Office 365 Phishing Attacks Uses Malicious Links to Steal Credentials

A new phishing campaign is targeting Office 365 customers to steal their credentials. PhishPoint campaign spreads via emails contain SharePoint document. However, upon clicking the email, a file of malicious URL snatches users’ credentials.
Phishing attacks are evolving because instead of emails, hackers are now using SharePoint documents. The Phishing attack technique has infected Office 365 via SharePoint document to harvest credentials.
So far, the campaign has impacted 10 percent of Office 365 customers globally. On the other hand, Microsoft did not respond to the situation.
Michael Landewe, the founder of Avanan, said;
The phishing campaign came into existence three weeks ago. The attack was first carried on pre-compromised accounts and then on compromised accounts.
Avanan researchers first discovered the campaign. According to them, the victim receives an email containing a link to a SharePoint document. The email message is identical to a standard SharePoint invitation to collaborate.
How PhishPoint Attack Works?
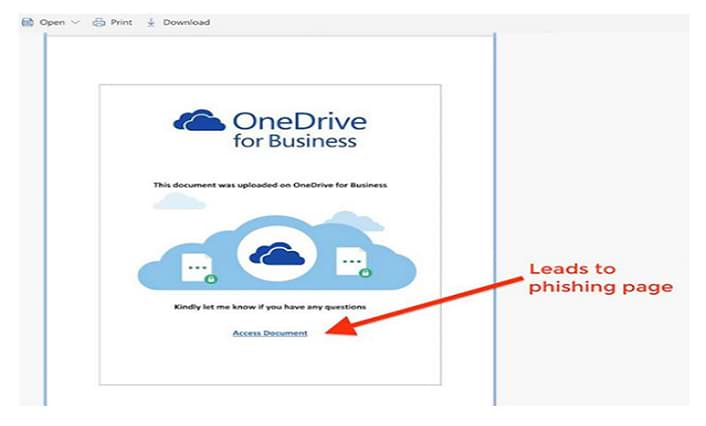
On clicking the hyperlink, the victim’s browser automatically opens a SharePoint file. This file content copy a standard access request to a OneDrive file, with an ‘Access Document’ hyperlink which actually is a malicious URL.
Office 365 scan links in email bodies, but the link leads to an actual SharePoint document and Microsoft did not identify it as a threat.
Microsoft scans the link but not the files hosted within the link. Therefore, the SharePoint document is used. The link inside the SharePoint document directs the user to a fake Office 365 login screen.
Later when user access Office 365 by logging in, hackers harvest their credentials. If the user uses new credentials, the attackers upload a file into users’ SharePoint account. This file sends an invite link from SharePoint which allows the user to access new credentials.
For now, only small companies are being targeted in the USA and Europe. As the phishing attacks adopt new tactics, spams are increasing. Spam emails, in particular, is a top phishing tactic.
The average share of spam in email traffic worldwide until now in 2018 is 50 percent.
Protect Phishing Attacks
To prevent these phishing threats, Microsoft needs to do a deep scan of documents for phishing URLs. Even if Microsoft scan links and blacklists the full URL of the Sharepoint file, the hackers will recreate a new URL.
Thus, the best solution is to implement multi-factor authentication and invest in anti-phishing training programs. Since these attacks are indistinguishable and appear safe, the user should check the legitimacy of a login page.
However, if such attacks involve malware links, the damage by the time will become more.
To stop this next-generation future attack, we recommend using the free malware removal tool.

Get peace of mind! Get rid of malicious programs instantly
Free Checkup & fix for your PC! Get rid of malicious programs instantly!
