What is Planetary Ransomware?
Planetary is the recent variant of HC7 Ransomware. It scans your hard drive and encrypt most of your files This computer virus restricts victims from accessing various files stored on infected machine. It includes databases, images, and other personal and sensitive data. After file encryption, it renames the affected data by appending. PLANETARY extension.
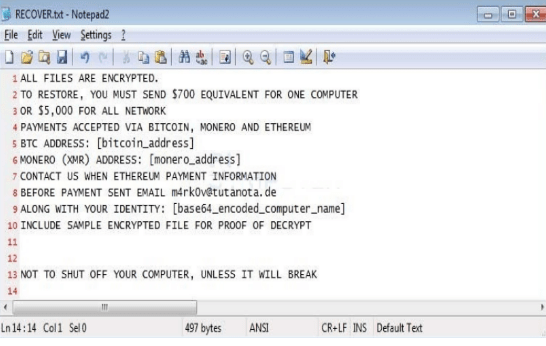
When infected, the developers attack a single victim to decrypt a single machine for a set price or the entire network for another price. As you can see from the ransom note below, the current ransom amount is $700 per machine or $5,000 for all of the machines on the network. Noticeable feature of this PLANETARY ransomware and its developers that it accepts payment in the Bitcoin, Monero, and Ethereum cryptocurrencies.
Also read-How To Remove Cutwail Botnet Virus From Computer?
In the earlier similar attacks, the method used to decrypt HC7 encrypted files was discovered by performing memory forensics on a victim's computer in order to retrieve the password used on the command line when the ransomware was installed. The change of success using this method, though, diminishes the longer the computer is in use and no longer works at all if the computer has been rebooted.
How does this Planetary Ransomware infect your system?
- Bundling: Through third party installers by concealing itself in freeware installation. It comes bundled with free application hosted from unreliable site. When user install those free application then this infection also gets installed automatically.
- It can also get attached with on your PC, if you frequently visit unsafe site like Porn sites or betting sites which contain illegal stuff. In addition, user should also avoid clicking on misleading ads and random links which redirects the victim to social media site.
- It gets inside your system along with the installation of any new software applications which the user does without completely reading license agreements or reading without terms and condition. Most of these cases are sharing files like music, photos and many more in networking environment, visiting various adult websites are also liable behind the insertion of this threat inside your system.
- Attachments send via emails or Facebook, Skype messages. This trap is genuinely old, however it is always getting enhanced. The most recent hit is to influence it to look an associate sent you that email and it will also incorporate what seem, by all accounts, to be business related documents inside. Make sure to search for the file attachment before you take a gander at the document name. If it closes with .exe or it is .exe file then it’s most likely an infection!
- Spam emails: This browser hijacker gets into your computer through malicious email attachments in the spam emails tab. malicious infected attachments and download links in an unknown email.
- Carelessness-It gets installed when you click unintentionally on any infected link. Always pay attention while clicking on unsafe links or unknown links.
- Torrents & P2P File Sharing: Online Ads are another common culprit. Torrent sites especially are well known for their tricks involving multiple fake download buttons. If you click on the wrong button you’ll get a file to download that is named exactly like the file you want. Unfortunately, what’s inside is actually the virus.
- Fake download websites are another wellspring of hijacker programs. These websites have worked in calculations, which enable them to duplicate your search queries and influence the search engines to trust they have an ideal match for your search. When you endeavor to download a file from such a webpage the name will fit, but the file that you have downloaded are really going to be loaded with infections, viruses, malwares and other threats. So, it is never a smart thought to open documents got from arbitrary sources without scanning them for infections first. Always keep an anti-virus program on your machine.
Common symptoms of Planetary Ransomware:
- Unstable behavior of the browser, frequent crashes.
- Default home page of the browser is changed.
- Your web browsers are now equipped with all new add-ons toolbars and extensions.
- Every time you go online searching your something you get redirected to the target portal or to fake security warning which would want you to download a program to fix your computer.
- Poor system performance, slow response time as the advertisement would pop out of nowhere on the screen even when the browser is disabled.
- Slow internet browsing speed or internet would stop unexpectedly.
- The operating system would crash now and then, or computer would boot up for no reason.
- An adware gradually weakens the security of the computer authorizing the installation of other malware programs.
- New icons are added or suspicious programs appear on the desktop screen out of nowhere.
- Certain system setting and browser settings are disabled or changed.
- Ads pop up even when the browser is not open.
- New tabs open in browser to display ads or search results would always end up with displaying advertisement banners.
Also read-How To Remove Ramnit Trojan Virus From Computer Easily?
Download Free Removal Tool
Tips to prevent Planetary Ransomware from entering your computer :
1. Enable your popup blocker: Pop-ups and ads in the websites are the most adoptable tactic used by cybercriminals or developers with the core intention to spread malicious programs. So, avoid clicking uncertain sites, software offers, pop-ups etc.
2. Keep your Windows Updated: To avoid such infections, we recommend that you should always keep your system updated through automatic windows update. By doing this you can keep your device free from virus. According to the survey, outdated/older versions of Windows operating system are an easy target.
3. Third-party installation: Try to avoid freeware download websites as they usually install bundled of software with any installer or stub file.
4. Regular Backup: Regular and periodical backup helps you to keep your data safe in case the system is infected by any kind of virus or any other infection. Thus always backup important files regularly on a cloud drive or an external hard drive.
5. Always have an Anti-Virus: Precaution is better than cure. We recommend that you install an antivirus like McAfee or a good Malware Removal Tool like Download Free Virus Removal Tool
6. Install a powerful ad- blocker for Chrome, Mozilla,and IE.
