Prevent .Backup Ransomware Attacks To Restore Files
.Backup ransomware belonging to the family of cryptomix is a new variant of a high-risk infection. Nowadays, ransomware attacks appear from nowhere, infect a system and alter data using file encryption technique.
The classified variant enters into the system, lock your files and then demand money. The ransomware adds .Backup file extension to stored files in your system and changes the file name to some alphanumeric code name.
Since it belongs to the family of cryptomix, it encrypts files on victim’s computer, then demand payment to retrieve those files. As it is a combination of CryptXXX and CryptoWall, the developers of the ransomware always ask payment in Bitcoins.
However, the cost to recover your files back is yet unknown but would be high for someone who suffers the infection of ransomware. Thus, it is necessary to find out a legitimate method for preventing a ransomware attack.
This article walks you through a stepwise process to prevent and remove .backup ransomware from your system. Therefore, we would suggest you to follow this ransomware removal guide.
What is a .Backup Ransomware?
Like all other ransomware, it is also a file-encrypting ransomware which without your knowledge evades the system; mostly windows operating system. Once it makes a successful entry to the system, it encrypts (lock) the user’s files.
It adds the .Backup extension to the files and then would leave a ransom note demanding the ransom in the bitcoins.
For example, sample.pdf is renamed to a file name such as 3E3402E523DAEB4B558E11B9294AAAC7.BACKUP
It is an encoded file that creates due to the attack of ransomware. The new cryptomix variant ransomware encrypts file types like audio, video, image, documents, and other files and makes them inaccessible.
When a file compromises, it is quite easy to distinguish it from an unblocked file. Whenever a user tries to open the compromised file, it displays a ransom note in a file named _HELP_INSTRUCTION.TXT
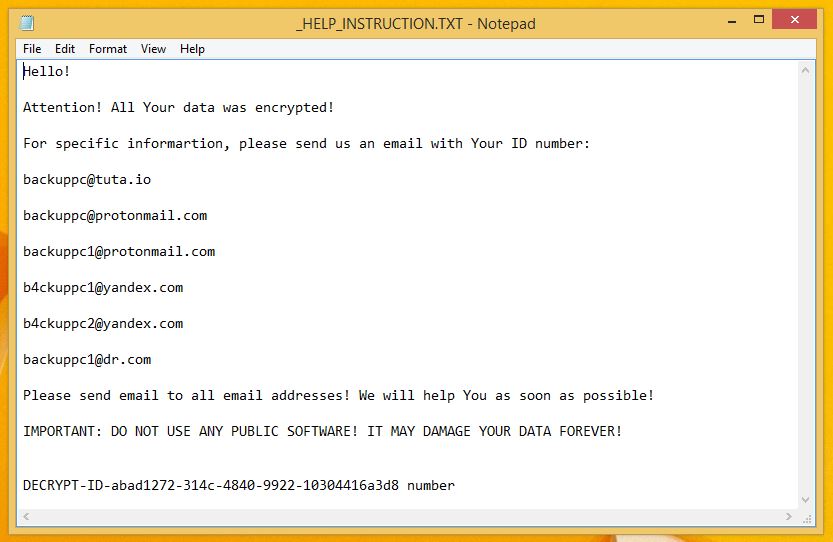
The ransom note clearly mentions that all your files are encrypted. Furthermore, to restore .backup files, you must contact cyberattackers or the developers of the ransomware.
Following are the indicated email id’s in ransom note:
- backuppc@tuta.io
- backuppc@protonmail.com
- backuppc1@protonmail.com
- b4ckuppc1@yandex.com
- b4ckuppc2@yandex.com
- backuppc1@dr.com
Should User Contact .Backup Ransomware Developers?
A ransomware from some C2 server lands on your network, inject itself in your computer and encrypts the file. It's hard to digest the fact that your files are locked and for .backup file recovery, the last option is to pay the developers.
However, there is no need to pay money to the developers of the ransomware. We recommend this because the developers won’t give you unlocked files after receiving money in their accounts. And to unlock files, they need decrypting keys which are already stored in your server.
