Remove Clop Ransomware from PC (+File Recovery)
The cybersecurity investigators dubbed the new variant as Clop Ransomware which belongs to a well-known Cryptomix ransomware family.
Clop ransomware is a vicious file encrypting virus which evades the security vulnerable system and encrypts (lock) the stored files by placing the .Clop extension and compels you to pay the money within some time limit for the alleged restoration of your data.
Clop virus belongs to one of the worst computer threat that makes entries in the Windows Registry to achieve persistence and could launch or repress processes in a Windows environment to stay concealed from the regular antivirus program and user.
If your computer has just become a victim of such an attack, you’re probably speculating how to deal with it and how to save your important files like work documents, backup files, archives, images, videos, and many more.
However, since you are on this page, you are already a step ahead and have a chance to delete Clop ransomware before it causes more harm to the PC especially to your valuable data.
What is Clop Ransomware?
Clop ransomware is categorized as dangerous malware because the infection can have severe outcomes, and capable of infecting almost all operating system version like Windows XP, Windows7, Windows8, Windows8.1 and Windows 10.
It is designed to modify predefined browser settings and manipulate various functionalities to run a built-in encryption module and corrupt all important files that you keep on your system and make them useless.
Clop ransomware targets 100+ files and appends .Clop extension to the end of all file names.
Whenever a user attempts to open a compromised file, it displays a ransom message informing victims of the encryption and giving instructions regarding the method to pay ransom money in Bitcoin or other cryptocurrencies.
It is recommended that you should never believe such cyber-attackers because once payment is submitted, there is no such guarantee that you would be able to recover locked files.
We suggest investing the money you are demanded to pay into some backup may be a better option because data loss wouldn’t be a problem.
Further, creators of such infections via these threats steal private data like IP address, URL’s Search, browser history, and financial information which can lead to serious privacy violations as criminals use this data for their malicious purposes.
Thus, it is important to use a successful robust Clop ransomware removal tool such as Malware Crusher which will help you in the removal of Clop ransomware and other malicious programs, saving you the struggle and time of hunting down various infected files.

Clop Ransomware – Distribution Techniques
Here are some distribution techniques which cyber crooks opt to inject malicious programs in the targeted system:
- Social Clickjacking: developers of such malevolent programs use social media platform and alluring ad banners to trick the users to click on the ads, i.e., Update your USB driver or win an iPhone.
- Spam emails: A number of harmful infections can get into your device through nasty junk attachments, and download links present in the body of the mail. These unsolicited emails usually appear to be from a reputed corporation, i.e., Banks and insurance companies.
- Bundling: The major parts of the malicious programs are installed through freeware, and in this case, the user is also responsible for authorizing the installation of such harmful software without reading the terms and conditions completely.
- Torrents & P2P File Sharing: Files shared on P2P networks and torrents have a high probability of being a carrier to such ransomware programs.
- Pornographic Websites: Adult or porn-related sites are major causes of these ransomware infections.
How to Prevent Clop Ransomware and Recover Encrypted Files
There have been occurrences in the past showing the users were hit by the same ransomware for the second time, even though they have already paid the ransom amount.
From here, all we can say is if you don’t act quickly in the right way, you might not get another chance, so we suggest you follow removal guide to eliminate the ransomware threats that may also help you in the removal process of other malicious content. The guide is divided into two parts:
- Unlock Computer In Safe Mode
- Restore System
Temporarily Disable Clop Ransomware in Safe Mode using Command Prompt
1. Steps to be followed to enter the safe mode Win XP/Vista/7
- Click start > then shut down > then restart.
- While the computer is booting up at the very first screen start tapping F8 until you see the advanced boot options.
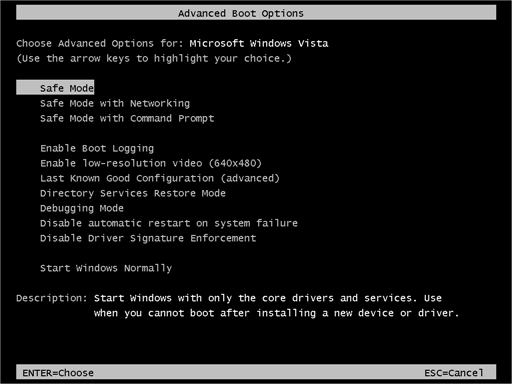
- In the advanced boot option’s, you need to select safe mode with Command prompt from the list of given options.
2. Steps to be followed to enter safe mode in Win 8/10
- On the windows login screen, you need to press the power option.
- Now, press and hold the shift key on the keyboard, and then click Restart.
