SHUTUPANDDANCE Ransomware Overview
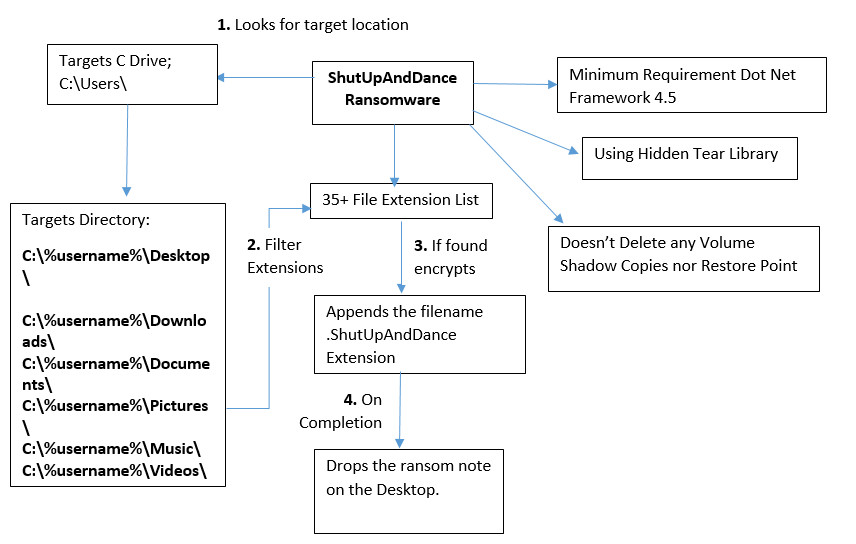
SHUTUPANDDANCE Ransom is a part of the ransomware family, found by the security researcher; it encrypts the victim's machine by using AES Encryption method.
It appends the filename of the affected file by adding .SHUTUPANDDANCE extension in the last. It Only targets the C Drive with specific folder list along with more than 35+ file extensions.
This ransomware using Hidden Tear Library which is easily available on GitHub.
It drops the ransom note on the desktop but it doesn’t contain any ransom amount information. Ransom note contains a note in the style of the FSociety Logo with the bad actor contact information. By looking at the code it seems it contains few bugs in the code which can be easily rectified by anyone.

Get peace of mind! Get rid of malicious programs instantly
Free Checkup & fix for your PC! Get rid of malicious programs instantly!
Flow Chart
Technical Analysis of SHUTUPANDDANCE Ransomware
File Name: adobe.exe
MD5: 04D5426462DBC02BBEC38145ABC749C5
File Type: .EXE
Spread Via: Not Known Yet.
Detail Description of SHUTUPANDDANCE Ransomware with Screenshots
Static Analysis
This ransomware has minimum requirement Dot Net Framework 4.5
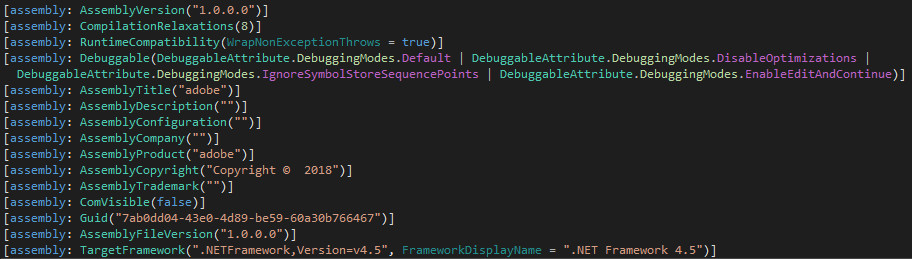
Figure 1 Assembly Information
This ransomware contains the following PDB information:
PDB: "C:\Users\Elprofesor\Desktop\virus\Hidden-tear-2.0-master\hidden-tear\hidden-tear\obj\Debug\adobe.pdb"
This ransomware gathers the Username, Computer Name and targets the User Directory C:\Users; While the ransomware is running in the background it appends the affected filename with .ShutUpAndDance Extension.
This ransomware using the Hidden Tear Library which is easily available on the GitHub. As shown below this ransomware is using AES Encryption Method to encrypt the files.
