A gang of hackers have been successfully breaking into unsecured enterprise servers since June. To make it possible they have been using RDP brute-force attacks to get into the user's system remotely and then install the LockCrypt ransomware.
What is LockCrypt ransomware?
LockCrypt now adds up to the long list of ransomware families that is not distributed through spam or exploit kits but depend on RDP brute-force attacks.
Volume of infected systems have been increasing recently and the infection rate is high. Users in mass have been constantly asking for a fix on various websites.
Specialists at AlienVault had something on this after they had a deep look into this infection — Companies that were hit are the US, the UK, South Africa, India, and the Philippines.A report from AlienVault reveals LockCrypt ransomware logged into their network via RDP from 212.111.192.203, an IP address that was found to be affiliated to the Ministry of Education and Science of Ukraine.
LockCrypt ransomware normally breaks into one server, moves alongside to as many machines it possibly can infect and installs LockCrypt ransomware remotely on each system.
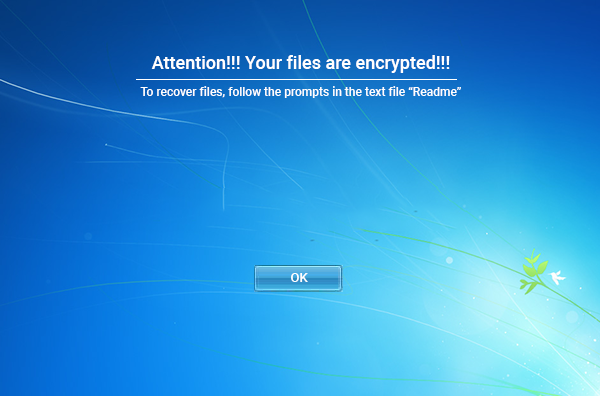
On infection it would encrypt all the files and leave a prompt followed by the ransom note.
[Prompt]
[Ransom note]
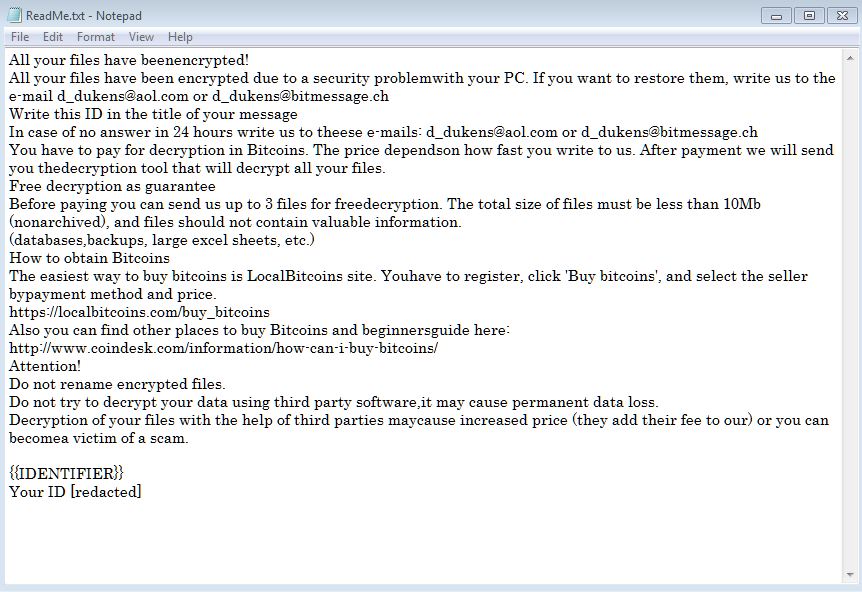
To get the files decrypted, victims must pay a ransom somewhere between 0.5 and 1 Bitcoin each server, that is $3,500 and $7,000 per machine.
Some companies may face ransom demands of hundreds of thousands of dollars if attackers manage to compromise their database.
The LockCrypt ransomware appears to be making a lot of profit for its developers. Just three of the many Bitcoin wallet addresses used in ransom notes reveal the group made around $175,000 worth of Bitcoin.
What if you are infected? What should be your next move?
By any chance, if you believe that your computer could be infected with this infection, do not hesitate to eliminate LockCrypt ransomware. This is the most straightforward approach to end its movement on your operating system. If you let this malware remain on your PC, this ransomware can cause significantly more harm by encoding another bit of your documents. Since quite possibly this infection is back online, we highly recommend you to run a full system scan with malware removal tool.
Thinking of paying the ransom? Stop thinking, it’s a clean no to it.
Despite the fact that we highly suggest not paying the ransom, we understand that a few organizations would not have the capacity to get away without the information that has been put away on the encrypted PCs, so unfortunately in such cases, paying the ransom will be the only option to advance the business. Also, we can just advice you to not pay the amount. Remember that you can never be sure whether the criminals would give you a working decryption key.
Things you must know about a ransomware attack
There have been incidents showing the users were hit by the same ransomware for the second time, even though they have already paid the ransom. From here, all that we can say is if you don’t act quickly and the right way, you might not get a second chance.
So, the best solution for this is to get rid of the ransomware using the steps given at the bottom of this article.
Temporarily Disable LockCrypt ransomware in Safe Mode with Command Prompt
Step – 1 (enter safe mode)
- Steps to be followed to enter the safe mode Win XP/Vista/7
- Click start, then shutdown, then restart.
- While the computer is booting up at the very first screen start tapping F8 until you see the advanced boot options.
- In the advanced boot option’s, you need to select safe mode with Command prompt from the list of given options.
Steps to be followed to enter safe mode in Win 8/10.
- On the windows login screen, you need to press the power option.
- Now, press and hold the shift key on the keyboard, and then click restart.
- Now, among the list of options you need to select Troubleshoot, and then advanced options, then startup settings and finally press restart.
- Once your computer restarts and gives you the list of startup options you need to select Enable Safe Mode with Command prompt.
Step – 2 (Restore system)
- Once you see the command prompt windows, type in cd restore and hit enter on the keyboard.
- Now, type rstrui.exe and hit Enter again.
- Then you would see new windows, click on next over there and select a restore point that is before the date of infection.
- Then, click next and followed by yes.
After temporarily disabling the ransomware, we need to create a strong firewall to fight against such intrusions and prevent them in future.
Tips to Prevent LockyCrypt rasomware from Infecting Your System:
1. Enable your popup blocker: Pop-ups and ads in the websites are the most adoptable tactic used by cybercriminals or developers with the core intention to spread malicious programs. So, avoid clicking uncertain sites, software offers, pop-ups etc.
2. Keep your Windows Updated: To avoid such infections, we recommend that you should always keep your system updated through automatic windows update. By doing this you can keep your device free from virus. According to the survey, outdated/older versions of Windows operating system are an easy target.
3. Third-party installation: Try to avoid freeware download websites as they usually install bundled of software with any installer or stub file.
4. Regular Backup: Regular and periodical backup helps you to keep your data safe in case the system is infected by any kind of virus or any other infection. Thus always backup important files regularly on a cloud drive or an external hard drive.
5. Always have an Anti-Virus: Precaution is better than cure. We recommend that you install an antivirus like McAfee or a good Malware Removal Tool like Download Free Virus Removal Tool
6. Install a powerful ad- blocker for Chrome, Mozilla, and IE.
