Bip Ransomware - CrySis and Dharma’s New Variant
Nowadays, ransomware attacks appear out from nowhere and attack private organizations, hospitals, colleges, universities and statutory bodies of the government without letting anyone know about it.
Tons of ransomware are being developed to hack into the computers especially Windows computer to extort money from the users.
Cybersecurity researchers disclosed reports on new ransomware supposedly a blend of CrySis and Dharma ransomware. This new variant is Bip Ransomware which is also a destructive file-encrypting threat as like most of the ransomware.
What is Bip Ransomware?
Bip ransomware is a file-encrypting malware that usually gets inside the system via malicious email and process data encryption. It is a new variant of the ransomware that appends .bip extension.
Like all other ransomware, it is also a file-encrypting malicious code that hijacks your computer to encrypt photographs, music records, business reports, pdfs, docs and all other data only after utilizing file lock and encryption techniques like AES/RSA.
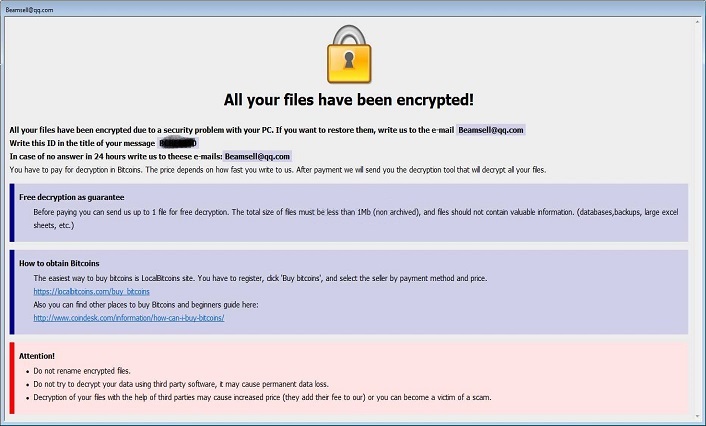
To lock any file, the ransomware always adds the extension in the format .id-[id].[email].bip. For example, filename.jpg firstly is encrypted, then is renamed to filename.jpg.id-BCBEF350.[Beamsell@qq.com].bip.
Typically, it spreads after it hacks into remote network computers and desktop services. It should also be noted that this dangerous ransomware encrypts mapped network drives, unmapped networks, host drives and shared virtual machines.
The ransomware also creates two different ransom notes Info.hta file and FILES ENCRYPTED.txt. The message within the note is same that tells users to pay ransom in bitcoins to get back the access of encrypted files.
Eventually, once the payment is done the ransomware developers in the note claims to free your system unharmed. However, from the reports gathered by HTRI’s cybersecurity expert, this claim was found misleading the victims of Bip ransomware.
Typical of like ransomware, this claim is false and once the payment is done, the cyber attackers demand more money rather than leaving the system. We suggest you to never make payment and must find a way to delete .bip ransomware files.
Here we would recommend you to install a robust antimalware tool named Malware Crusher to prevent the entry of ransomware into your computer.

Report On Bip Ransomware
Recently, we received information from a victim of .bip attack. He was asked to pay 2000 dollars for the data recovery. However, after spending 500 dollars, he didn’t receive any decryption key.
Warning: The ransomware frauds with their victims and extort money from them. Instead of giving bip ransomware decryption keys, they demand more money and leaves you with those same locked files.
Therefore, wasting your time and money on deals with cybercriminals is not the right way to solve the ransomware infection. The safest method is to follow a few prevention steps and a removal guide that never allows such ransomware to enter again into your system.
It quickly spreads through spam emails, websites, peer to peer file sharing, freeware (fake software updates), cracked or pirated software and social hijacking. It degrades the computer performance and compels you to pay money for your files within some time limit.
Once victimized, the ransomware attacks your system, web browsers settings and corrupts hard drive of the computer. Applications do not respond sometimes and adequately lack few important program files.
Cybercriminals via these threats steal information like IP address, URL’s Search, browser history, search queries, username, ID, passwords, banking information and ATM Card information.
Are There Decryptors For .Bip Ransomware?
No, it is nearly impossible to recover all the locked files as the encryption algorithm is strong and runs on private keys of malicious programmers. Therefore, as of now, it is quite notable that forging out any decryption key and tool is not realistic as.
