Remove KCTF Locker Ransomware Without Paying Money
KCTF Locker ransomware also called as KCTF Virus is a file-encrypting virus that usually alters data into the infected system by XOR encryption technique.
It is a classified new variant of the Cryptovirus which may be persistent into your systems. Once the ransomware enters into your system, it demands money to decrypt the locked files.
Research from cybersecurity experts concludes;
Most of the times users pay the ransom (sometimes in BTC) but don’t get decrypting keys to recover their locked files. Thus, it is necessary to find out a legitimate method for removing ransomware.
This article aids you to remove KCTF Locker cryptovirus. Follow this ransomware removal guide to bring back your system to safety.
What is KCTF Locker Ransomware?
It is a file-encrypting virus that claims to be used for educational purposes though no Institution and educational organization is linked to it.
Samples of the ransomware come from an IP address located in East Asia. Researchers also assume its origination somewhere nearby East Asian Cultural Sphere.
The ransom note of KCTF LOCKER, typically states that your files are encrypted and the victim must pay 10 BTC to get them restored.
The main target of this threat is Japanese-speaking people!
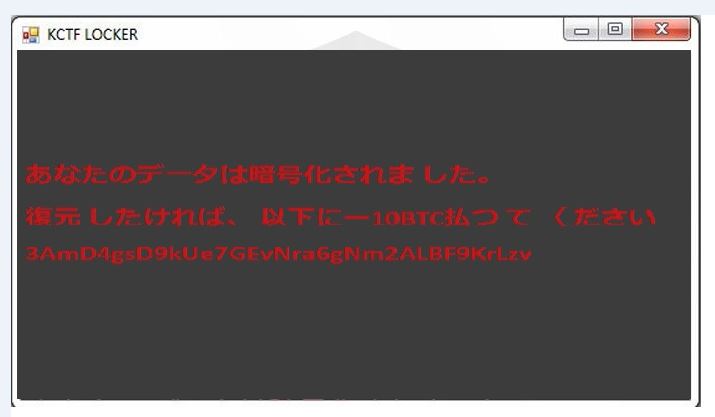
Researchers also speculated that the ransomware locks your screen after which you can’t access files anymore.
How KCTF Locker ransomware infects system?
Cybersecurity experts confirmed that KCTF cryptovirus uses XOR encryption technique to modify data on infected systems. For this, the ransomware locks the file and give them .DWG extension.
For instance, 'Nvidia GTX 1050 Ti.pptx' is renamed to 'Nvidia GTX 1050 Ti.pptx.DWG.'
The KCTF Locker ransomware and other ransomware like .skype ransomware, arena ransomware, redboot ransomware, etc all use names of legitimate applications to hide their respective operations.

The KCTF Locker cryptovirus could erase all the Shadow Volume Copies from the Windows operating system from the following command:
→vssadmin.exe delete shadows /all /Quiet
The widely used files by users are Audio files, Video files, Document files, Image files, Backup files, Banking credentials, etc.
Hackers and cyber attackers widely use Spam email campaigns to spread KCTF Locker ransomware virus on the system. The minute you open it, cryptovirus installs and infects the system.
The open safe looking emails actually lure people, but on clicking them, it downloads macro-virus in other words, a direct malware script. The developers hide malware script into well-known logos and pictures of companies.
And the requirement of a tool that can create a shield against file-encrypting ransomware increases.
Effects Of KCTF Locker Ransomware
KCTF Locker Ransomware infects a computer in a various number of nasty irritating manners as given below:
- Polymorphic: It carries many types of cryptovirus variants, remains undetected and ordinary antivirus tool cannot locate it.
- Identity Theft: It posses keyloggers to monitor your keystrokes additionally sends information to hackers. It also steals your sensitive and financial information.
- Copycat Look: Developed in a manner that it represents an original program to cheat innocent users, but doesn’t contain any genuine features of the application.
- Memory Resident: After entering into the system it remains in the memory of the system and automatically gets executed.
- Poor Detection: All the working Security application blocks, so it becomes unable to detect any other incoming threat.
- Fake scanning property: It performs bogus system scanning on the screen and shows fake results.
- Transferable: It easily duplicate itself and transmit from one infected system to another via network vulnerabilities and security checkup loopholes.
The infections caused by KCTF Ransomware are intrusive and also spy on the system. Furthermore, keeps an eye on our activities before blocking access to the system. Thus, it is important to delete KCTF Locker ransomware from the system.
Cybercriminals via these threats steal information like IP address, URL’s Search, browser history, search queries, username, ID, passwords, banking information and ATM Card information.
If you are an infected user of this ransomware, then our KCTF Locker ransomware removal guide will be helpful to you to fix your system on your own.
If you do not have any security software, then download a reliable software for KCTF Locker ransomware removal. But before that, you can use a few manual methods to see whether they can work against ransomware or not.
Temporarily Disable KCTF Locker Ransomware
Windows Safe Mode Options
Steps to be followed to enter the safe mode Win XP/Vista/7.
- Click start, then shutdown, then restart.
- While the computer is booting up at the very first screen start tapping F8 until you see the advanced boot options.
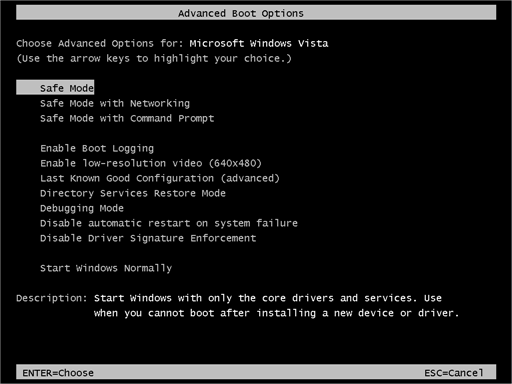
- In the advanced boot option’s, you need to select safe mode with Command prompt from the list of given options.
