Brrr Ransomware Compromises Windows Computing Machines
Many times we see our computers getting slow. When you try to start or boot your computer, some freezes and some do not respond. If this happens a lot to your machine then your computer is in infection from some foreign program or software that should not have existed in it.
Due to this unwanted program, you could have suffered data loss, file loss, slow internet speed and importantly data theft. Such program is called Ransomware that infiltrates the computer using AES algorithm, cheat users and makes an illegal profit.
A classified malicious variant of Dharma ransomware named Brrr Ransomware containing all features of malware, viruses, scareware, keyloggers and hijackers is attacking windows based computers.
Ransomware is a tool to carry encryption technique into your computers so that manipulation of computer system becomes easy while infecting servers and internet networks.
You might ask if this threat is infectious then how to remove Brrr ransomware? The answer lies in the below ransomware removal guide.
What is brrr ransomware?
It is a new Brrr Dharma ransomware variant that injects .brrr files virus into the system. First configures the system then encrypt(lock) the files which you executed last time. It then adds .brrr ransomware extension to locked files itself and set an execution pattern.
The Dharma Brrr Ransomware family manually install the ransomware by hacking into the remote computers connected to the internet. On getting access to the computer, the attackers start encryption and changes the file names.
For example, after encryption, test.jpg is renamed to test.jpg.id.EFBCB.brrr
Every time you try to open a locked file, a FILES ENCRYPTED.txt ransom note opens and says;
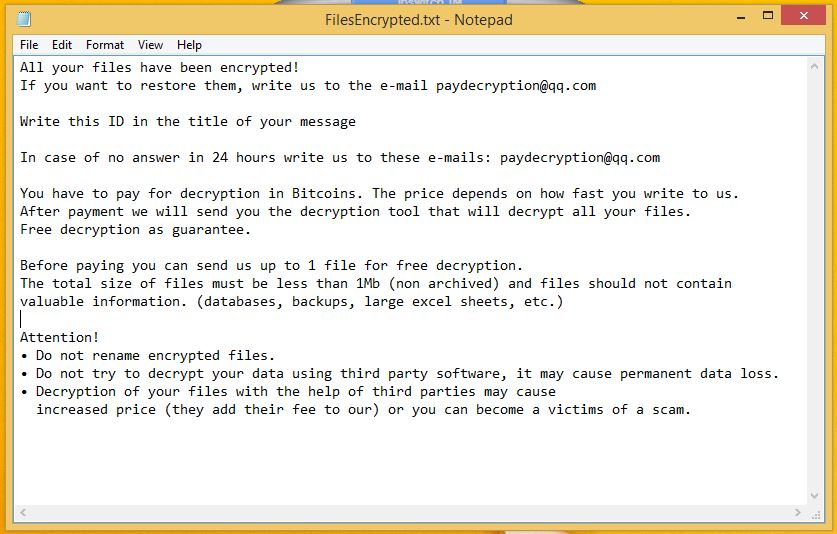
Dharma’s Brrr Ransomware virus also creates an HTML file Info.hta. Both the files share the same message and suggest victim users to contact at paydecryption@qq.com. However, according to security experts, a victim should not contact the developers as it could lead to money extortion. The threat developers demand money and make fake commitments to decrypt .brrr files.
Being said, if not to make payment then what is the option to restore .brr files? The only answer is to prevent the entry of Dharma .brrr ransomware into your computer. But, to do this, you must understand how a ransomware works? What are the possible ways to deal it before it causes more damage to your computer?
The ransomware infection begins with a data harvesting module which mainly gathers sensitive personal information about victims such as names, IP address, phone number, location, stored account credentials etc. Attackers also collect useful information that helps them in planning their next attacks.
The collected data is then processed under stealth protection. To execute the infection via ransomware, the system is scanned for applications or services (anti-virus products, sandbox environments or virtual machine hosts)that might stop the proper execution.
Once data is successfully obtained, system modification is done. The most popular technique is called manipulation of the Windows Registry files. On changing the file in registry editors, users experience computer performance issues and the operating system malfunctions.
Brrr ransomware is a persistent infection that automatically infects and stops certain services. In many cases, this also leads to the inability to enter into the boot recovery menu/ safe mode boot.
