Writehere@qq.com Ransomware - A Rising Cryptovirus
The Internet Society found a new variant of file-locking ransomware behind the unauthorized change in Windows registries, slow internet speed and performance of computers at offices and homes.
The cybersecurity investigators dubbed the variant as Writehere@qq.com Ransomware which is currently attacking private organizations, hospitals, colleges, universities and statutory bodies of the government in the major cities of the world.
The research from security experts shows the ransomware as a cause of data loss, file loss and data theft. If your documents and files are encrypted with .id-.[writehere@qq.com].btc extension, then your computer is probably under the cyber attack.
The in-depth investigation from experts has revealed answers to many questions and conclude this threat as a very powerful malicious program possessing different features of major threats like malware, viruses, scareware, keyloggers and hijackers.
What is Writehere@qq.com Ransomware?
It belongs to the family of Dharma ransomware, takes control after crawling in your system and encrypts many useful files. After invasion and encryption, the writehere@qq.com ransomware virus demands payment in bitcoins to decrypt the data.
Like all other ransomware, it is also a file-encrypting malicious code that hijacks your computer to encrypt photographs, music records, business reports, pdf, docs and all other data only after utilizing file lock and encryption techniques like AES/RSA.
These techniques are the part of its malicious code that modifies your system registry files in order to secretly allocate themselves into the infected machine for locking out the data and files.
Why Writehere@qq.com Cryptovirus Is Dangerous?
First thing first, ransomware today is the most widely used malicious program and acts as a threat within the computer. The Dharma’s Writehere@qq.com ransomware is highly infectious. Its program code is smart enough to automate itself every time it infiltrates a new system.
It quickly spreads through spam emails, websites, peer to peer file sharing, freeware (fake software updates), cracked or pirated software and social hijacking. It degrades the computer performance and compels you to pay money for your files within some time limit.
Once victimized, the ransomware attacks your system, web browsers settings and corrupts hard drive of the computer. Applications do not respond sometimes and adequately lack a few important program files.
Cybercriminals via these threats steal information like IP address, URL’s Search, browser history, search queries, username, ID, passwords, banking information and ATM Card information.
Direct contact with hackers on C2 servers let them steal sensitive and financial information. Furthermore, it acts as a spy agent to our computer for cybercriminals.
Once this ransomware is tricked into a system, it checks the PC for data files and encrypts them. Being the latest file-encrypting malicious code security experts are also not very aware of the functioning and how to prevent its infections?
Moreover, there is no process of decryption available to counterfeit the impacts caused by the Writehere@qq.com ransomware. Additionally, there exists no Writehere@qq.com decryptor tool to stop file-encryption.

Writehere@qq.com Ransomware - Tricks and Encryption
The ransomware infects the system and drop a file extension named .id-.[writehere@qq.com].btc.
Once the files are encrypted with this extension, a ransom note named FILES ENCRYPTED.txt file is created in place of those files and folders where the data has been encrypted.
After dropping the ransom, cyberattackers demand payment in Bitcoins. The note randomly opens whenever the user tries to access an encrypted locked file.
Writehere@qq, a variant of Dharma ransomware follows Symmetric/Asymmetric encryption algorithm to lock user’s access. Additionally, there are chances that it might work as a crypto mix variant to perform cryptojacking and coin-mining.
It distributes via spam emails; the mail contains some infected attachment or link that on access enters ransomware. This threat targets all versions of Windows and for encrypting files, it uses RSA-2048 key (AES CBC 256-bit encryption algorithm), AES-265 and RSA encryption method.
The encrypted files are stored with random notes at %AppData% or %LocalAppData% folder. Important documents and files like .doc, .docx, .xls, .pdf etc are no longer working and can’t open.
Analysis of this ransomware shows that it has become one of the most devastating cyber threats of 2018 and posses potential to become the next large-scale ransomware.
Are Writehere@qq.com Ransomware Decrypt Tools Worth Using?
