Trojan Maljava - A Banking Trojan Uses Java
Trojan.Maljava is a group of Java files that selectively take advantage of system securities vulnerabilities. It has been active since 2010 and made headlines when got associated with fake airline ticketing notifications.
At that time, criminals used this threat in holiday seasons to book fake air travel tickets by dropping phishing emails in your computer. Later on, if you fall victim to such emails, cybercriminals loots your money and spread malware Trojan.Maljava.
It forces itself into your computer to insert malicious java files and attempts to infect it by exploring system weaknesses. The damage level from this system is high, and mainly infects older versions of Windows viz. Windows 98 to Windows 8.
Our team HTRI has discovered the recent attacks where the trojan infection spreads without the user’s knowledge unless the hard drive and RAM secretly get filled.
Computer Troajn especially the banking trojan cause economic damage to billions of dollars' each year due to system failures, waste computer resources, corrupt personal and corporate data, increase maintenance costs, etc.
Thus, you must learn ways to remove Trojan.Maljava from your computer. To help you out we had prepared a trojan removal guide that will successfully delete all the variants of Maljava from Windows.
The Secret Way How Trojan.Maljava Enters Computer
Trojan.Maljava is a family of threats with a range of functionalities. Their method of propagation is different. Some variants of this threat such as Trojan.Maljava!gen4, Trojan.Maljava!gen34, Trojan.Maljava!gen9 use spam email messages and persuade users to open the attached script.
Most of the emails are related to fake notices about the airline tickets and holiday greetings. Even more, the Trojan utilizes unsecure file downloads, P2P network connections to target those victims who casually surf the internet for free software downloads.
Here the Trojan disguises itself as a popular software or program updates which on click from user let to enter the trojan. Most of the Trojan enters into your computer from these ways also:
- A very common way of entry is CD/DVD or U.S.B. Drives.
- Viruses spread through LAN (Local Area Network). If an infected system is connected to a healthy network, then the whole network gets infected.
- If you download software from free websites, then you might sacrifice your privacy and system to virus infections.
- Infected email attachments
- Fake updates that trick you installing them
- Infected documents circulating on peer-to-peer file-sharing networks, torrent sites, and IRC (Internet Relay Chat) channels.
Impacts Of Trojan.Maljava
Once the user executes any variant of Trojan.Maljava, it drops several files. The variant and the infection starts spreading and lead to many computer abnormalities that range from mild to severe.
Some of the most common defects it does to the system are explained as follows.
- Internet browser redirection to untrustworthy and explicit websites.
- Disables security applications and firewall applications.
- Mass sending of spam phishing email messages to compromise a system on SMTP server.
- Blocks network and Internet traffic, cause regular ad pop-ups when the computer is online.
- Search results are always redirected to unknown web pages.
- The most harmful variant of Maljava trojan is Trojan.Maljava!gen4 that contains a backdoor function and allow remote attackers to gain full access.
- Download number of threats on the compromised PC.
- Steals sensitive banking, social networking, other email ID and LogIn ids from a password manager.
- Spy on your every internet activity.
- Connects to remote hosts for updating the configuration file of various variants of Maljava Trojan.
- Gathers essential data such as computer name, operating system version, network setup Ids and hardware/software details.
Trojan.Maljava mostly spreads through email and messages. Consecutively you should always avoid opening emails having an unknown file extension (.exe, .vbs, .bat, .pif and .scr). These extensions are harmful and spoil your computer's performance.
To detect such file in your computer, we recommend an antimalware tool that 24X7 scans your computer and detect unwanted files. The one-click download button of Malware Crusher given below starts scanning your system as soon as it downloads into your system.

If you are not skilled and knowledgeable about the manual removal of different types of trojan, leave it for a reliable anti-malware application which will successfully remove Trojan.Maljava!gen24 easily.
The Trojan’s components will be detected very soon after executing an in-depth scan. Additionally, it automatically updates itself unless your computer is connected to the Internet.
Thus, let us look a complete PC protection kit enough capable to remove all kinds of trojans. The kit is divided into two different parts:
- Automatic Preventive Method
- Manual Preventive Methods
Remove Trojan.Maljava Automatically
Malware Crusher is one of the best and most commonly used anti-malware software for Windows. It costs you nothing in comparison to other security tools and is capable of removing various kind of infections from your machine.
It is an antimalware tool with different malware removal capabilities like;
- It performs a Deep scan, detects malicious software, files and browser extension within your system.
- The Quarantine feature of the tool removes all infected files from your computer in addition to keeping a record of all deleted malicious program.
- Malware Crusher also creates a shield against Ransomware, Adware, Malware, Browser Hijackers, Viruses, Extensions and Trojans from entering into your system.
- Gives a warning and notification on detection of threats and blocks malicious ads while browsing. Eventually, prevents redirect to any third-party website.
