Remove Blower@india.com Blower Ransomware
The cybersecurity investigators dubbed new ransomware-type infections as Blower ransomware that blackmails the people by corrupting their computers.
Currently, it is attacking private organizations, hospitals, colleges, universities and statutory bodies of the government in the different cities of the world.
It is an advanced and particularly harmful file encrypting Cryptovirus which infiltrate the user’s system without their knowledge. After successfully entering the system it encrypts every single data available on your hard drive and locks down the entire system.
The Blower ransomware encrypts all kinds of files and folders stored in your computer including texts, music, images, documents, pdf, backup files, etc. Instead of directly locking files, it appends .blower extension to the file name.
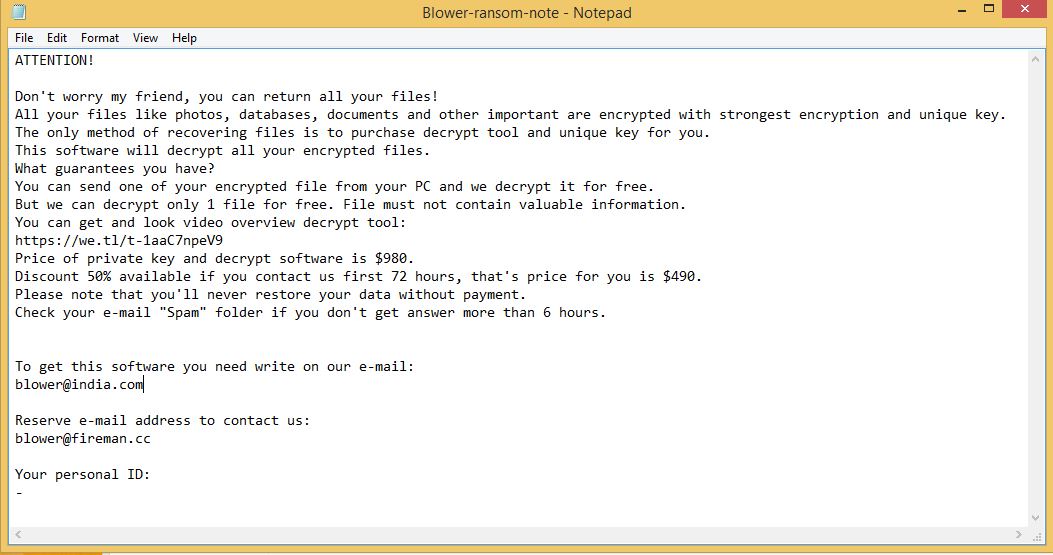
Whenever a user attempts to open any of the compromised files, a ransom note pops-up informing victims to pay ransom money in Bitcoin or another form of cryptocurrencies.
However, since you are on this page, you are already a step ahead and have a chance to remove .blower files virus from PC before it can cause more harm to your valuable data.
For removing this .blower virus ransomware from your computer, you must follow the ransomware removal guide included in this article.
What is Blower Ransomware?
Blower Ransomware is file-encrypting ransomware that secretly infiltrates the security-vulnerable system, corrupts valuable files and deletes system’s backup with the help of sophisticated cipher algorithm.
It is categorized as a dangerous file locking virus because it is enough capable to infect almost all Windows Operating System version like Windows XP, Windows7, Windows8, Windows8.1 and Windows 10.
It has been developed by cyberattackers with the sole motive to extract huge ransom money by phishing innocent users.
The primary purpose is to blackmail you by not allowing your access to the computer, use or modify the files from the computer until you pay the ransom demanded by the hackers.
Is Blower ransomware dangerous?
Once the victim contacts the developer and pays the ransom, it is hard to crack ransomware’s AES/DES cryptography technique. Finding their decryption keys is also difficult as attackers hide them in remote servers, they are the only ones who can access them.
It is recommended that one must not believe such cybercriminals because there exists no such guarantee from them helping you to recover encrypted files. Therefore, Blower ransomware is dangerous if it enters into your computer.
