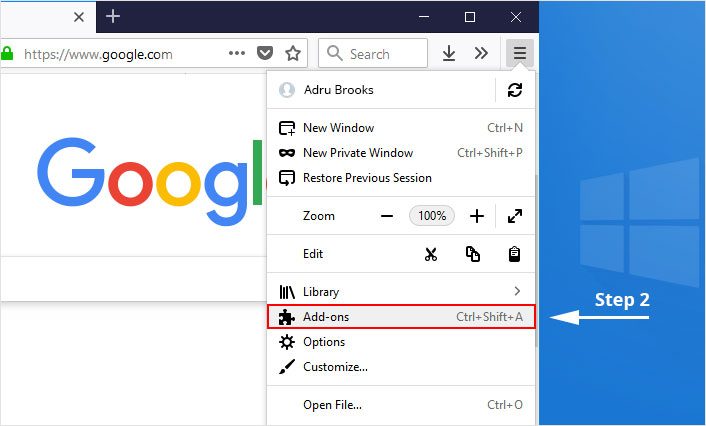
2. Select “Add-ons” from the menu.
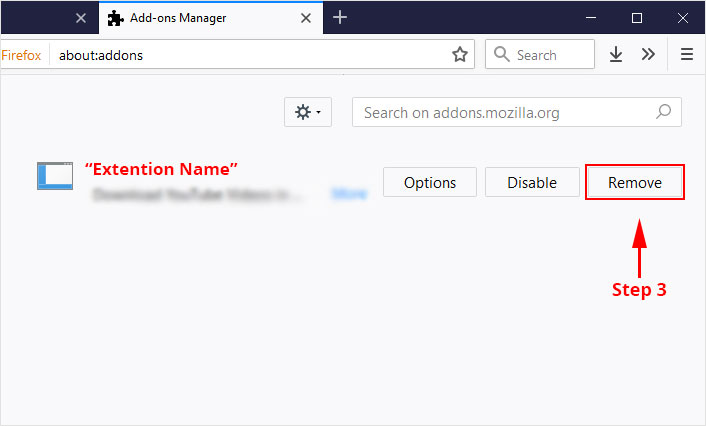
3. Click the “Remove” button next to the extension you wish to get rid of.
Now that we have successfully eliminated the malicious browser extension, we need to create a robust firewall to avoid any such thing that makes our system and privacy vulnerable to various online threats.
Make Sure: Read all the given instructions carefully. There are malicious programs which may try to hope in which you may not notice.
REMOVAL STEP 2:
Use Malware Crusher to remove the Pushokey.com browser hijacker.
Malware Crusher is one of the best and most commonly used anti-malware software for Windows (obviously for 100 good reasons). Almost costing you nothing in comparison to other anti-malware software's, this tool is capable of removing various kind of mishaps on your machine.
Important: Malware Crusher is free and is recommended as the most impactful tool when it comes to fighting against malware.
Follow the mentioned steps to scan and remove Pushokey.com and other malicious programs from your computer completely.
'Download' Malware Crusher by clicking on the link given below.
'Click to Download-Malware Crusher'
This link will open a new tab from where you can download Malware Crusher.
Now install the downloaded Malware Crusher setup by double-clicking on the downloaded file.
1. Install Malware Crusher
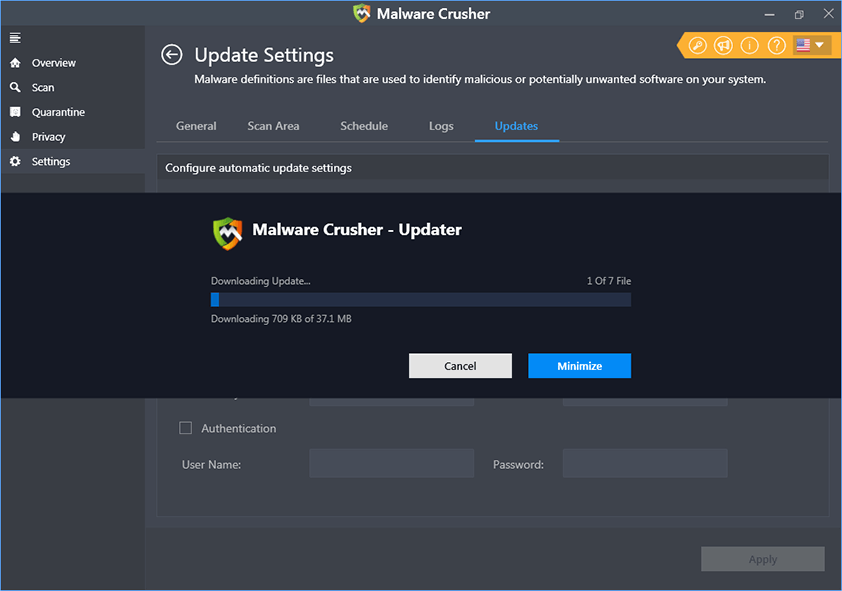
Install Malware Crusher setup. Once the installation process is complete, it will start downloading and installing the updates from the server.