- Malware Crusher tirelessly visits all domains, URLs and web pages to secure your online presence from fraudulent entities.
- Malware Crusher becomes fiercer in detecting keylogging, remote connections and saving your session data from being recorded.
To get rid of the Trojan.Maljava!gen4, Trojan.Maljava!gen34, Trojan.Maljava!gen9, you must download Malware Crusher, install it and perform a quick full scan.
It automatically removes all the malicious threats including adware by fixing your computer in less than 5 minutes.
On the other hand, manual methods are stepwise techniques whose execution needs technical knowledge and more time. Moreover, executing steps by yourself may not give you the desired result.
How To Remove Trojan.Maljava!Gen19 Manually?
- Press Ctrl + Shift + ESC together to open Task Manager. Look for suspicious files, right click on it and click End Task.
- Now, press Windows key + R to open RUN box window. Type appwiz.cpl on it, this opens Programs and Features window.
- Select each suspicious program and uninstall it one by one. Once the uninstallation is complete, restart your computer and again redirect yourself to Programs and Features window to check whether the application is present or not.
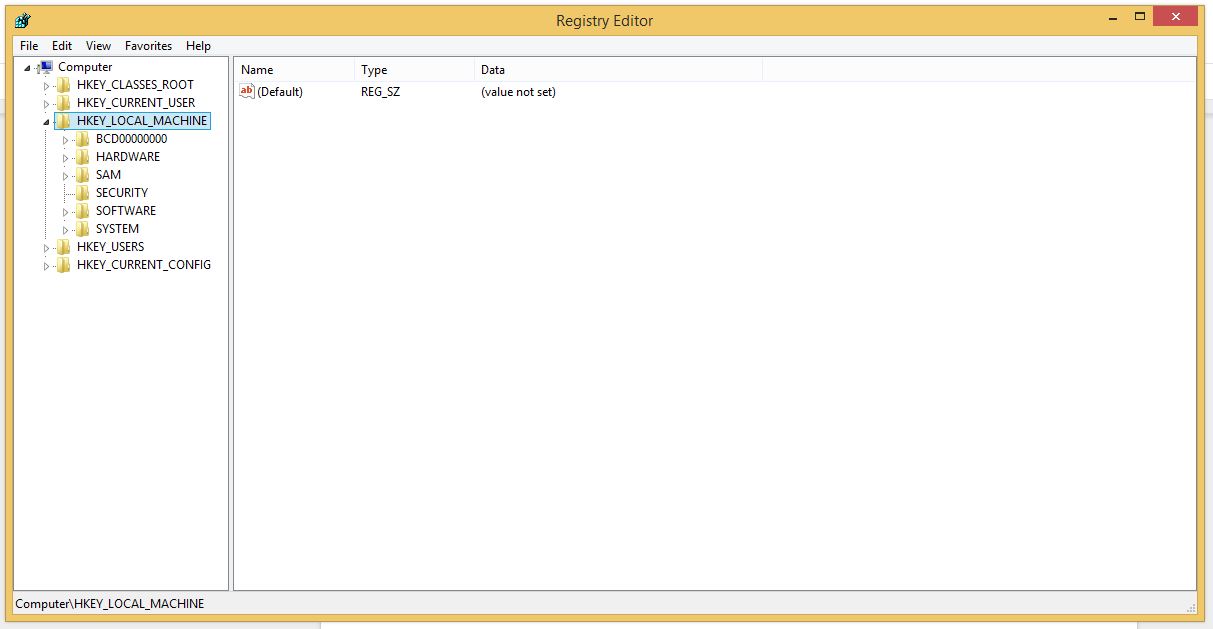
- When convinced, press Windows key + R to open RUN box window. Type regedit on it, hit OK and then click Yes.
- Go through HKEY, HKLM, etc. files and find all suspicious files related to adware and delete them.
- You can also remove malicious extensions and delete Rifhub Ads from your Chrome and Firefox.
