What is RAA ransomware?
The latest ransomware called RAA is made up entirely on JavaScript and believed to be spreading via email attachments that pretend to be doc files with names like mgJaXnwanxlS_doc_.js. Once the JavaScript is opened, and the ransomware spreads in your computer, it will encrypt files on the affected machine and then demand a ransom amounting roughly to US$250 to get the files. We had seen a similar ransomware called Ransom32 that was created using NodeJS and packaged inside an executable. RAA is a little different, as it is not delivered via an executable like Ransom32, but uses a standard JS file. JavaScript has the standard implementation, which does not include any advanced cryptography functions. To spread the RAA developers utilized the Cryptos library so that AES encryption could be used to encrypt the files. RAA is being spread and distributed via emails as attachments that pretend to be doc files and have names like mgJaXnwanxlS_doc_.js. Once you click on this file, the JS file is opened, and it will then work its main work, which to encrypt the computer and then demand a ransom of ~USD 250 to get the files back. To do further damage, another nasty feature this ransomware does is it will also steal and extract an embedded password stealing malware called Pony from the JS file and install it onto the onto the victim's computer. This ransomware was first discovered by security researchers @JAMES_MHT and @benkow_.
Also read-How to remove WinYoo adware?
New Variant of RAA Ransomware
The RAA ransomware made its appearance in June this year, but cybersecurity researchers at Kaspersky Lab have discovered a new variant of it already. Like the earlier variant of the ransomware, RAA was distributed by email, but now this nasty software is injecting code which is hidden in a password protected Zip attachment which is more difficult for anti-virus software to discover - the content of protected archives is harder for security programmes to examine properly. This new version of RAA has new targets, now preferring to target businesses rather than ordinary users probably because the payoff is much higher. The email's content claims about an overdue payment to a supplier, with information about the fraudulent request for payment hidden in the Zip file for what the malware creator say is "due to security reasons." This new version of RAA is even more potent as it does not also need to communicate with the C&C server to encrypt files on the victims' PC. This trojan generates its own keys on the infected machine and ignores to ask for a master key to unlock. This self-generated key helps RAA to infect offline machines, in addition to those connected to the internet. As if locking a business out of its files was not good enough, the ransomware payload delivers the Pony Trojan, a form of data-stealing malware capable of stealing login credentials.
How RAA Encrypts a victim's Files
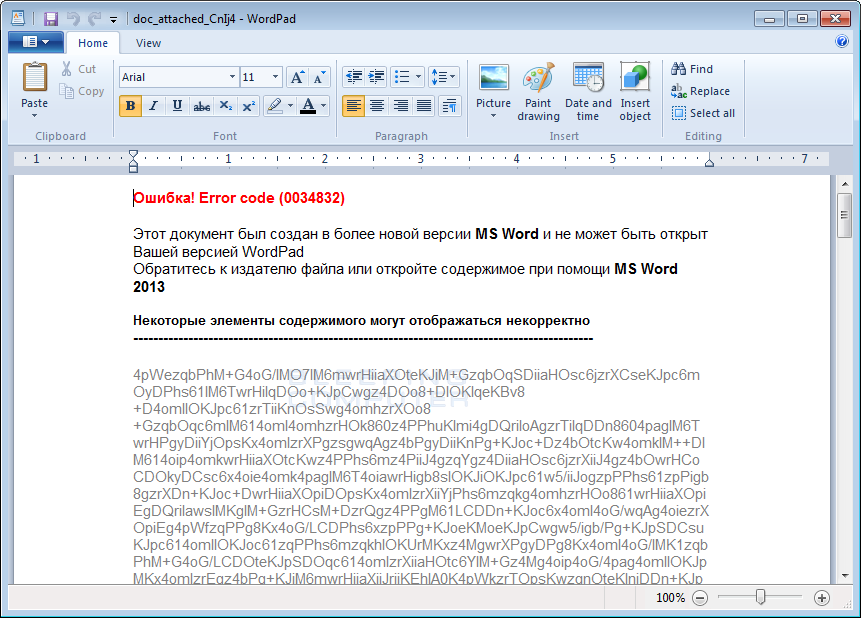
RAA infection ransom note is displayed in Russian as you open it. However, it is believed that to spread itself globally and then it’s distributed more widely and localized for other global languages. The modus operandi of this ransomware is that it is spread through email which has an attached Javascript (.JS) file. When the victim to open this ransomware, and double-clicks on this JS file, it would lead to a window which has an execute default program which is associated with JavaScript files. This is the Windows Script Host or wscript.exe. When the data is executed, it will generate a fake word document in the %MyDocuments% folder. This word document will have a name similar to doc_attached_CnIj4 and will be automatically opened to make it look like the attachment was corrupted
Source of this Ransomware
As per the research did the only source of this ransomware to get in your computer is the infected emails with any malicious attachment ransomware uses the Javascript to convert the text and then puts in a ransomware note which demands money to encrypt the locked files.
Also read-How to remove Matrix Ransomware?
How to protect yourself from Ransomware?
In today’s digital world it is essential to secure your computer for any cyber-attacks, it is vital that proper computer hygiene and habits are followed, and reliable security software is being installed on your computer. Most importantly, you should always have a stable and strong backup data that can be restored in the case of an emergency, like a ransomware attack. Make sure you follow the following safety online security habits, which in many cases are the most important steps of all:
- Always have a secure Backup of all the essential data.
- Be careful when you open any attachments if you do not know who sent them don’t open it.
- Emails with attachment with suspicious headings shouldn’t be opened until you confirm that the person actually sent you them,
- Scan attachments with tools like anti-virus tool before opening it.
- Make sure all Windows updates are installed updated! Also make sure you update all programs, especially Java, Flash, and Adobe Reader. Therefore, it is essential to keep them updated.
- Have an excellent reliable security software installed to save your system from any virus attacks.
- Use complex passwords to be safe and try avoiding reusing the same password on multiple sites.
Download Free Removal Tool
Tips to Prevent "RAA ransomware" from Infecting Your System:
1. Enable your popup blocker: Pop-ups and ads in the websites are the most adoptable tactic used by cybercriminals or developers with the core intention to spread malicious programs. So, avoid clicking uncertain sites, software offers, pop-ups etc.
2. Keep your Windows Updated: To avoid such infections, we recommend that you should always keep your system updated through automatic windows update. By doing this you can keep your device free from virus. According to the survey, outdated/older versions of Windows operating system are an easy target.
3. Third-party installation: Try to avoid freeware download websites as they usually install bundled of software with any installer or stub file.
4. Regular Backup: Regular and periodical backup helps you to keep your data safe in case the system is infected by any kind of virus or any other infection. Thus always backup important files regularly on a cloud drive or an external hard drive.
5. Always have an Anti-Virus: Precaution is better than cure. We recommend that you install an antivirus like McAfee or a good Malware Removal Tool like Free Malware RemovalTool
6. Install a powerful ad- blocker for Chrome, Mozilla,and IE.