2. Let Scan Run
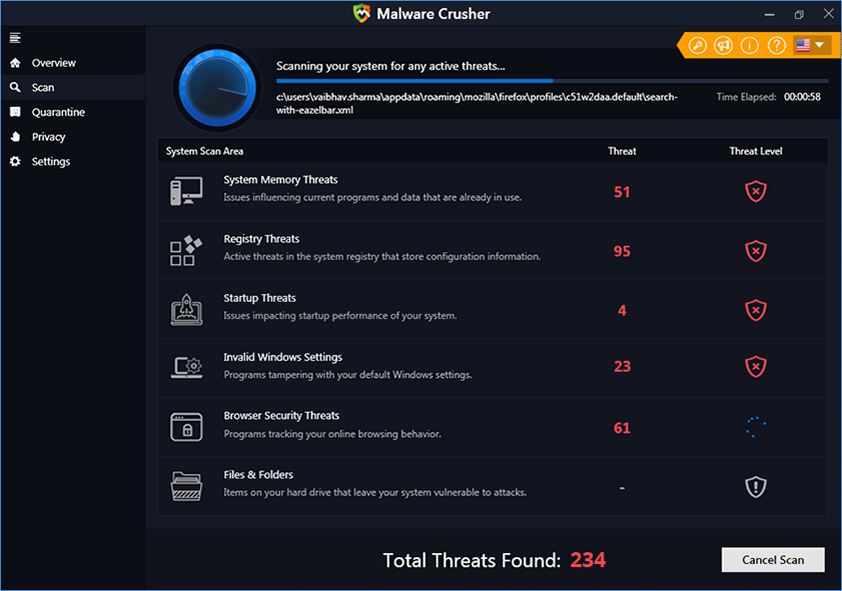
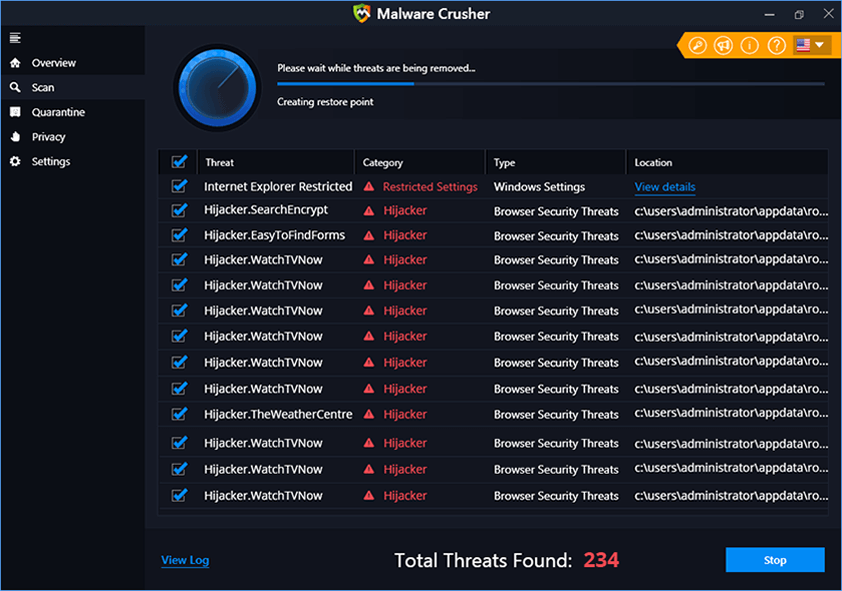
Once the update is finished, it will start scanning your computer from the detection of WebDiscover and other malicious programs.
3. View & Remove The Detected Threats
Once the scan is completed the found threats will appear on your screen as shown below. You can also view the log of the detected items.
