Cadillac.407@aol.com Phobos Ransomware – A Rising Data Encryption Cyber Threat!
Cadillac.407@aol.com Phobos ransomware is a vicious file encrypting virus that belongs to ransomware family, which evades the user’s system without their knowledge, after successfully entering the system it will encrypt (lock) the user’s data.
Phobos Ransomware is categorized as dangerous malware because the infection can have severe outcomes and infected almost all Windows Operating System version like Windows XP, Windows7, Windows8, Windows8.1 and Windows 10. It is developed by the team of cyber attackers with the sole motive to extract huge ransom money by phishing innocent users.
It is designed to modify predefined browser settings and manipulate various functionalities to run a built-in encryption module and corrupt every single data available on your hard drive and locks down the entire system.
The primary purpose of the Phobos ransomware is to blackmail you by not allowing you to access, use or modify the personal files that you keep on your system until you pay the ransom requested by the hackers.
As the article advances, you will come to know how the ransomware infected your system and how you could potentially Decrypt Cadillac.407@aol.com Phobos Ransomware without paying the ransom, followed by various removal techniques which encapsulate manual preventive methods and a robust tool that fights with the ransomware.
What is Cadillac.407@aol.com Phobos ransomware?
Phobos Ransomware is a critical data encrypting ransomware that make an entry on your system secretly and corrupts valuable files and deletes system’s backup with the help of sophisticated cipher algorithm.
It infiltrates the security-vulnerable computer silently and allows the remote attacker to access the compromised system to execute codes that encrypt users' valuable files with nasty .Phobos extension.
For instance, an image named test.jpg will be encoded and renamed to test.Phobos.
Following strong encryption, Phobos creates an HTML file placing a copy in every existing folder of the user’s computer.
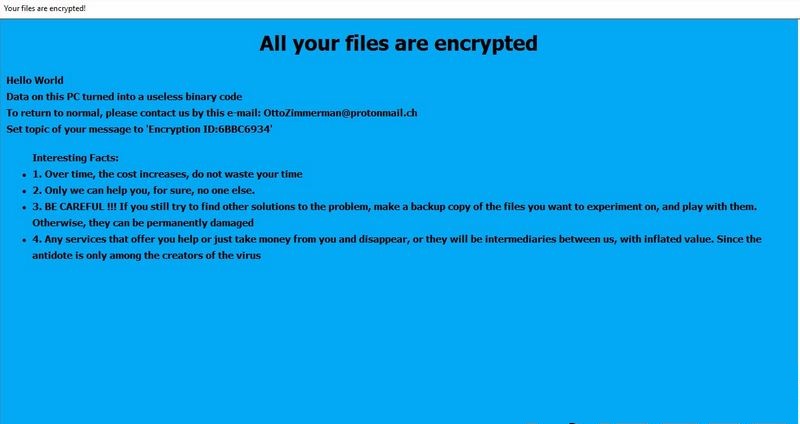
The new HTML file contains a ransom message informing victims of the encryption and giving instructions regarding the method to pay ransom money in Bitcoin or other cryptocurrencies.
Whenever a user tries to open the compromised or locked file, it displays a ransom extortion note “Phobos-Instruction.HTML.”
It is likely to appear on the computer screen at the end of the attack and here is the message you could read:
Like other ransomware, it also uses AES technique to encrypt your files and hide the decryption tools and keys on a remote server.
Once payment is submitted, there is no such guarantee that you would be able to recover Encrypted files.
The Phobos Ransomware will encrypt all files that belong to one of the following types:
- Audio files
- Document files
- Backup files
- Image files
- Video files
- Pdf files
- Banking creational, etc.
After encrypting the files, it leaves a ransom note that goes by different names. Despite the many names, the ransom note remains the same.
A victim is asked to pay the ransom in Bitcoins, but first, they will have to contact the hackers via one of the email addresses given in the ransom note.
Phobos Ransomware– Distribution Techniques
Currently, ransomware attack campaigns may target computer users worldwide. Phobos Ransomware distributes itself using multiple mechanisms. A payload dropper that kick-starts the malicious script of this ransomware has been distributed around the World Wide Web, and experts have acquired a malware sample. By any chance if the file happens to be on a system and if the user clicks on it to see what kind of record it is, the system gets infected by the ransomware.
To achieve persistence Phobos Ransomware might make entries in the Windows Registry, and could repress or launch processes in a Windows environment. Such entries are logged so that the ransomware can start automatically every time the Windows boots up.
- Spam and junk email attachments
- Virtual desktop services
- Backdoor malware
- Pirated and free software’s
- Contagious webpages
- Fake advertisement’s or download portals, etc.
What should be your next logical step?
By any chance, if you believe that your computer could be infected with this infection, do not hesitate to eliminate ransomware. This is the most straightforward approach to end its movement on your operating system.
If you let this malware remain on your PC, this ransomware can cause significantly more harm by encoding another bit of your documents.