No, at this time it is impossible to recover all the encrypted files as the algorithm of encryption is strong and runs on private keys of C2 servers. Therefore, it is quite notable that forging out any decryption key and tool is not realistic.
Moreover, to make any decryption tool it is important to reverse engineer the program code of ransomware’s encryption mechanism. Unfortunately, more time is required to break down the AES/RSA mechanism.
As per security experts, presently it is impossible for researchers to reverse engineer the encryption process. If they succeed in doing that then protecting computers from CrySis, Dharma, Wannacrey ransomware, etc. will be easy.
We also know that it is difficult to obtain keys to decrypt ransomware files. Even more, cyber attackers claim to generate keys and tools for your locked files. But, that would only happen if you pay them.
Paying ransom to get the decryption tool is not a good option because the probability of getting cheat is more. Besides no attacker would like to offer you a solution to counterfeit the problem created by himself.
If you once pay them, doing so would encourage these bad guys in expanding their operations. We strongly, suggest you do not pay anything to the ransom and instead address the situation to internet law enforcement bodies of your respective countries.
At present, there exists no decrypt tool to recover your files, but it is important to take preventive measures before the ransomware starts attacking your computer once again after entering into the advanced phase.
Therefore we would recommend all the Writehere@qq.com victims to follow the below ransomware removal guide such that it becomes easy to enter into your system after the ransomware has locked your access.
Additionally, at the end of the article, you will get two vigilant cybersecurity tools which you can download at your computer to detect, remove and prevent the entry of almost all ransomware into your computer.
Temporarily Disable Writehere@qq.com Ransomware in safe mode using Command Prompt
If you can’t access your computer, then it might become impossible to remove Writehere@qq.com ransomware. However, system reboot in Safe Mode could give you entry into your computer followed by creating a system restore point.
Once you are into your computer, perform a full system scan using the antimalware tool which we have suggested at the end of this article.
Steps to be followed to enter the safe mode Win XP/Vista/7
- Click start, then shut down, then restart.
- While the computer is booting up at the very first screen start tapping F8 until you see the advanced boot options.
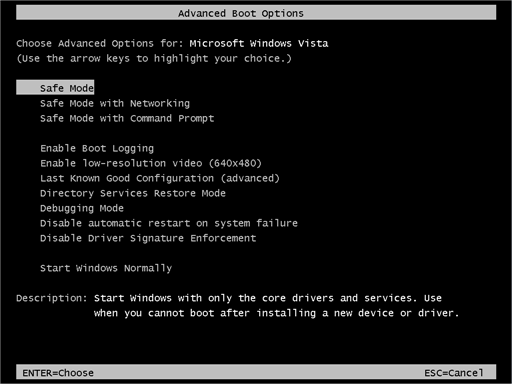
- In the advanced boot option’s, you need to select safe mode with Command prompt from the list of given options.
Steps to be followed to enter safe mode in Win 8/10
- On the windows login screen, you need to press the power option.
- Now, press and hold the shift key on the keyboard, and then click Restart.
- Now, among the list of options you need to select Troubleshoot, and then advanced options, then startup settings and finally press restart.
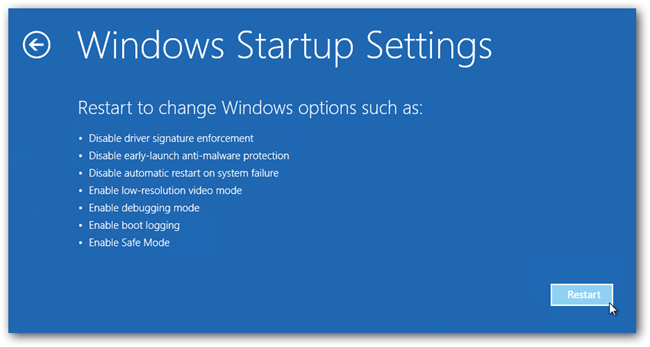
- Once your computer restarts and gives you the list of startup options you need to select Enable Safe Mode with Command prompt.