Thus, accepting the payment option could be the biggest mistake. Rather than paying cybercriminals, we suggest you using an anti-virus or anti-malware tool like Malware Crusher against the new backup cryptomix ransomware variant.

Effects Of .Backup Ransomware
The .Backup Ransomware infected computer shows the various number of nasty irritating effects. A few are given below;
- It carries many types of cryptovirus variants which remains undetected from an ordinary antivirus tool.
- It posses keyloggers to monitor your keystrokes and sends information to hackers via servers. It also steals your sensitive and financial information.
- Copycat Look: It cheats innocent users by replicating an original application, but doesn’t contain any genuine features of the application.
- After entering into the system, it remains in the memory of the system and automatically gets executed.
- Fake scanning property: It performs bogus system scanning on the screen and shows fake results.
- Transferable: It easily duplicate itself and transmit from one infected system to another via network vulnerabilities and loopholes of security checkups.
The .Backup ransomware infections were intrusive. Moreover, the ransomware always kept an eye on your activities before blocking access to the system. Thus, it is important to delete .Backup ransomware from the system.
Cybercriminals steal information like IP address, URL’s Search, browser history, search queries, username, ID, passwords, banking information and ATM Card information via this threat.
Even though one should not pay the ransom, reports of Allscripts and Atlanta ransomware revealed a few organizations that once paid the attackers to get data back.
Did they receive their data back? The answer is yet unknown and the government of Atlanta city never gave any satisfactory answer.
What Should A User Do On .Backup Ransomware Attack?
There have been some incidents where the users were hit the second time by the same ransomware, even though they paid the attackers.
Paying criminals is a big mistake because once you fall into their trap, the chain of attack will continue unless you don’t follow a strong strategy against the ransomware attacks.
While keeping you out of the harms hand, we suggest you follow the below .backup ransomware removal guide and prevent .backup ransomware from attacking your computer.
The below guide is divided into three different parts and each step in it is fundamentally oriented to remove malicious codes of ransomware from home user’s computers.
Unblock Your Locked Computer
Being a dangerous threat, ransomware sometimes locks you out of your computer. Whenever you start the computer, it freezes on the start window. In order to get inside, you must reboot your system in safe mode. For this, you need to follow the below process;
- Start your computer and instantly press F8(Windows 7), F5(Windows 8, 8.1 and 10) repeatedly to enter Advanced Boot Options.
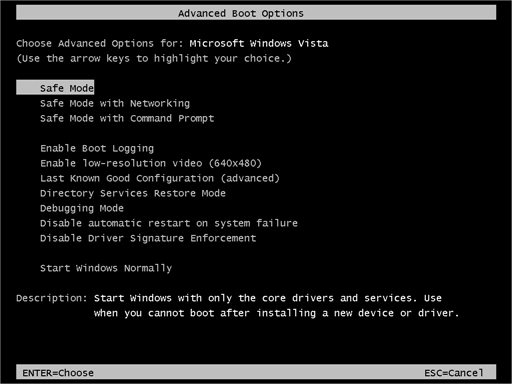
- Log on the computer as the Administrator.
- Change or remove your computer’s forgotten password in Control Panel and enable the safe mode options.
Once you have access to your computer, you can follow preventive methods to prevent the attacks of ransomware. We first will start with the automatic method.
Automatic Preventive Method
Malware Crusher is the most commonly used anti-malware tool for the Windows computer. And ransomware mostly impacts windows based computer.
Following are the removal capabilities of the tool that makes it the most watchful tool in preventing your system before the ransomware starts spreading infection;
- It’s real-time protection feature, performs a deep scan to detects malicious software, persistent threats and suspicious behaviour on your computer.
- The Quarantine feature of the tool removes all infected files from your computer. Additionally, keeps a record of all deleted malicious program and allows you to choose important programs to restore at a later time.
- Malware Crusher also creates a shield against Ransomware, Adware, Malware, Browser Hijackers, Viruses, Extensions and Trojans from entering into your system.