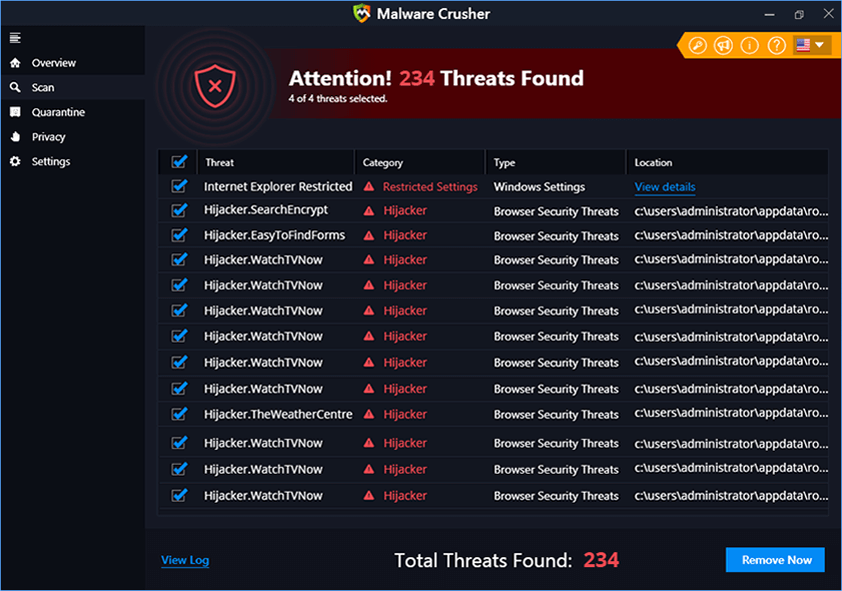
Click on the Remove Now button to get rid of all the malicious programs.
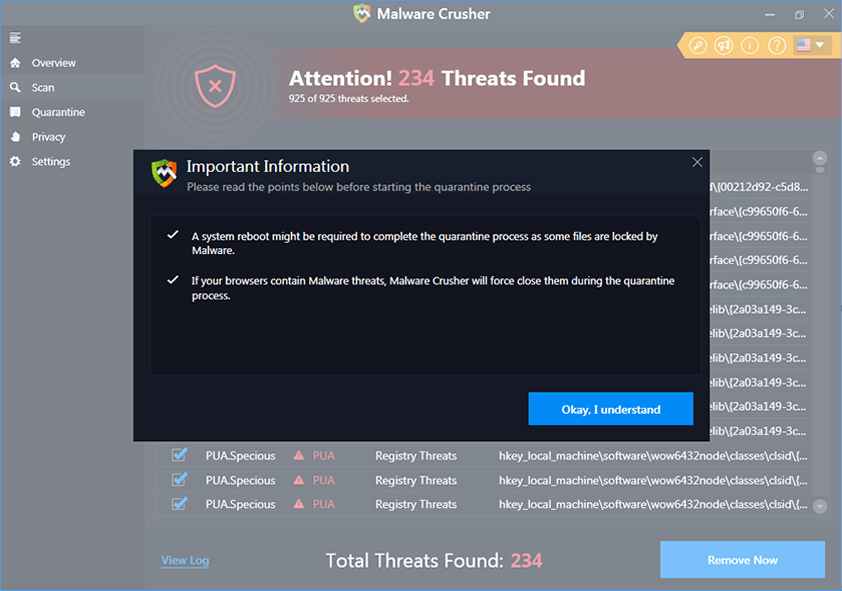
A system reboot might be required once the scan is complete. Finally, click on the Okay, I understand button to initiate the cleaning.
4. Creating Restore Point
Malware Crusher will create a restore point before cleaning the found threats (in case you need to reverse the actions).