The hackers program the ransomware to delete the backup data, System Restore information and Shadow Volume Copies of identified user data. An infected machine suffers more and the ransomware starts ransom module.
It establishes a connection with the attacker-controlled server (C2) and spy on the victims in real time. It further advances its attack and targets the data such as archives, backups, audio - video files, documents, images, databases etc.
However, it is possible to stop this infection. Even more, one can prevent Brrr Ransomware from infecting windows computing machine. To fight against such malicious threat, one must use a strong antimalware tool that makes .brrr files recovery possible. We recommend a strong robust tool, Malware Crusher.

Distribution Ways of Brrr Ransomware
Being a persistent threat, it actively spread using different tactics. Few names of the captured samples are given below which is running the campaign against windows computers:
- Win32: Malware-gen
- TR/Dropper.Gen
- W32.RansomeDNZ.Trojan
- Ransom.Crysis.Generic
- Ransom.Crysis/Variant
- Trojan-Ransom.Win32.Crysis.a
- Trojan-Ransom.Win32.Crusis.to
The first method of distribution is via phishing SPAM messages, malicious URLs, Links that pretends to be sent from a legitimate company or service. These messages are like password reset prompts, software updates or other texts which user can regularly receive on a daily basis.
The criminals also develop malicious download sites and push various pop-ups, ads and redirections to further victimize user into interacting them with the malicious elements. Malicious Javascript found on hacker-controlled pages and community forums of legitimate sites also spread ransomware.
Infected documents like spreadsheets, rich text documents, presentations and databases also spread .brrr files. Once the victim opens these documents, a notification prompt asks the users to enable the built-in macros. Once it is done, the computer infection spreads severely.
The ransomware may inject threats like browser hijackers to spread the ransomware. On installation, the victim user redirects to a hacker-automated site that manipulates the built-in settings such as default home page, new tab page and search engine).
In short, it quickly spreads through spam emails, websites, peer to peer file sharing, freeware (fake software updates), cracked or pirated software and social hijacking. It degrades the computer performance and compels you to pay money to unlock files.
Cybercriminals via these threats steal information like IP address, URL’s Search, browser history, search queries, username, ID/passwords, banking information and ATM Card information.
Therefore, avoiding the infection is not a better choice and we recommend to remove Brrr ransomware. The most important method to get back your files is downloading a reputable antimalware tool.
We also suggest victims to follow the below-mentioned ransomware removal guide for deleting it quickly and prevent your computer from further attacks.
How to Remove Brr Ransomware?
If you can’t access your computer due to Brrr attacks then removing ransomware becomes impossible. However, system reboot in Safe Mode is a short trick that gives you entry into the computer.
Once you are into the computer, perform a full system scan using Malware Crusher after downloading it. This ransomware mainly affects Windows XP, Windows Vista, Windows 7, and Windows 8. Therefore, the below method is purely for the Windows-based computer.
Unlock Your Locked Computer
Steps to be followed to enter the safe mode Windows.
- Start your computer and instantly press F8(Windows 7), F5(Windows 8, 8.1 and 10) repeatedly to enter Advanced Boot Options.
- Log on the computer as the Administrator.
- Change or remove your computer’s forgotten password in Control Panel and enable the safe mode options.
Once you enable the Windows manually, you now have a choice to follow two different methods to prevent the attacks of ransomware. Both the methods are described below;
Automatic Preventive Method
Malware Crusher is the most commonly used anti-malware tool for the Windows computer. It’s malware removal capabilities makes it the most impactful and vigilant tool that prevents your system before the ransomware starts spreading infection;
- It’s real-time protection feature, performs a deep scan to detects malicious software and persistent threats. Also, identifies suspicious behaviour on your computer.
- The Quarantine feature of the tool removes all infected files from your computer. Additionally, keeps a record of all deleted malicious program and allows you to choose important programs to restore at a later time.
- Malware Crusher also creates a shield against Ransomware, Adware, Malware, Browser Hijackers, Viruses, Extensions and Trojans from entering into your system.
- The 24X7 online protective shield works as an anti-exploit technology and blocks the ransomware component before they hold files as a hostage.