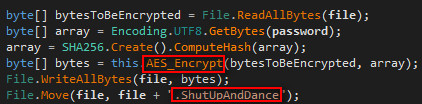
Figure 2 AES Encryption
As shown below, as per the code this ransomware is creating a random password based on predefined string and a fixed length of 15 for encrypting files and move the ransomware to a specific location with .ShutUpAndDance extension.
Thereupon, this ransomware starts encrypting the folder based on their specific target directory, extension list, and password.
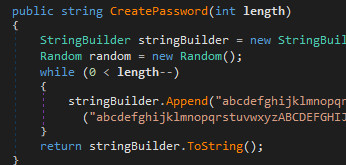
Figure 3 Random Password
As shown below, as per the code this ransomware is using specific password based on a predefined string (“Amir12345) and move the ransomware to a specific location with .ShutUpAndDance extension.
Thereupon, this ransomware starts encrypting the folder based on their specific target directory, extension list and also drops the ransom note at Desktop location.
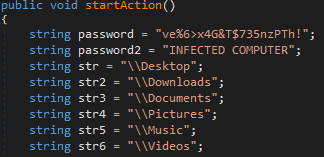
Figure 4 Specific Password & Target Directory
As shown above, this ransomware targets following folders Desktop, Downloads, Documents, Pictures, Music & Videos.
As shown below, this ransomware encrypts the files based on the extension list. It has more than 35+ file extensions list.
".doc",".docx",".xls",".index",".pdf",".zip",".rar",".css",".lnk",".xlsx",".ppt",".pptx",".odt",".jpg",".bmp",".png", ".csv",".sql",".mdb",".php",".asp",".aspx",".html",".xml",".psd",".bk",".mp3",".mp4",".wav",".wma",".avi", ".divx",".mkv",".mpeg",".wmv",".mov",".ogg"
It searches an above extension in the target drive and encrypts it.
As per the below code, this ransomware hides its visibility from the taskbar
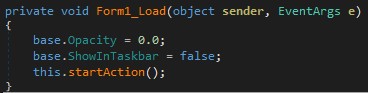
Figure 5 Not in Taskbar
This ransomware drops READ_IT.txt in C:\users\%username%\Desktop
While opening the READ_IT.txt in notepad it shows the FSOCIETY logo with the contact information
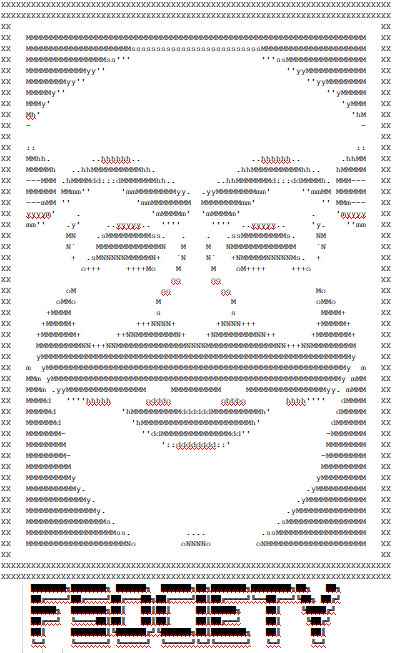
Figure 6 FSOCIETY LOGO
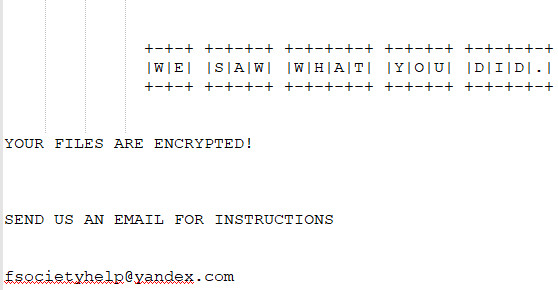
Figure 7 Ransom Note
Once the files have encrypted this ransomware it appends the filename by adding .SHUTUPANDDANCE extension in the last.