Blower Ransomware – Distribution Techniques
Currently, ransomware attacks are mainly campaigning against Windows computer users worldwide by using multiple attack mechanisms.
The ransomware makes entries in the Windows Registry to achieve persistence and repress processes in a Windows environment. Such entries are typically designed in a way to start the virus spontaneously every time the Windows boots up.
Here are some other distribution techniques which cybercriminals opt to inject malicious content in the targeted system:
- Spam emails
- Social clickjacking
- Pirated and free software’s
- Torrents & P2P File Sharing
- Fake advertisement’s or download portals, etc.
Cybercriminals via these threats steal information like IP address, URL’s Search, browser history, search queries, username, ID, passwords, banking information, and ATM Card information.
This personal information, later, may be sold to third parties which can lead to serious privacy violations, financial loss or even data theft.
According to the reports of the National Cyber Security Centre, the attacks from ransomware saw a gradual increase this year in 2018 and are the biggest cyberwar threats in 2019.
Hence, it is important to stop the entry and remove Blower@india.com Blower ransomware from your computer.

How to Prevent Blower Ransomware Entry In Computer?
There have been instances in the past showing the users were hit by the same ransomware for the second time, even though they have already paid the ransom amount.
From here, all we can say is if you don’t act quickly in the right way, you might not get another chance. So we suggest you follow Blower Ransomware removal guide to delete Blower ransomware that may also help you in the removal process of other malicious content. The guide is divided into two parts:
- Unlock Computer In Safe Mode
- Restore System
Temporarily Disable Blower Ransomware in safe mode using Command Prompt
If you can’t access your computer, then it might become impossible to remove Blower ransomware. However, system reboot in Safe Mode could give you entry into your computer followed by creating a system restore point.
Once you are into your computer, perform a full system scan using the antimalware tool which we have suggested at the end of this article.
Steps to be followed to enter the safe mode Win XP/Vista/7
- Click start, then shut down, then restart.
- While the computer is booting up at the very first screen start tapping F8 until you see the advanced boot options.
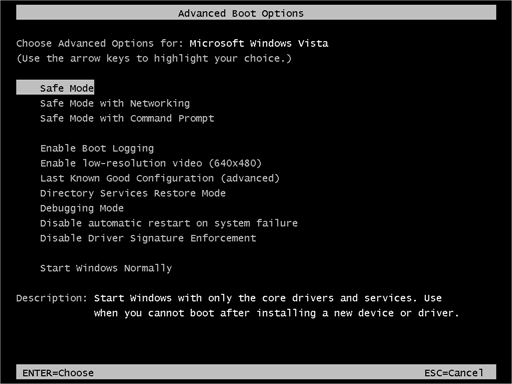
- In the advanced boot option’s, you need to select safe mode with Command prompt from the list of given options.
Steps to be followed to enter safe mode in Win 8/10
- On the windows login screen, you need to press the power option.
- Now, press and hold the shift key on the keyboard, and then click Restart.
- Now, among the list of options you need to select Troubleshoot, and then advanced options, then startup settings and finally press restart.
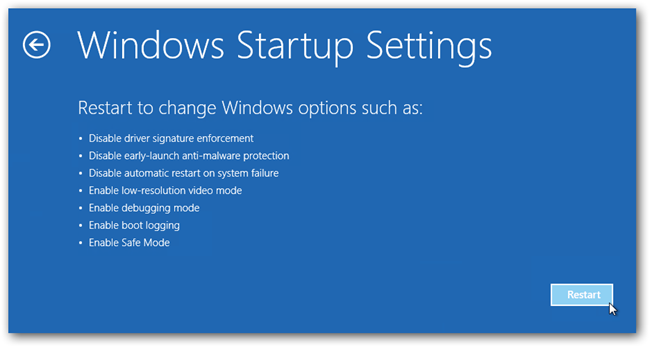
- Once your computer restarts and gives you the list of startup options you need to select Enable Safe Mode with Command prompt.