- Malware Crusher tirelessly visits all domains, URLs and web pages to secure your online presence from fraudulent entities. Furthermore, the tool detects the vulnerabilities of online fraudulent entities effortlessly.
- Malware Crusher becomes fiercer in detecting keylogging, remote connections and saving your session data from being recorded.
Malware crusher continuously monitors the happenings of cyberworld related security issues. In response to the malicious codes and javascript, the tool writes anti-malware code, diagnose ransomware. Hence, affected Brr ransomware file recovery becomes possible.
After using the tool, you can follow manual methods on a regular basis to keep a watch on pre-installed applications and programs.

Manual Preventive Methods
- Press Ctrl + Shift + ESC together to open Task Manager. Look for suspicious files, right click on it and click End Task.
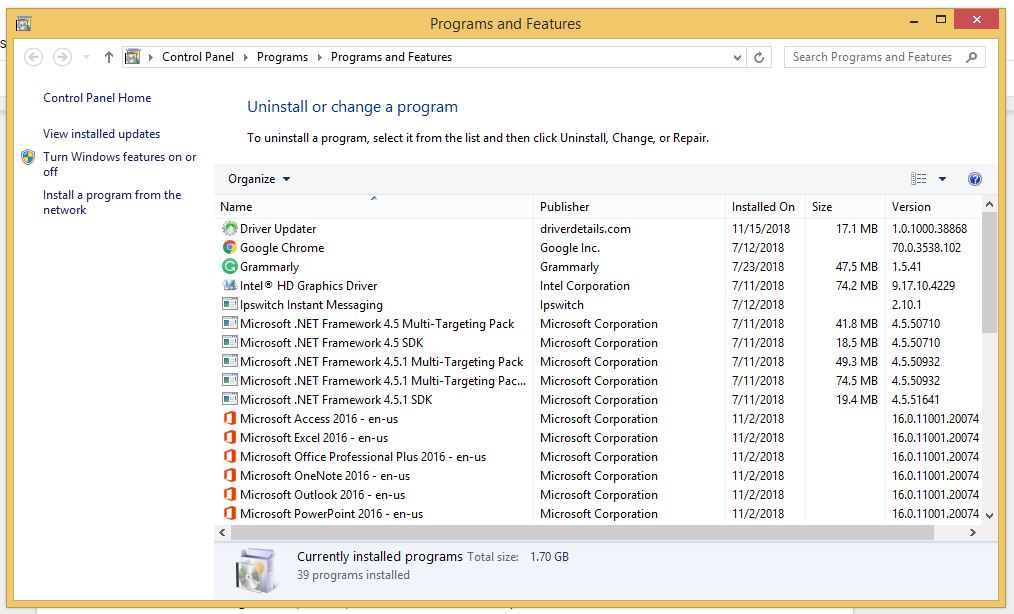
- Now, press it to open RUN box window. Type appwiz.cpl on it, this opens Programs and Features window.
- Select each suspicious program and uninstall it one by one. Once the uninstallation is complete, restart your computer and again redirect yourself to Programs and Features window to check whether the application is present or not.