Restore System
- Once you see the command prompt windows, type in cd restore and hit enter on the keyboard.
- Now, type rstrui.exe and hit Enter again.
- Then you would see new windows, click on next over there and select a restore point that is before the date of infection.
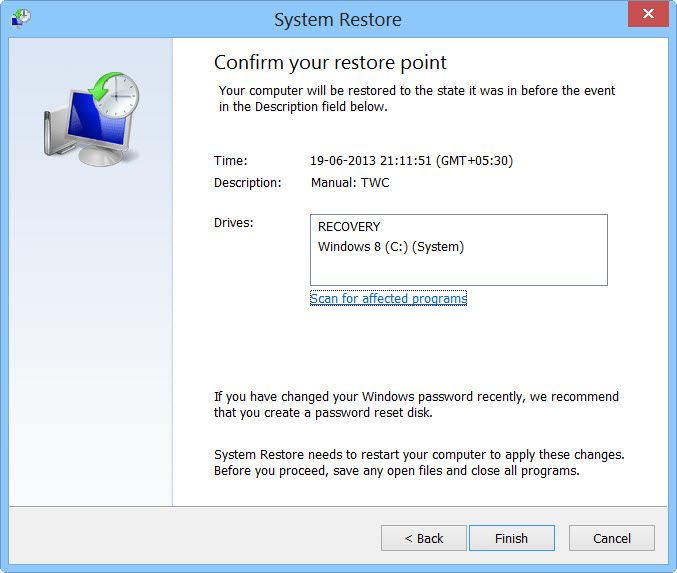
- Then, click next and followed by yes.
At present, your computer is in a state that has its file and data backed up at a safe restore point. We also suggest you make a copy of your backed up data into some external hard drive.
It is now time, to reinstall your Windows via an external source such as USB drives, CD or DVD and portable HDD devices.
While installing Windows, allocate disk space to C, D and E drive. If asked to restore any files, select the restore point and get the backed up data into the new operating system.
Your system format is complete, also your data is backed up. Now you must create a strong firewall against such malicious threats to prevent future attacks.
Cyber attackers are very advanced and had learned to gain illegal access to the computer. More than that, they make their malware more adaptable, resilient and damaging. It is impossible to stop cyberwarfare and cyberterrorism by common antivirus software.

Thus, the best preventive step is to upgrade our cyber defense systems at home and office computers with those cybersecurity tools that could delete Writehere@qq.com ransomware with their real-time protection feature, quarantine feature, web protection and anti-exploit technology.
Note: If your computer doesn’t have such security software, then download ITL Total Security and Malware Crusher to prevent malware attacks on your system. Both are reputable, vigilant and robust in creating a shield 24X7 against any cyberthreat.
These tools are highly recommended if you are willing to give advanced security to your PC. Their 5-minute function could be a savior for your computer!
Tips to Prevent virus and malware from Infecting Your System:
- Enable your popup blocker: Pop-ups and ads on the websites are the most adoptable tactic used by cybercriminals or developers with the core intention to spread malicious programs.
So, avoid clicking uncertain sites, software offers, pop-ups etc. and Install a powerful ad- blocker for Chrome, Mozilla, and IE
- Keep your Windows Updated: To avoid such infections, we recommend that you should always keep your system updated through automatic windows update.By doing this you can keep your device free from virus.According to the survey, outdated/older versions of Windows operating system are an easy target.
- Third-party installation: Try to avoid freeware download websites as they usually install bundled of software with any installer or stub file.
- Regular Backup: Regular and periodical backup helps you to keep your data safe in case the system is infected by any kind of virus or any other infection.Thus always backup important files regularly on a cloud drive or an external hard drive.
- Always have an Anti-Virus: Precaution is better than cure. We recommend that you install an antivirus like ITL Total Security or a good Malware Removal Tool like Download Virus RemovalTool
