Vurten ransomware - Demands huge $10,000 ransom to restore the files.
Are you a victim of Vurten Ransomware?
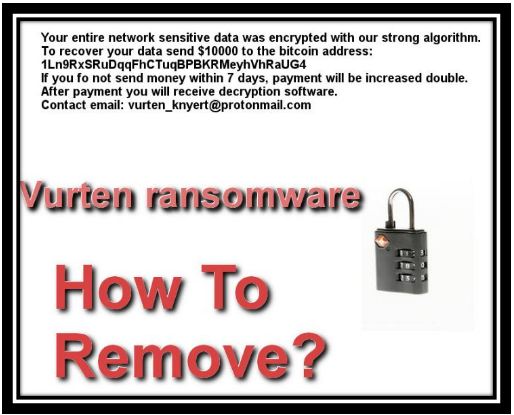
An outrageous amount of $10,000 ransom is what you need to pay to get your files and data restored.
Cybersecurity experts recommend that you need an excellent Anti-Ransomware tool to delete Vurten Ransomware from your system completely.
Download today Free Malware Removal Tool for 360-degree safety against nasty Ransomware.
What is Vurten Ransomware?
The internet landscape is filled with a plethora of different Ransomware, ready to dive on its next victim.
Vurten Ransomware is the latest addition to the family of malware.
It has taken Ransomware attack to an entirely new level and asks for an insane amount of Ransom money, $10,000 is the amount it takes as ransom to supposedly decrypt the encrypted files on your computer.
Vurten is a very cunning and disturbing encryption Ransomware.
It is a harmful creation of cyber criminals that infects your computer and locks your necessary files with a sophisticated encryption algorithm.
As most Ransomware viruses, it holds back your data to be able to make money.
How to remove Vurten Ransomware if Vurten infects your PC and you are not able to access your files, continue reading this blog to get answers to all your queries.
Vurten Ransomware Process and Description
Vurten is malicious malware that can ruin all the personal data stored on your computer system. It is a deadly creation of cyber crooks, specially developed to make data unreadable and earn ransom.
This dangerous threat enters your computer by bundling itself with freeware and shareware programs, third-party download offers, spam email attachments, P2P sharing, Torrent and contaminated web links.

A single click on any of these links can result in a compromised PC.
Once Vurten is successfully installed on your PC is alters the functioning of default firewall and other security software to avoid detection.
It sits in the background of your computer silently and starts using a highly sophisticated encryption algorithm to encrypt essential and confidential files stored on your computer.
Vurten Ransomware process includes changing and modifying data by adding its extension to the end making then useless for the owner.
It adds extension “.improved” at the end of files name to encrypt them entirely and by doing this Vurten makes the data utterly inaccessible to the user and starts demanding ransom.
Post data encryption it drops a ransom note on your computer screen along with the instructions for data decryption and payment details.
Additionally, it keeps displaying the ransom note whenever the user tries to access encrypted files.
Vurten is a typical Ransomware with a whole sole motive of earning ransom; it keeps using ransom notes which states that there is no way to recover locked data than to pay payment to scare users.
Ransom is demanded in the form of cryptocurrencies like Bitcoin.
Caution Note: Paying Ransom does not promise data decryption.
Users should be fully aware that paying ransom will not solve this deadly problem.
File decryption was never the motive of cyber-crooks, and you will never receive a decryption key.
Getting rid of Vurten Ransomware and efficiently shielding your computer against malware is the need of the hour.
Using right Ransomware removal tool is the most appropriate solution.
Distribution Campaign used by Vurten Ransomware
Ransomware viruses are known to use highly misleading distribution techniques. Below mentioned are the most commonly spreading methods used by Vurten.
•Malspam/ Spam Emails: Spam emails are the most widely used carriers of system threats.
These deceptive emails contain contaminated web links and infected attachments and masquerade itself as mail from popular platforms.
Do not fall prey to shady emails, if the source is not known it is advised that you report it spam and delete it.
•Fake Software Updates: Software update notification is often loaded with virus and is known to exploit system vulnerabilities resulting in a compromised PC.
•Illegal Websites: Vurten gets inside your PC through unauthorized and unsafe sites like Porn and adult sites. Often these sites are filled with misleading ads which can redirect the victim to shady media sites.
•Freeware and Shareware Software: Harmful virus conceal themselves with freeware installation. Vurten comes bundled with freeware and shareware programs available online and gets automatically downloaded.
•Social Clickjacking: Social Media is spreading its roots at a skyrocketing speed and so is its use by cybercriminal for spreading malware and other malicious system threats.
•Torrent and P2P files: Online media is a ready platform available for hijackers for spreading system threats. Torrent sites are used to deploy various trick including fake download buttons. A single click on a wrong button can open the ways for Ransomware to get downloaded to your computer.
The list as mentioned above is not an extensive one, and there are numerous other ways by which Ransomware can infect your PC.
Keeping a reputable and efficient malware removal program will delete Vurten Ransomware quickly from your system.
Why should you remove Vurten Ransomware?
If you agree with the presence of Vurten Ransomware on your computer system, it can potentially damage and encrypt your personal and necessary files, making them completely inaccessible, with the risk of losing it entirely.
As per cyber researchers, it is capable of exploiting system vulnerabilities and also provide unauthorized access to your computer to remote hackers resulting in identity theft.
Loss of data, loss of money, performance degradation are other deadly reasons which make it more essential for you to remove Vurten Ransomware.
There is no denial of the fact the Vurten is a severe piece of infection used to extract money from innocent users, Cleaning Vurten Ransomware is highly essential for the protection of system file and data.
How to Remove Vurten Ransomware?
Paying ransom does not guarantee that you will receive decryption keys for restoring encrypted data. Recovering data post-invasion is very difficult.
Go with experts’ advice, uses an excellent anti Malware tool to shield your system against Vurten virus.
Download today Free Malware Removal Tool to save your computer.
Let’s here take a close look at the download procedure of Free Malware Removal Tool.
• Download Free Malware Removal Tool using the below-attached link.
• Install and click on Run button.
• Post successful installation performs complete Start Scan.
• List of all detected infection will be displayed on your PC.
• Click on the fix now button to clean Vurten virus entirely from your system.
Also, Read: FacexWorm - Malicious Chrome Extension Spreads via Facebook Messenger
Tips to Prevent virus and malware from Infecting Your System:
- Enable your popup blocker: Pop-ups and ads on the websites are the most adoptable tactic used by cybercriminals or developers with the core intention to spread malicious programs.
So, avoid clicking uncertain sites, software offers, pop-ups etc. and Install a powerful ad- blocker for Chrome, Mozilla, and IE
- Keep your Windows Updated: To avoid such infections, we recommend that you should always keep your system updated through automatic windows update.By doing this you can keep your device free from virus.According to the survey, outdated/older versions of Windows operating system are an easy target.
- Third-party installation: Try to avoid freeware download websites as they usually install bundled of software with any installer or stub file.
- Regular Backup: Regular and periodical backup helps you to keep your data safe in case the system is infected by any kind of virus or any other infection.Thus always backup important files regularly on a cloud drive or an external hard drive.
- Always have an Anti-Virus: Precaution is better than cure. We recommend that you install an antivirus like ITL Total Security or a good Malware Removal Tool like Download Virus RemovalTool