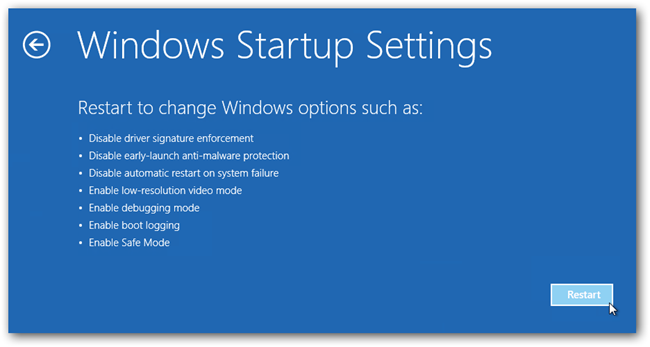
- Now, among the list of options you need to select Troubleshoot, and then advanced options, then start-up settings and finally press restart.
- Once your computer restarts and gives you the list of start-up options you need to select Enable Safe Mode with Command prompt.
3. Restore System
- Once you see the command prompt windows, type in cd restore and hit enter on the keyboard.
- Now, type rstrui.exe and hit Enter again.
- Then you would see new windows, click on next over there and select a restore point that is before the date of infection.
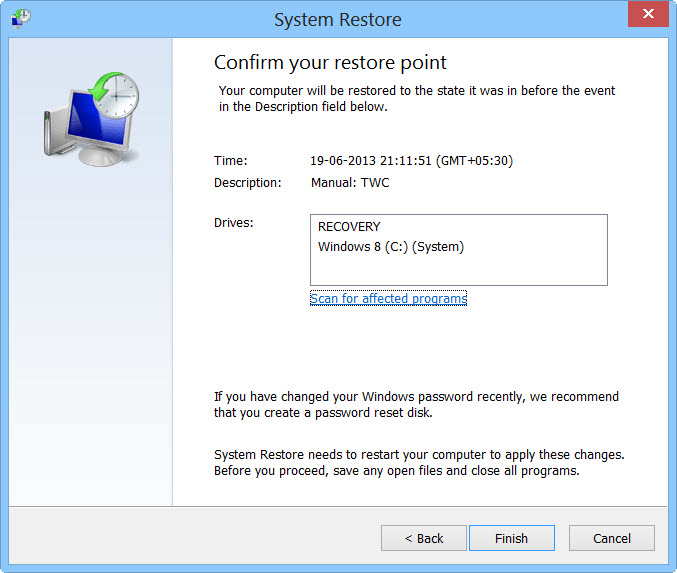
- Then, click next followed by yes.
At present, your computer is in a state that has its file and data backed up at a safe restore point. We also suggest you make a copy of backed up data into some external hard drive.
It is now time, to reinstall your Windows via an external source such as pen drive, CD or DVD.
While installing Windows, allocates disk space to C, D and E drive. If asked to restore any files, select the restore point and get the backed up data into the new operating system.
Your system format is complete; also your data is backed up. Now you must create a strong firewall against such intrusions and prevent them in the future.
Nowadays, criminals have learned to make their malware more adaptable, resilient and damaging than ever before. Common antivirus software cannot protect you from all cyber threats at the same time.
Though, we must comprehensively upgrade our cyber defense structures and processes to more effectively guard against cybersecurity risks, as well as to respond in a timely and robust manner to prevent any future intimidations.

Note* - We recommend Malware crusher and ITL Total Security, among the best reputed anti-malware software which will help you to block ransomware, hijackers, viruses, and other malware on your PC.
They are fully loaded with many useful features like Invalid Registry Cleaner, Real-Time Protection, live updates, Web Protection, and many more to protect your computer from all kinds of disarray and keep you safe always.
Tips to Prevent virus and malware from Infecting Your System:
- Enable your popup blocker: Pop-ups and ads on the websites are the most adoptable tactic used by cybercriminals or developers with the core intention to spread malicious programs.
So, avoid clicking uncertain sites, software offers, pop-ups etc. and Install a powerful ad- blocker for Chrome, Mozilla, and IE
- Keep your Windows Updated: To avoid such infections, we recommend that you should always keep your system updated through automatic windows update.By doing this you can keep your device free from virus.According to the survey, outdated/older versions of Windows operating system are an easy target.
- Third-party installation: Try to avoid freeware download websites as they usually install bundled of software with any installer or stub file.
- Regular Backup: Regular and periodical backup helps you to keep your data safe in case the system is infected by any kind of virus or any other infection.Thus always backup important files regularly on a cloud drive or an external hard drive.
- Always have an Anti-Virus: Precaution is better than cure. We recommend that you install an antivirus like ITL Total Security or a good Malware Removal Tool like Download Virus RemovalTool