- The 24X7 online protective shield works as an anti-exploit technology that blocks the ransomware component before they hold files as a hostage.
- It tirelessly visits all domains, URLs and web pages to secure your online presence from fraudulent entities. Furthermore, the tool also detects the vulnerabilities of online fraudulent entities effortlessly.
- It becomes fiercer in detecting keylogging, remote connections and saves your session data from being recorded.
Malware Crusher is continuously monitoring the happenings of the cyber world. In response to the new malicious codes and javascript, the tool writes anti-malware code, diagnose ransomware and neutralize the ransomware attack. Hence, affected .backup ransomware file recovery becomes possible.
On the other hand, manual methods can’t go deep into cleaning. However, you as a user has the liberty to follow few manual preventive methods like uninstalling programs, ending the task manager process, clearing browsing history etc.

Manual Preventive Methods
- Press Ctrl + Shift + ESC together to open Task Manager. Look for suspicious files, right click on it and click End Task.
- Now, press Windows Key + R to open RUN box window. Type appwiz.cpl on it, this opens Programs and Features window.
- Select each suspicious program and uninstall it one by one. Once the uninstallation is complete, restart your computer and again redirect yourself to Programs and Features window to check whether the application is present or not.
- When convinced, press Windows key + R to open RUN box window. Type regedit on it, hit OK and then click Yes.
- Go through HKEY, HKLM, etc. files and find all suspicious files and delete them.
- You can also delete malicious extensions from your browsers like Chrome and Firefox.