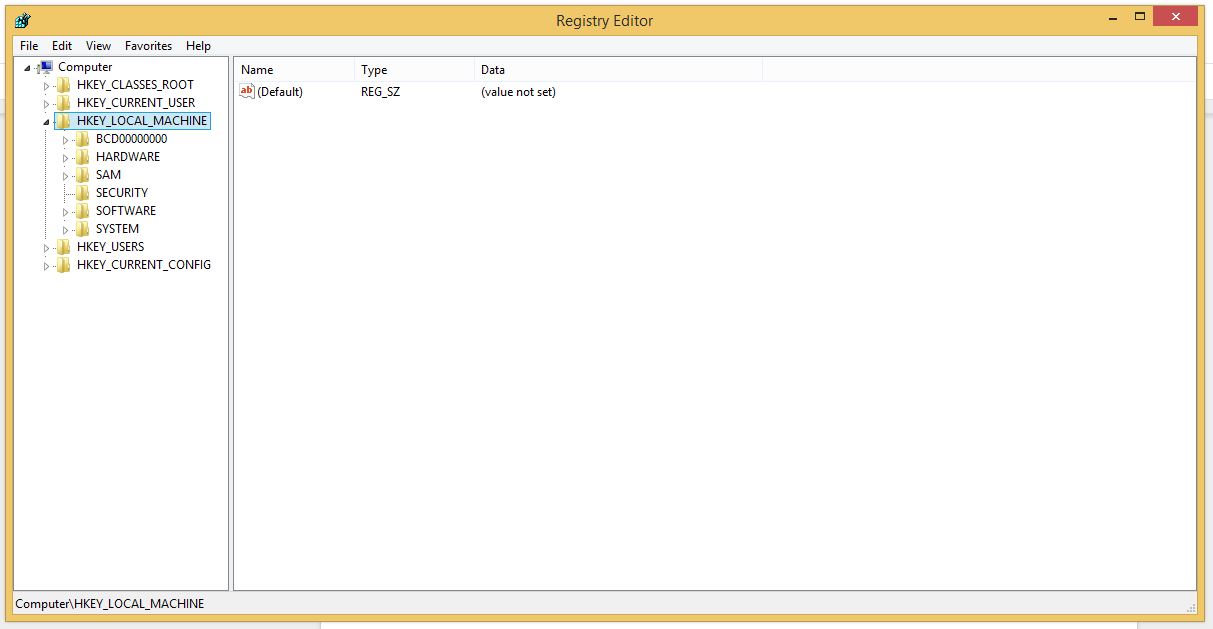
- When convinced, press Windows key + R to open RUN box window. Type regedit on it, hit OK and then click Yes.
- Go through HKEY, HKLM, etc. files and find all suspicious files and delete them.
- You can also delete malicious extensions from your browsers like Chrome and Firefox.