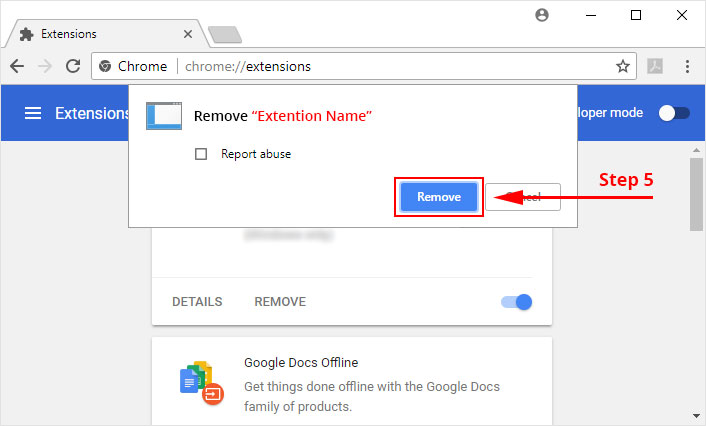
1. Click on the Customize and control menu icon at the top right corner of Google Chrome.
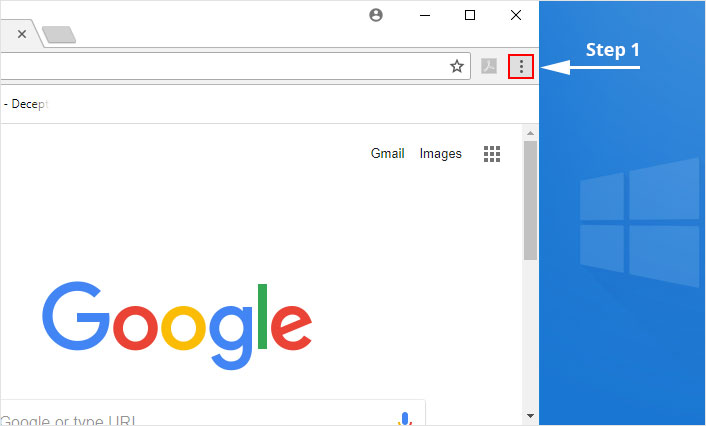
2. Select "More tools" from the menu.
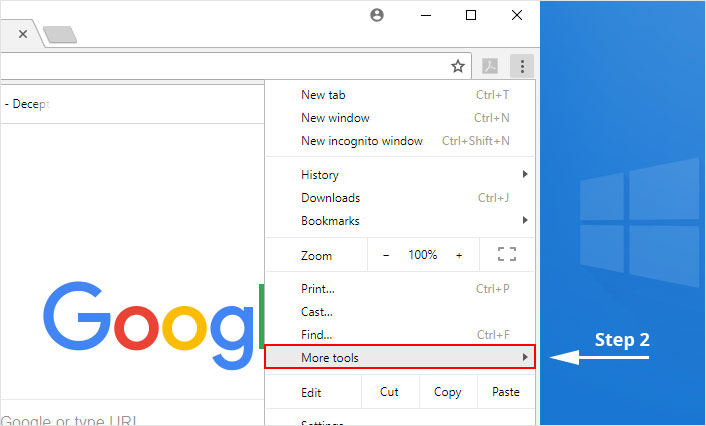
3. Select "Extensions" from the side menu.
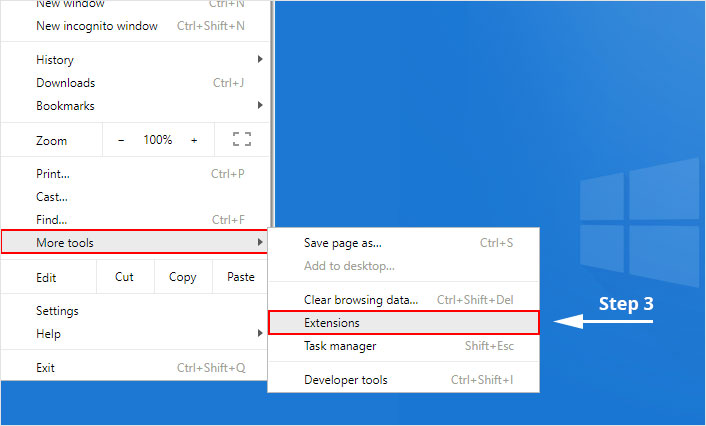
4. Click the remove button next to the extension you wish to remove.
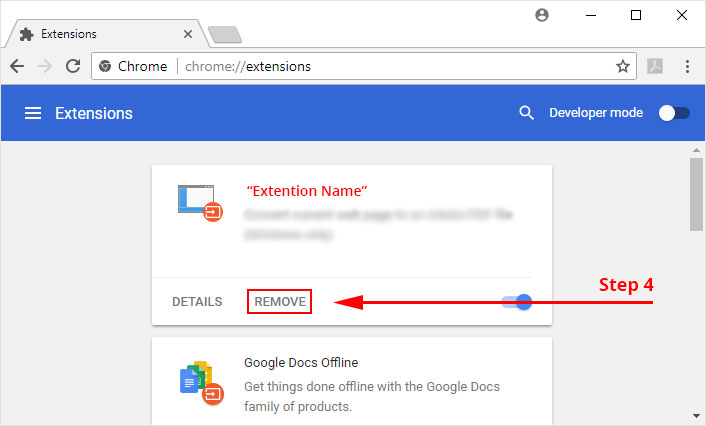
5. It will confirm again, click “remove” and the extension is finally out of the system.
Now that we have successfully eliminated the malicious browser extension, we need to create a robust firewall to avoid any such thing that makes our system and privacy vulnerable to various online threats.