Since quite possibly this infection is back online, we highly recommend you to run a full system scan with a malware removal tool.
We recommend you to download Malware Crusher. This is an antimalware tool that fights against all kinds of ransomware and capable to prevent their attacks on the computer.

Thinking of Paying the Ransom? Stop Thinking; Always Say NO To Cyber-Criminals!
Despite the fact that we highly advise not paying the ransom, we understand that a few organizations would not have the capacity or technical guidance to get away without the information that has been put away on the encrypted systems, so unfortunately in such cases, paying the ransom will be the only option to advance the business.
Cybersecurity experts never recommend you to pay! Paying money is not a good option because once you start paying a ransom, the cyber attackers will demand more.
We suggest investing the money you are demanded to pay into some backup may be a better option because data loss wouldn’t be a problem.
Remember that you can never be sure whether the criminals would give you a working decrypting key.
How to Recover Encrypted Files And Remove Cadillac.407@aol.com Phobos Ransomware
There have been instances in the past showing the users were hit by the same ransomware for the second time, even though they have already paid the ransom amount.
From here, all we can say is if you don’t act quickly in the right way, you might not get another chance, so we suggest you follow removal guide to delete Phobos Ransomware that may also help you in the removal process of Cadillac.407@aol.com files and folders and other malicious content. The guide is divided into three parts:
- Unlock Computer In Safe Mode
- Restore System
- Automatic Prevention
Temporarily Disable Phobos Ransomware in safe mode using Command Prompt
1. Steps to be followed to enter the safe mode Win XP/Vista/7
- Click start > then shut down > then restart.
- While the computer is booting up at the very first screen start tapping F8 until you see the advanced boot options.
- In the advanced boot option’s, you need to select safe mode with Command prompt from the list of given options.
2. Steps to be followed to enter safe mode in Win 8/10
- On the windows login screen, you need to press the power option.
- Now, press and hold the shift key on the keyboard, and then click Restart.
- Now, among the list of options you need to select Troubleshoot, and then advanced options, then start-up settings and finally press restart.
- Once your computer restarts and gives you the list of start-up options you need to select Enable Safe Mode with Command prompt.
3. Restore System
- Once you see the command prompt windows, type in cd restore and hit enter on the keyboard.
- Now, type rstrui.exe and hit Enter again.
- Then you would see new windows, click on next over there and select a restore point that is before the date of infection.
- Then, click next followed by yes.
At present, your computer is in a state that has its file and data backed up at a safe restore point. We also suggest you make a copy of backed up data into some external hard drive.
It is now time, to reinstall your Windows via an external source such as pen drive, CD or DVD.
While installing Windows, allocates disk space to C, D and E drive. If asked to restore any files, select the restore point and get the backed up data into the new operating system.
Your system format is complete; also your data is backed up. Now you must create a strong firewall against such intrusions and prevent them in the future.
Automatic Preventive Method
Malware Crusher is the most commonly used anti-malware software for the Windows computer. Its malware removal capabilities make it the most impactful tool and prevent you before the ransomware starts infecting your system because:
- Its real-time protection feature performs a deep scan, detects malicious software and infected encrypted files within your system.
- The Quarantine feature of the tool removes all infected files from your computer. In addition, keeping a record of all deleted malicious program.
- Malware Crusher also creates a shield against Ransomware, Adware, Malware, Browser Hijackers, Viruses, Extensions and Trojans from entering into your system.
- The 24X7 online protective shield works as an anti-exploit technology and blocks the ransomware component before they hold files as a hostage.
- Malware Crusher tirelessly visits all domains, URLs and web pages to secure your online presence from fraudulent entities.
- Malware Crusher becomes fiercer in detecting keylogging, remote connections and saving your session data from being recorded.
To get a better security awareness on preventing cyber-attacks and security threats, we recommend Malware Crusher, trusted by many users.

Tips to Prevent virus and malware from Infecting Your System:
- Enable your popup blocker: Pop-ups and ads on the websites are the most adoptable tactic used by cybercriminals or developers with the core intention to spread malicious programs.
So, avoid clicking uncertain sites, software offers, pop-ups etc. and Install a powerful ad- blocker for Chrome, Mozilla, and IE
- Keep your Windows Updated: To avoid such infections, we recommend that you should always keep your system updated through automatic windows update.By doing this you can keep your device free from virus.According to the survey, outdated/older versions of Windows operating system are an easy target.
- Third-party installation: Try to avoid freeware download websites as they usually install bundled of software with any installer or stub file.
- Regular Backup: Regular and periodical backup helps you to keep your data safe in case the system is infected by any kind of virus or any other infection.Thus always backup important files regularly on a cloud drive or an external hard drive.
- Always have an Anti-Virus: Precaution is better than cure. We recommend that you install an antivirus like ITL Total Security or a good Malware Removal Tool like Download Virus RemovalTool