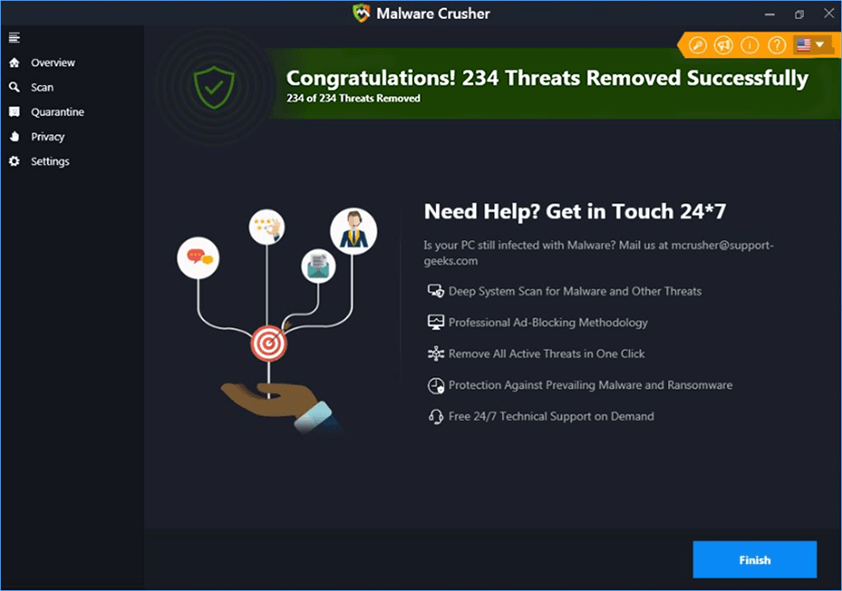
5. Congratulations! Threats Removed Successfully
Malware Crusher has successfully scanned and removed all the malicious programs on your computer. Click the Finish Button to close Malware Crusher and make sure that you scan your system once a week with Malware Crusher to Keep it Safe.
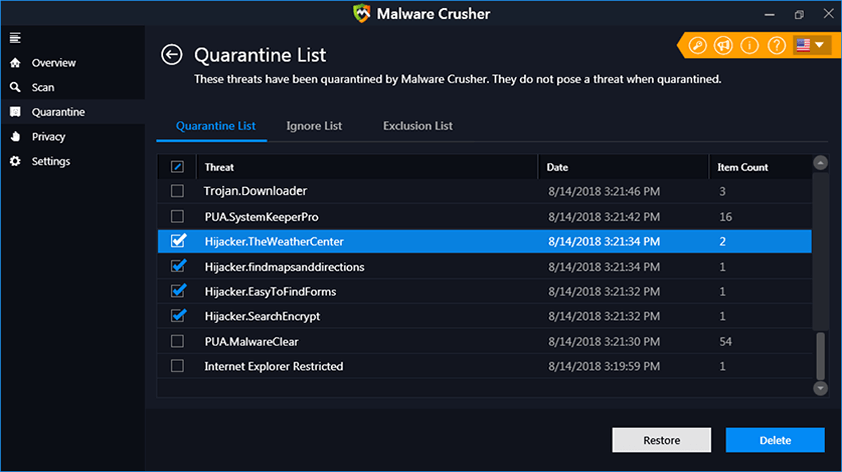
6. Restore The Removed Items.
You can restore the cleaned items by selecting desired items and clicking the Restore button. In case if you click on the Delete button the backup will be deleted.
Conclusion :
We believe now your system is free from “ Pushokey.com ” browser hijacker. In case, if you are still facing any security threat, repeat the above-given steps to make sure your system is clean and free of infections.

INSIGHT
What is a Browser Hijacker?
A malware program that modified the web browser without the permission of a user is known as a Browser Hijacker. It changes the browser settings and redirects the user to some other unintended websites. These websites are usually are infectious and malicious. Hence, browser hijacking is pursued through a browser hijacker.
Key Points
- Always pay attention while installing software as it comes with additional installs(optional) such as Name of hijacker browser hijacker.
- Watch out carefully when you agree to install.
- Opt for custom installation always and deselect everything that doesn't appear to be familiar. Especially, an optional software that you never intended to download.
- Do not install any software that you don't trust
Note*We always recommend you to use Malware Crusher to get rid of Browser Hijacker
Tips to Prevent virus and malware from Infecting Your System:
- Enable your popup blocker: Pop-ups and ads on the websites are the most adoptable tactic used by cybercriminals or developers with the core intention to spread malicious programs.
So, avoid clicking uncertain sites, software offers, pop-ups etc. and Install a powerful ad- blocker for Chrome, Mozilla, and IE
- Keep your Windows Updated: To avoid such infections, we recommend that you should always keep your system updated through automatic windows update.By doing this you can keep your device free from virus.According to the survey, outdated/older versions of Windows operating system are an easy target.
- Third-party installation: Try to avoid freeware download websites as they usually install bundled of software with any installer or stub file.
- Regular Backup: Regular and periodical backup helps you to keep your data safe in case the system is infected by any kind of virus or any other infection.Thus always backup important files regularly on a cloud drive or an external hard drive.
- Always have an Anti-Virus: Precaution is better than cure. We recommend that you install an antivirus like ITL Total Security or a good Malware Removal Tool like Download Virus RemovalTool