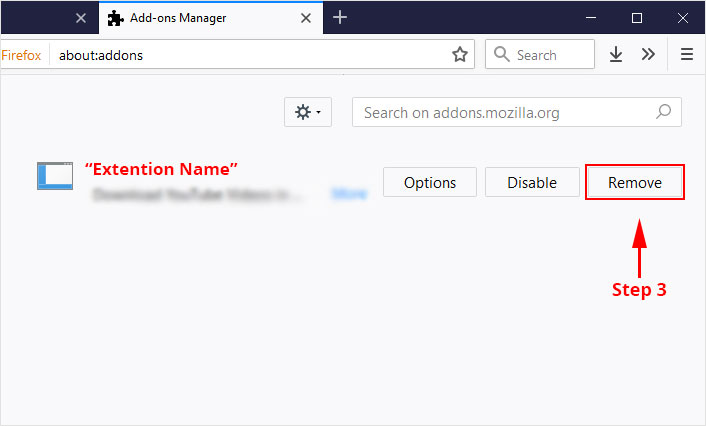
1. Click on the “menu” button at the top right corner.
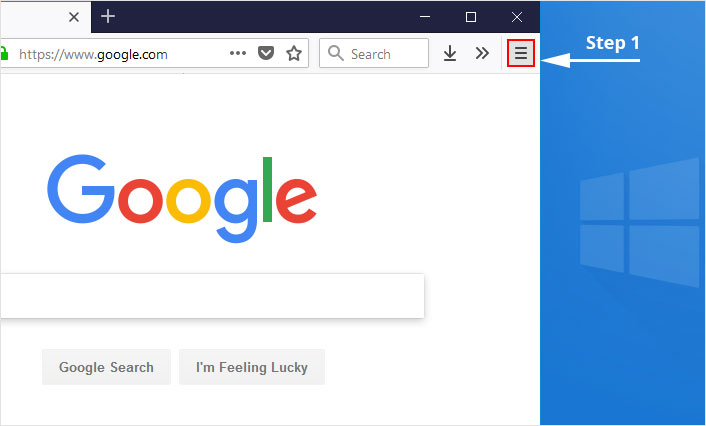
2. Select “Add-ons” from the menu.
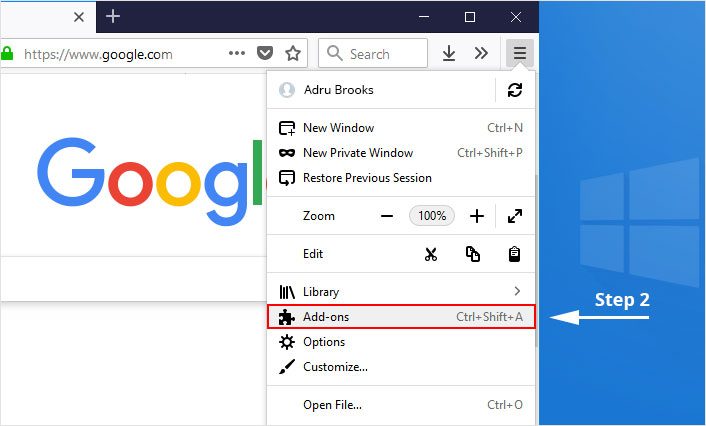
3. Click the “Remove” button next to the extension you wish to get rid of.
Now that we have successfully eliminated the malicious browser extension, we need to create a robust firewall to avoid any such thing that makes our system and privacy vulnerable to various online threats.
The manual method might not work in some instances due to the user’s lack of knowledge which then will modify Windows system files to stay hidden from the regular antivirus program.
The best way in our hand is to eliminate the threat by using an advanced antimalware program, i.e., Malware Crusher.

Tips to Prevent virus and malware from Infecting Your System:
- Enable your popup blocker: Pop-ups and ads on the websites are the most adoptable tactic used by cybercriminals or developers with the core intention to spread malicious programs.
So, avoid clicking uncertain sites, software offers, pop-ups etc. and Install a powerful ad- blocker for Chrome, Mozilla, and IE
- Keep your Windows Updated: To avoid such infections, we recommend that you should always keep your system updated through automatic windows update.By doing this you can keep your device free from virus.According to the survey, outdated/older versions of Windows operating system are an easy target.
- Third-party installation: Try to avoid freeware download websites as they usually install bundled of software with any installer or stub file.
- Regular Backup: Regular and periodical backup helps you to keep your data safe in case the system is infected by any kind of virus or any other infection.Thus always backup important files regularly on a cloud drive or an external hard drive.
- Always have an Anti-Virus: Precaution is better than cure. We recommend that you install an antivirus like ITL Total Security or a good Malware Removal Tool like Download Virus RemovalTool