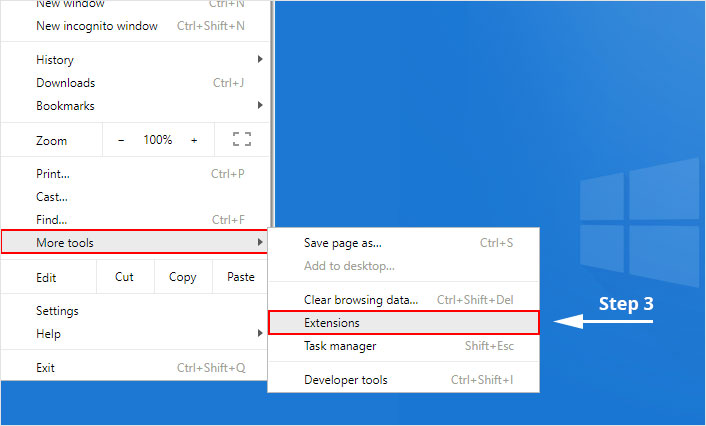
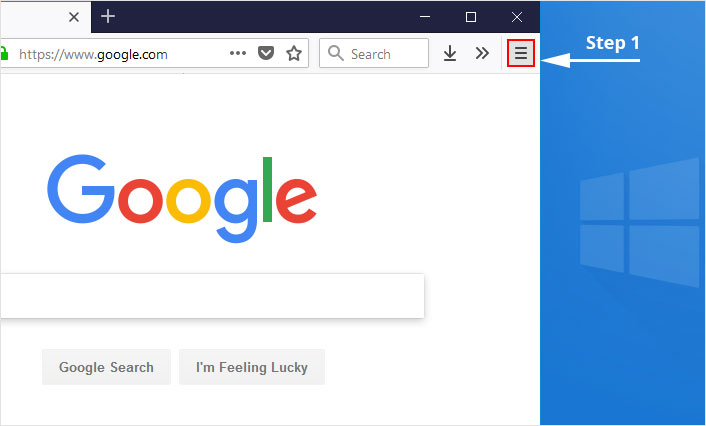
1. Click on the Customize and control menu icon at the top right corner of Google Chrome.
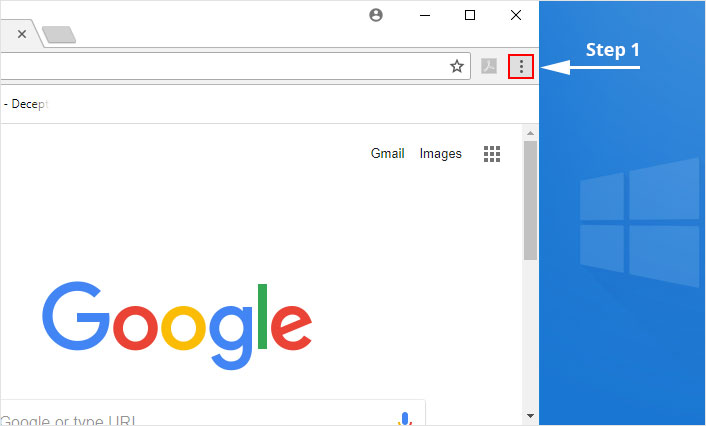
2. Select "More tools" from the menu.
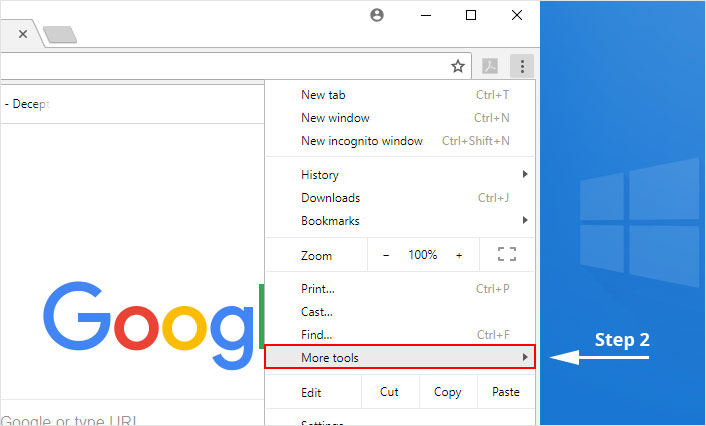
3. Select "Extensions" from the side menu.
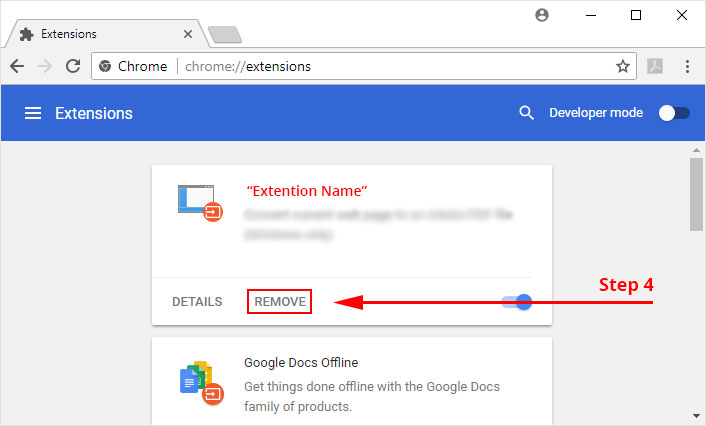
4. Click the remove button next to the extension you wish to remove.
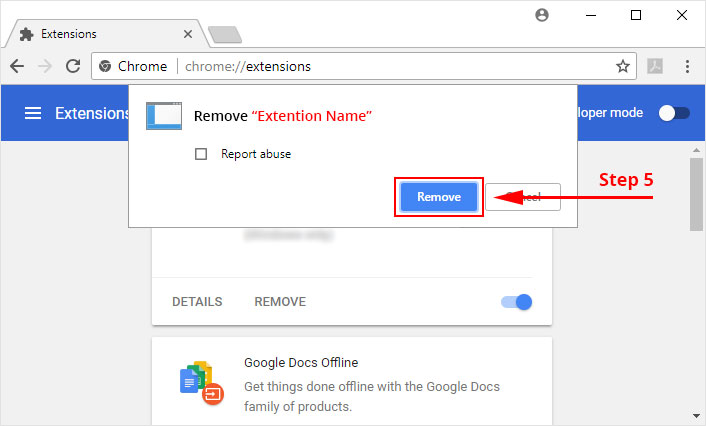
5. It will confirm again, click “remove” and the extension is finally out of the system.
Now that we have successfully eliminated the malicious browser extension, we need to create a robust firewall to avoid any such thing that makes our system and privacy vulnerable to various online threats.
