Remove .Gamma Ransomware Without Paying Money
.Gamma ransomware is a file-encrypting malware that usually gets inside the system via malicious email and process data encryption. It is a new variant of the CrySis ransomware that appends .gamma extension.
Belonging to a CrySis Family, this ransomware firstly detected in 2017 has undergone through several updates in .gamma files.
Most of the times ransomware files demand payments in Bitcoins to free your system. Unfortunately, that’s a rare case because once any ransomware enters into your system, neither you can do anything nor you can sit back and relax.
Once it enters, .gamma file extension blocks other files and encrypt them before letting you know. To fight against ransomware, you must learn to decrypt .gamma files. Ransomware after encryption creates text document files such as FilesEncrypted.txt that are known as a ransom note.
.Gamma Ransomware Encrypted Files Messages
- All your data is locked! Do you want to return? Write email {e-mail address}
- All your files are encrypted! due to security problems in your PC. to restore, write an e-mail at glynnaddey@aol.com.
- You have to pay for ..gamma ransomware decryptor files in Bitcoins. The price depends on how early you write to us. After payment is done, we will send you the ..gamma ransomware decrypt tool to help you get your files back.
- Free decryption as a guarantee. Before paying, send us 5 files for free decryption. The size must be less than 10Mb (non-archived), should not contain any valuable information. (databases, backups, large excel sheets, etc.)
- Attention! Do not rename or edit encrypted files.
- Don’t decrypt your data by using any malware removal tool as it might cause permanent data loss.
- Pay ransom to recover encrypted files rather than using permanent removal tools.
Almost all the file messages force the victim to contact ransom and to pay the ransom. On the other hand, you should get warned from these messages. Latest versions of the ransomware weren’t decryptable manually; however, there is a chance to restore your encrypted files by decrypting .gamma files.
Overall the encryption methods remain same in almost all ransomware but there exist few decryption keys that decrypt the victim's files. It sounds bit fishy and odd, however, we recommend you Malware Crusher to remove .gamma ransomware permanently from your system.

Victims reports on the ransomware
Recently, we received information from a victim of .gamma attack. He was asked to pay 2000 dollars for the data recovery. However, after spending 500 dollars, he didn’t receive any decryption key.
Warning: The ransomware frauds with their victims and extort money from them. Instead of giving keys, they demand more money and leaves you with those same locked files.
Therefore, wasting your time and money on deals with cybercriminals is not the right way to solve the ransomware infection. The safest method is to follow a few prevention steps and a removal guide that never allows such ransomware to enter again into your system.
Impacts Of .gamma Ransomware
It easily spreads through spam emails, websites, peer to peer file sharing, freeware, cracked or pirated software and social hijacking. It degrades the computer performance and compels you to pay money for your own files within some time limit.
Once victimized, the ransomware attacks your system and web browsers settings in the following ways;
- Tamper system files and Windows registry editors
- Delete back up files
- Disable system recovery files
- Run system automatically on system boot
- Fake software update notification (which a user install thinking it as a genuine update)
- Cause software bugs/flaws
- Installation of rogue applications via third-party
- Changes windows administrator permissions
- Makes your computer to host crypto mining and cryptojacking
Cybercriminals via such threat infections steal information like IP address, URL’s Search, browser history, search queries, username, ID, passwords, banking information and ATM Card information.
Though ransomware removal is a complicated task, it can be completed by removing .gamma file extension on your own. While keeping you out of the harms hand, we suggest you follow the below .gamma ransomware removal guide and prevent .gamma ransomware from attacking your computer.
The below guide is divided into three different parts and each step in it is fundamentally oriented to remove malicious codes of ransomware from home user’s computers.
Get Entry Into Your System Via Safe Mode
- Start your computer and instantly press F8(Windows 7), F5(Windows 8, 8.1 and 10) repeatedly to enter Advanced Boot Options.
- Log on the computer as the Administrator.
- Change or remove your computer’s forgotten password in Control Panel and enable the safe mode options.
After entering, we need to create a strong firewall to fight against such intrusive threat. For this, you must follow the automatic preventive tool guide.
Automatic Preventive Method
Malware Crusher is one of those with which you can prevent .gamma CrySis ransomware before it collects your information and money.