Restore System
- Once you see the command prompt windows, type in cd restore and hit enter on the keyboard.
- Now, type rstrui.exe and hit Enter again.
- Then you would see new windows, click on next over there and select a restore point that is before the date of infection.
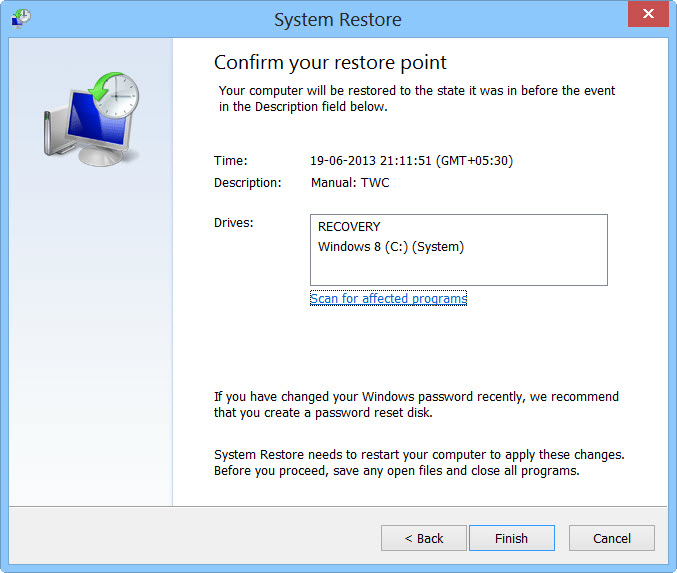
- Then, click next and followed by yes.
At present, your computer is in a state that has its file and data backed up at a safe restore point. We also suggest you make a copy of your backed up data into some external hard drive.
It is now time, to reinstall your Windows via an external source such as USB drives, CD or DVD and portable HDD devices.
While installing Windows, allocate disk space to C, D and E drive. If asked to restore any files, select the restore point and get the backed up data into the new operating system.
Your system format is complete, also your data is backed up. Now you must create a strong firewall against such malicious threats to prevent future attacks.
Cyber attackers are very advanced and had learned to gain illegal access to the computer. More than that, they make their malware more adaptable, resilient and damaging. It is impossible to stop cyberwarfare and cyberterrorism by common antivirus software.

Thus, the best preventive step is to upgrade our cyber defense systems at home and office computers with those cybersecurity tools that could delete Blower ransomware with their real-time protection feature, quarantine feature, web protection and anti-exploit technology.
If your computer doesn’t have such security software, then download ITL Total Security and Malware Crusher to prevent malware attacks on your system. Both are reputable, vigilant and robust in creating a shield 24X7 against any cyberthreat.
These tools are highly recommended if you are willing to give advanced security to your PC. Their 5-minute function could be a savior for your computer!
Tips to Prevent virus and malware from Infecting Your System:
- Enable your popup blocker: Pop-ups and ads on the websites are the most adoptable tactic used by cybercriminals or developers with the core intention to spread malicious programs.
So, avoid clicking uncertain sites, software offers, pop-ups etc. and Install a powerful ad- blocker for Chrome, Mozilla, and IE
- Keep your Windows Updated: To avoid such infections, we recommend that you should always keep your system updated through automatic windows update.By doing this you can keep your device free from virus.According to the survey, outdated/older versions of Windows operating system are an easy target.
- Third-party installation: Try to avoid freeware download websites as they usually install bundled of software with any installer or stub file.
- Regular Backup: Regular and periodical backup helps you to keep your data safe in case the system is infected by any kind of virus or any other infection.Thus always backup important files regularly on a cloud drive or an external hard drive.
- Always have an Anti-Virus: Precaution is better than cure. We recommend that you install an antivirus like ITL Total Security or a good Malware Removal Tool like Download Virus RemovalTool