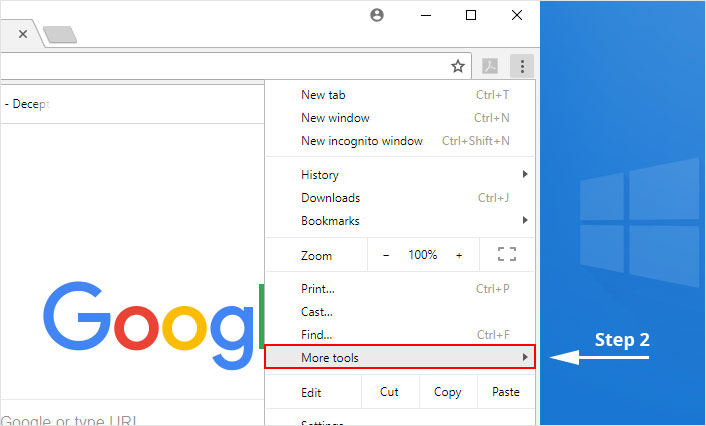
1. Click on the Customize and control menu icon at the top right corner of Google Chrome.
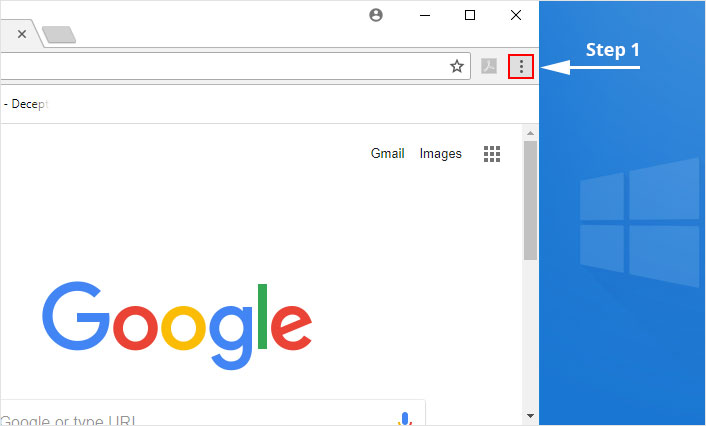
2. Select "More tools" from the menu.
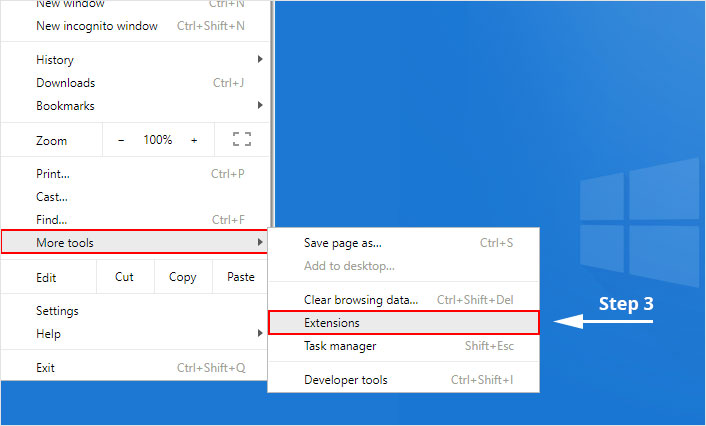
3. Select "Extensions" from the side menu.
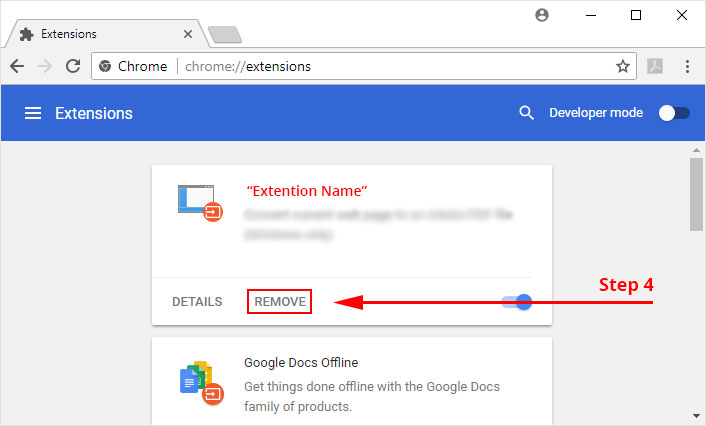
4. Click the remove button next to the extension you wish to remove.
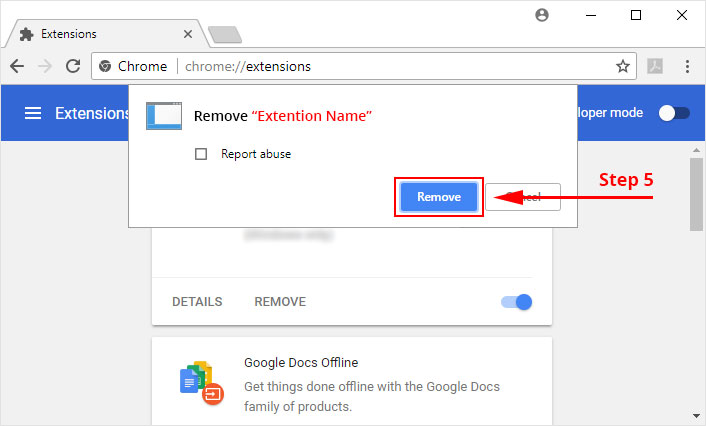
5. It will confirm again, click “remove” and the extension is finally out of the system.
Now that we have successfully eliminated the malicious browser extension, we need to create a robust firewall to avoid any such thing that makes our system and privacy vulnerable to various online threats.