It can be your permanent ally due to its following removal capabilities;
- It’s real-time protection feature, performs a deep scan to detects malicious software, persistent threats and suspicious behaviour on your computer.
- The Quarantine feature of the tool removes all infected files from your computer. Additionally, keeps a record of all deleted malicious program and allows you to choose important programs to restore at a later time.
- Malware Crusher also creates a shield against Ransomware, Adware, Malware, Browser Hijackers, Viruses, Extensions and Trojans from entering into your system.
- The 24X7 online protective shield works as an anti-exploit technology that blocks the ransomware component before they hold files as a hostage.
- It tirelessly visits all domains, URLs and web pages to secure your online presence from fraudulent entities. Furthermore, the tool also detects the vulnerabilities of online fraudulent entities effortlessly.
- It becomes fiercer in detecting keylogging, remote connections and saves your session data from being recorded.
Malware Crusher continuously monitors incidents of the cyber world and accordingly rewrites anti-malware code, diagnose ransomware and neutralize the attack in your system. Hence, affected .gamma ransomware file recovery becomes possible.
On the other hand, manual methods can’t go deep into cleaning. However, you as a user has the liberty to follow few manual preventive methods like uninstalling programs, ending the task manager process, clearing browsing history etc.

Manual Preventive Methods
- Press Ctrl + Shift + ESC together to open Task Manager. Look for suspicious files, right click on it and click End Task.
- Now, press Windows Key + R to open RUN box window. Type appwiz.cpl on it, this opens Programs and Features window.
- Select each suspicious program and uninstall it one by one. Once the uninstallation is complete, restart your computer and again redirect yourself to Programs and Features window to check whether the application is present or not.
- When convinced, press Windows key + R to open RUN box window. Type regedit on it, hit OK and then click Yes.
- Go through HKEY, HKLM, etc. files and find all suspicious files and delete them.
- You can also delete malicious extensions from your browsers like Chrome and Firefox.