Steps to be followed to enter safe mode in Win 8/10.
- On the windows login screen, you need to press the power option.
- Press and hold the shift key on the keyboard, and then click restart.
- Now, among the list of options you need to select Troubleshoot, and then advanced options, then startup settings and finally press restart.
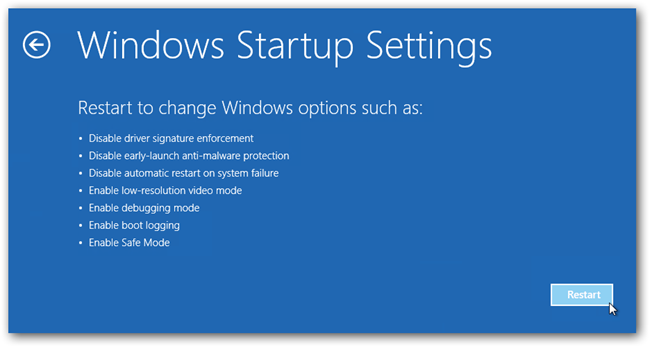
- Once your computer restarts and gives you the list of startup options you need to select Enable Safe Mode with Command prompt.
Windows System Restore
- Once you see the command prompt windows, type in cd restore and hit enter on the keyboard.
- Now, type rstrui.exe and hit Enter again.
- Then you would see new windows, click on next over there and select a restore point that is before the date of infection.
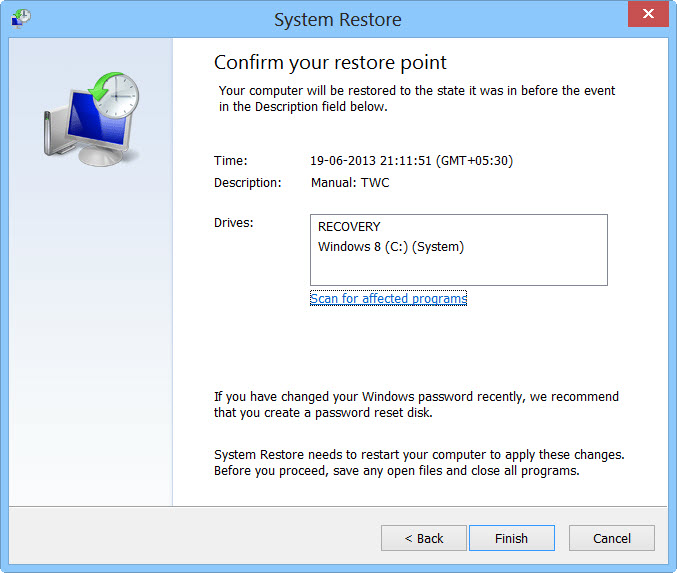
- Then, click Finish and followed by yes.
But here's something you should never forget: Following these steps, you might get rid of the malware from your PC and restore admin rights, but it won't decode your documents.
After temporarily disabling the ransomware, we need to create a strong firewall to fight against such intrusions and prevent them in the future. For this, you must follow the automatic KCTF Locker ransomware removal guide.
How to prevent KCTF Locker Ransomware Automatically?
You see a KCTF ransom note where the cyber attackers ask for money. But, we recommend you never to pay the ransom and if the issue is not solved by uninstalling and removing unwanted programs, you can use this automatic prevention method.
Malware Crusher prevents you from KCTF Locker ransomware attacks before it starts infecting your system.
It can be your permanent ally due to its following removal capabilities;
- It’s a real-time protection feature, performs a deep scan, detects malicious software, infected encrypted files within your system.
- The Quarantine feature of the tool removes all infected files from your computer in addition to keeping a record of all deleted malicious program.
- Malware Crusher also creates a shield against Ransomware, Adware, Malware, Browser Hijackers, Viruses, Extensions and Trojans from entering into your system.
- The 24X7 online protective shield works as an anti-exploit technology and blocks the ransomware component before they hold files as a hostage.
- Malware Crusher tirelessly visits all domains, URLs and web pages to secure your online presence from fraudulent entities.
- Malware Crusher becomes fiercer in detecting keylogging, remote connections and saving your session data from being recorded.
To get a better security awareness on preventing cyber attacks and cyber security threats keep visiting us, forget not to download Malware Crusher. Its 5-minute function could be a savior for your Windows computer!

Tips to Prevent virus and malware from Infecting Your System:
- Enable your popup blocker: Pop-ups and ads on the websites are the most adoptable tactic used by cybercriminals or developers with the core intention to spread malicious programs.
So, avoid clicking uncertain sites, software offers, pop-ups etc. and Install a powerful ad- blocker for Chrome, Mozilla, and IE
- Keep your Windows Updated: To avoid such infections, we recommend that you should always keep your system updated through automatic windows update.By doing this you can keep your device free from virus.According to the survey, outdated/older versions of Windows operating system are an easy target.
- Third-party installation: Try to avoid freeware download websites as they usually install bundled of software with any installer or stub file.
- Regular Backup: Regular and periodical backup helps you to keep your data safe in case the system is infected by any kind of virus or any other infection.Thus always backup important files regularly on a cloud drive or an external hard drive.
- Always have an Anti-Virus: Precaution is better than cure. We recommend that you install an antivirus like ITL Total Security or a good Malware Removal Tool like Download Virus RemovalTool