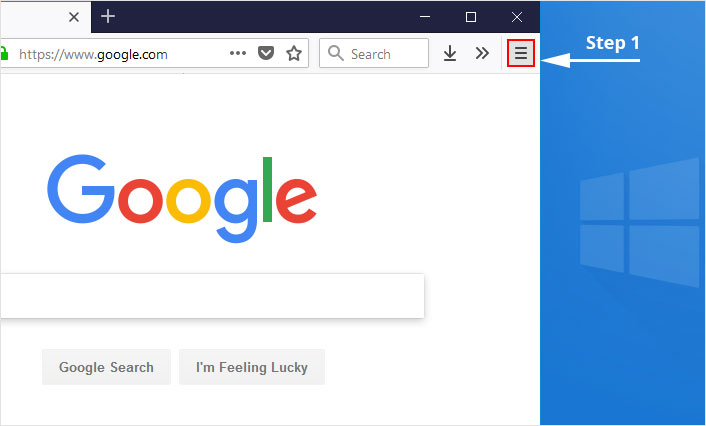
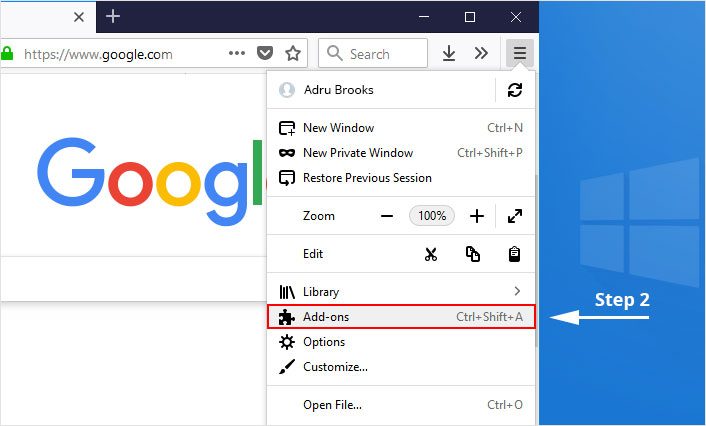
1. Click on the “menu” button at the top right corner.
2. Select “Add-ons” from the menu.
3. Click the “Remove” button next to the extension you wish to get rid of.
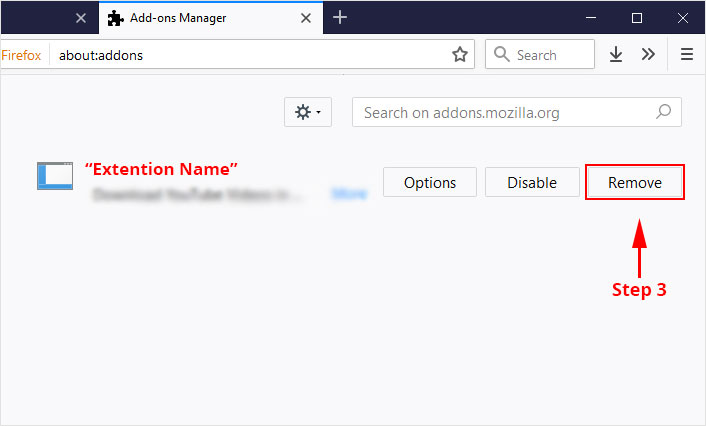
Now that we have successfully eliminated the malicious browser extension, we need to create a robust firewall to avoid any such thing that makes our system and privacy vulnerable to various online threats.
The manual method sometimes might not work at Windows OS because finding suspicious and modified registry files in registry editors is a difficult task. On the other hand, if a useful file deletes, then the windows stop working properly.
That’s why it is highly recommended to use an automatic tool to prevent cyberthreat attacks on your computer. If you wish to get more news and awareness on the happenings of the cybersecurity, then keep visiting us.
To get a better security awareness on preventing cyber-attacks and internet security threats, keep visiting us and forget not to download Malware Crusher. Its 5-minute function could become a savior for your Windows computer.
Tips to Prevent virus and malware from Infecting Your System:
- Enable your popup blocker: Pop-ups and ads on the websites are the most adoptable tactic used by cybercriminals or developers with the core intention to spread malicious programs.
So, avoid clicking uncertain sites, software offers, pop-ups etc. and Install a powerful ad- blocker for Chrome, Mozilla, and IE
- Keep your Windows Updated: To avoid such infections, we recommend that you should always keep your system updated through automatic windows update.By doing this you can keep your device free from virus.According to the survey, outdated/older versions of Windows operating system are an easy target.
- Third-party installation: Try to avoid freeware download websites as they usually install bundled of software with any installer or stub file.
- Regular Backup: Regular and periodical backup helps you to keep your data safe in case the system is infected by any kind of virus or any other infection.Thus always backup important files regularly on a cloud drive or an external hard drive.
- Always have an Anti-Virus: Precaution is better than cure. We recommend that you install an antivirus like ITL Total Security or a good Malware Removal Tool like Download Virus RemovalTool