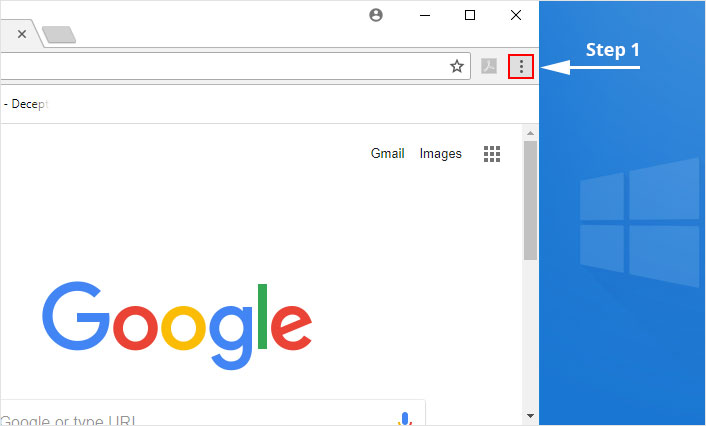
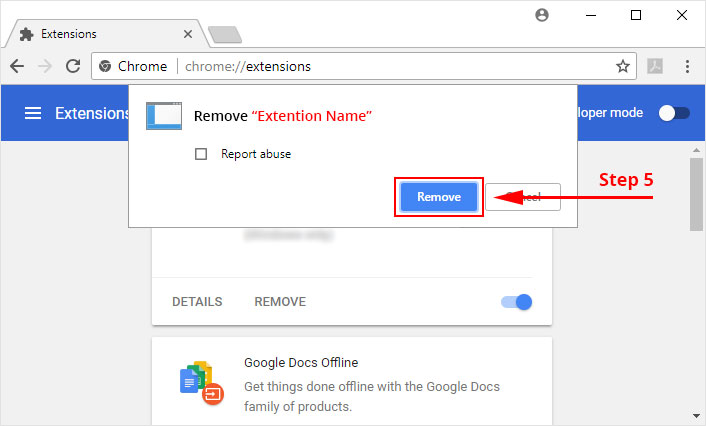
1. Click on the Customize and control menu icon at the top right corner of Google Chrome.
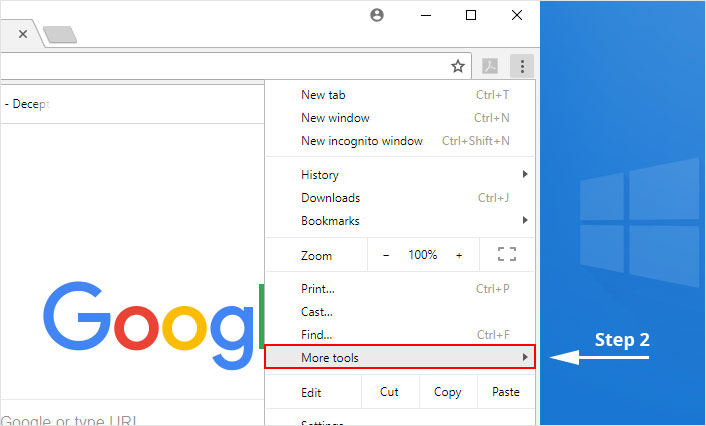
2. Select "More tools" from the menu.
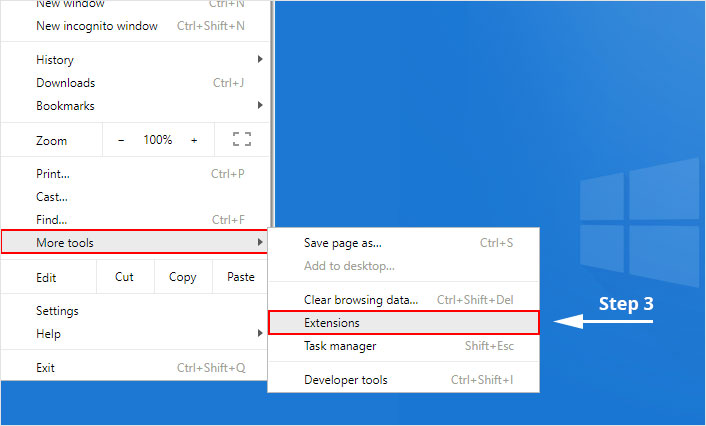
3. Select "Extensions" from the side menu.
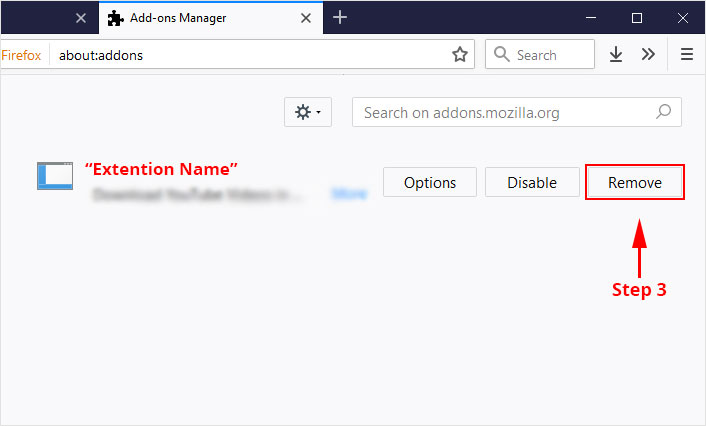
4. Click the remove button next to the extension you wish to remove.
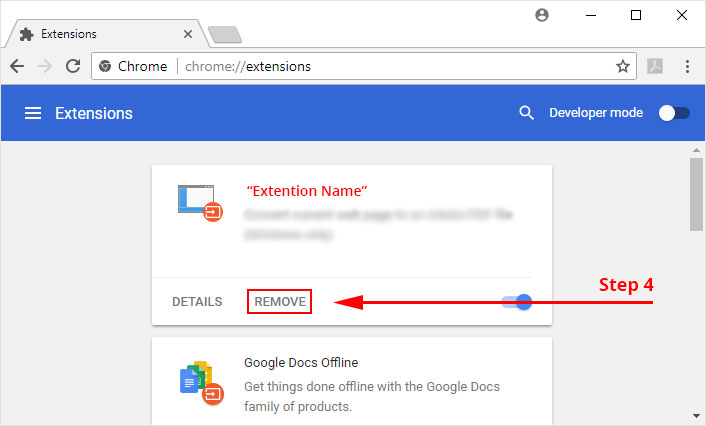
5. It will confirm again, click “remove” and the extension is finally out of the system.
Now that we have successfully eliminated the malicious browser extension, we need to create a robust firewall to avoid any such thing that makes our system and privacy vulnerable to various online threats.