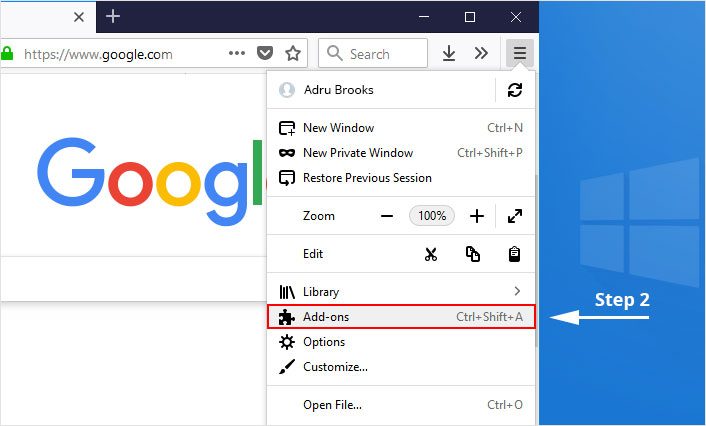
1. Click on the “menu” button at the top right corner.
2. Select “Add-ons” from the menu.
3. Click the “Remove” button next to the extension you wish to get rid of.
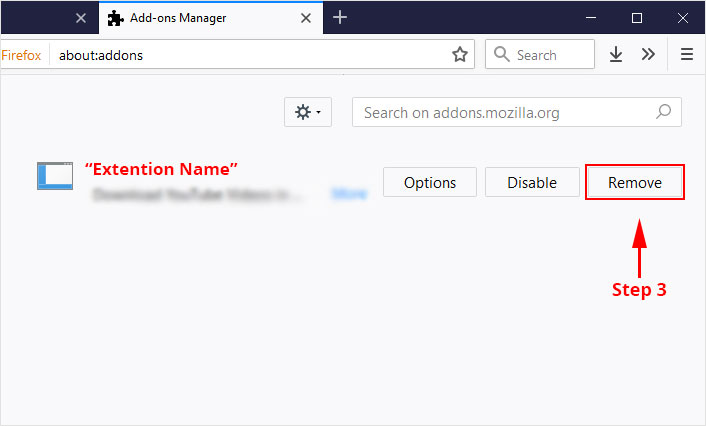
Now that we have successfully eliminated the malicious browser extension, we need to create a robust firewall to avoid any such thing that makes our system and privacy vulnerable to various online threats.
The manual methods sometimes might not work at Windows OS because finding suspicious and modified registry files in registry editors is a difficult task. On the other hand, if a useful file gets deleted, in that case, windows will stop working properly.
That’s why it is highly recommended to use an automatic tool to prevent .backup ransomware attacks on your computer. If you wish to get more news and awareness on the happenings of the cybersecurity, then keep visiting us.
Tips to Prevent virus and malware from Infecting Your System:
- Enable your popup blocker: Pop-ups and ads on the websites are the most adoptable tactic used by cybercriminals or developers with the core intention to spread malicious programs.
So, avoid clicking uncertain sites, software offers, pop-ups etc. and Install a powerful ad- blocker for Chrome, Mozilla, and IE
- Keep your Windows Updated: To avoid such infections, we recommend that you should always keep your system updated through automatic windows update.By doing this you can keep your device free from virus.According to the survey, outdated/older versions of Windows operating system are an easy target.
- Third-party installation: Try to avoid freeware download websites as they usually install bundled of software with any installer or stub file.
- Regular Backup: Regular and periodical backup helps you to keep your data safe in case the system is infected by any kind of virus or any other infection.Thus always backup important files regularly on a cloud drive or an external hard drive.
- Always have an Anti-Virus: Precaution is better than cure. We recommend that you install an antivirus like ITL Total Security or a good Malware Removal Tool like Download Virus RemovalTool