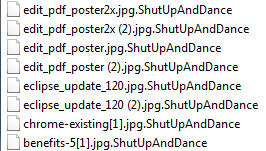
Figure 8 ShutUpAndDance File Extension
By looking at this ransomware code and behavior process it seems that’s it currently in development. Due to currently under development, this ransomware doesn’t delete Volume Shadow Copies from the system nor it deletes the System Restore Point.
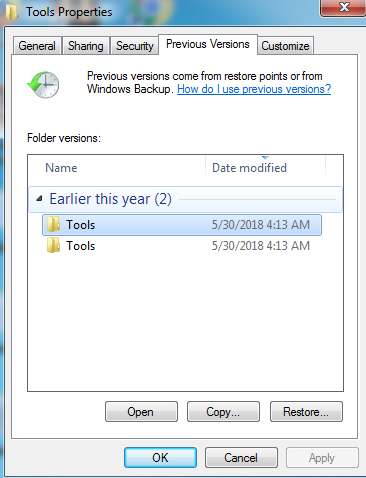
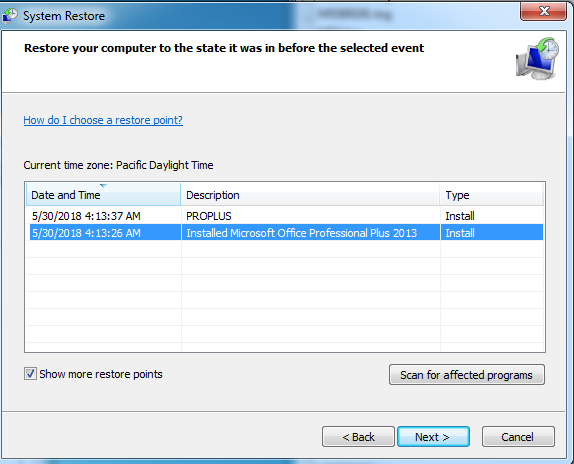
Figure 9 Restore Point
IOC’s
Hash
04D5426462DBC02BBEC38145ABC749C5
Associated File Path:
C:\Users\Admin\Desktop\Read_It.txt
Associated Email Address
fsocietyhelp@yandex.com
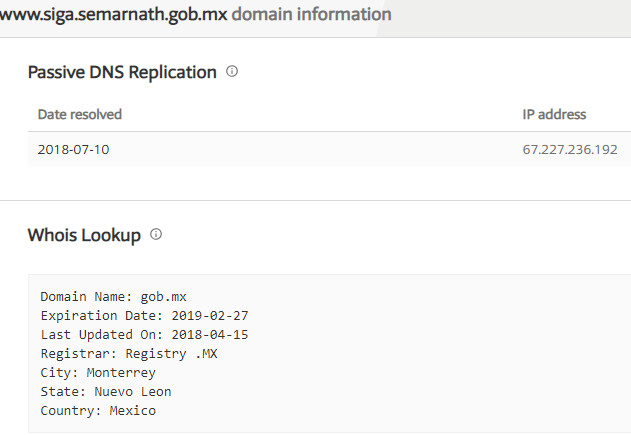
Associated C&C Server Information:
www[.]siga[.]semarnath[.]gob[.]mx
Are you worried about your PC health?
Check your PC Health for Free!
Tips to Prevent virus and malware from Infecting Your System:
- Enable your popup blocker: Pop-ups and ads on the websites are the most adoptable tactic used by cybercriminals or developers with the core intention to spread malicious programs.
So, avoid clicking uncertain sites, software offers, pop-ups etc. and Install a powerful ad- blocker for Chrome, Mozilla, and IE
- Keep your Windows Updated: To avoid such infections, we recommend that you should always keep your system updated through automatic windows update.By doing this you can keep your device free from virus.According to the survey, outdated/older versions of Windows operating system are an easy target.
- Third-party installation: Try to avoid freeware download websites as they usually install bundled of software with any installer or stub file.
- Regular Backup: Regular and periodical backup helps you to keep your data safe in case the system is infected by any kind of virus or any other infection.Thus always backup important files regularly on a cloud drive or an external hard drive.
- Always have an Anti-Virus: Precaution is better than cure. We recommend that you install an antivirus like ITL Total Security or a good Malware Removal Tool like Download Virus RemovalTool