1. Click on the “menu” button at the top right corner.
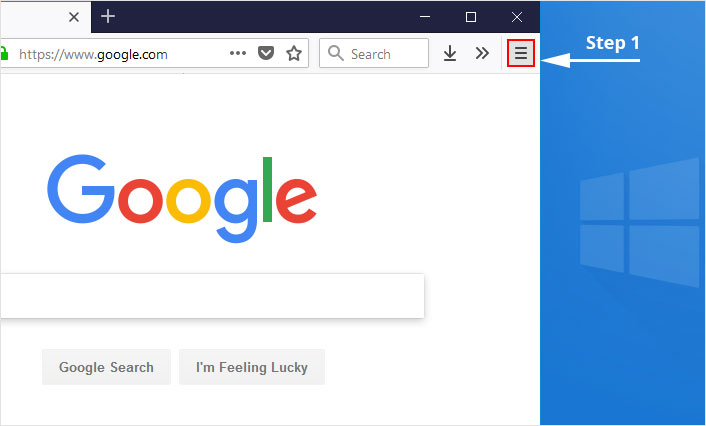
2. Select “Add-ons” from the menu.
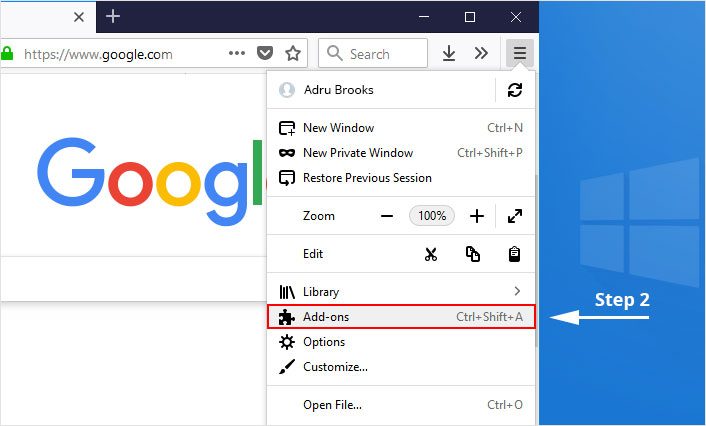
3. Click the “Remove” button next to the extension you wish to get rid of.
Now that we have successfully eliminated the malicious browser extension, we need to create a robust firewall to avoid any such thing that makes our system and privacy vulnerable to various online threats.
The manual methods sometimes might not work at Windows OS because finding suspicious and modified registry files in registry editors is a difficult task. On the other hand, if a useful file gets deleted, in that case, windows will stop working properly.
That’s why it is highly recommended to use an automatic tool to prevent gamma ransomware attacks on your computer. If you wish to get more news and awareness on the happenings of the cybersecurity, then keep visiting us.
Tips to Prevent virus and malware from Infecting Your System:
- Enable your popup blocker: Pop-ups and ads on the websites are the most adoptable tactic used by cybercriminals or developers with the core intention to spread malicious programs.
So, avoid clicking uncertain sites, software offers, pop-ups etc. and Install a powerful ad- blocker for Chrome, Mozilla, and IE
- Keep your Windows Updated: To avoid such infections, we recommend that you should always keep your system updated through automatic windows update.By doing this you can keep your device free from virus.According to the survey, outdated/older versions of Windows operating system are an easy target.
- Third-party installation: Try to avoid freeware download websites as they usually install bundled of software with any installer or stub file.
- Regular Backup: Regular and periodical backup helps you to keep your data safe in case the system is infected by any kind of virus or any other infection.Thus always backup important files regularly on a cloud drive or an external hard drive.
- Always have an Anti-Virus: Precaution is better than cure. We recommend that you install an antivirus like ITL Total Security or a good Malware Removal Tool like Download Virus RemovalTool