Moreover, to make any decryption tool it is important to reverse engineer the program code of ransomware’s encryption mechanism. Unfortunately, more time is required to break down the AES/RSA mechanism.
As per security experts, presently .Bip ransomware decryptor tool is not present and is yet to be developed. And if the keys exist, then on the first hand it would be with the developers of .Bip ransomware.
Since there is no decrypt tool to recover your files, we recommend taking some preventive measures against the attacks of CrySis and Dharma ransomware variant Bip.
Gain Entry In Computer By Safe Mode with Command Prompt
Steps to be followed to enter the safe mode Win XP/Vista/7
- Click start, then shut down, then restart.
- While the computer is booting up at the very first screen start tapping F8 until you see the advanced boot options.
- In the advanced boot option’s, you need to select safe mode with Command prompt from the list of given options.
Steps to be followed to enter safe mode in Win 8/10
- On the windows login screen, you need to press the power option.
- Now, press and hold the shift key on the keyboard, and then click Restart.
- Now, among the list of options you need to select Troubleshoot, and then advanced options, then startup settings and finally press restart.
- Once your computer restarts and gives you the list of startup options you need to select Enable Safe Mode with Command prompt.
Restore System
- Once you see the command prompt windows, type in cd restore and hit enter on the keyboard.
- Now, type rstrui.exe and hit Enter again.
- Then you would see new windows, click on next over there and select a restore point that is before the date of infection.
- Then, click next and followed by yes.
At present, your computer is in a state that has its file and data backed up at a safe restore point. We also suggest you to make a copy of your backed up data into some external hard drive.
It is now time, to reinstall your Windows via an external source such as pen drive, CD or DVD.
While installing Windows, allocates disk space to C,D and E drive. If asked to restore any files, select the restore point and get the backed up data into the new operating system.
Your system format is complete and new Window installation is over. Now you must create a strong firewall against such malicious threats to prevent cyber attacks.
If you do not have any security software, then download Malware Crusher.
If you didn’t find the backed up data, then you can use the pen drive to copy all the data. Malware Crusher will not allow the corrupt data to enter in your computer in order to keep your system away from Bip ransomware attack.

Prevent Entry Of Bip Ransomware
Malware Crusher is the most commonly used anti-malware software for the Windows computer. It’s malware removal capabilities makes it the most impactful tool and prevents you before the ransomware starts infecting your system because:
- It’s real-time protection feature, performs a deep scan, detects malicious software and infected encrypted files within your system.
- The Quarantine feature of the tool removes all infected files from your computer. Additionally, keeps a record of all deleted malicious program.
- Malware Crusher also creates a shield against Ransomware, Adware, Malware, Browser Hijackers, Viruses, Extensions and Trojans from entering into your system.
- The 24X7 online protective shield works as an anti-exploit technology and blocks the ransomware component before they hold files as a hostage.
- Malware Crusher tirelessly visits all domains, URLs and web pages to secure your online presence from fraudulent entities.
- Malware Crusher becomes fiercer in detecting keylogging, remote connections and saving your session data from being recorded.
To get a better security awareness on preventing cyber attacks and cyber security threats keep visiting us, forget not to download Malware Crusher.
Its 5-minute function could be a savior for your Windows computer!
If you wish to get more news and awareness on the happenings of the cybersecurity, then keep visiting us.
Tips to Prevent virus and malware from Infecting Your System:
- Enable your popup blocker: Pop-ups and ads on the websites are the most adoptable tactic used by cybercriminals or developers with the core intention to spread malicious programs.
So, avoid clicking uncertain sites, software offers, pop-ups etc. and Install a powerful ad- blocker for Chrome, Mozilla, and IE
- Keep your Windows Updated: To avoid such infections, we recommend that you should always keep your system updated through automatic windows update.By doing this you can keep your device free from virus.According to the survey, outdated/older versions of Windows operating system are an easy target.
- Third-party installation: Try to avoid freeware download websites as they usually install bundled of software with any installer or stub file.
- Regular Backup: Regular and periodical backup helps you to keep your data safe in case the system is infected by any kind of virus or any other infection.Thus always backup important files regularly on a cloud drive or an external hard drive.
- Always have an Anti-Virus: Precaution is better than cure. We recommend that you install an antivirus like ITL Total Security or a good Malware Removal Tool like Download Virus RemovalTool
