Remove .tro Ransomware From Computer
Browsing the web is always entertaining, but it could be dangerous when a dreadful infection like ransomware, trojan or any other form of malware enters into your computer on clicking a malicious URL or a wrong website.
Nowadays, the internet is not a secure place to keep your personal information logged in 24x7. Anonymous hackers somehow using various online techniques, leave a malicious program into your computer to impact the operating system’s performance to a large extent.
One such unwanted program that should never exist in your computer is .tro Ransomware designed to encrypt data and files. In other words, locking down files, data, online information, etc. in a computer without user’s permission.
If your documents, music, photos, web pages, etc. don’t open normally due to a .tro file extension added at the end of their file names then your machine is infected due to .Tro ransomware virus.
Once launched, it locks all the stored files on a computer, stops drives from functioning normally and blocks the network drives. It is malicious software that hijacks your system by locking files and other software.
What is .Tro Ransomware?
.Tro ransomware is a file-encrypting malware that usually gets inside the system via malicious email and process data encryption.
Like all other ransomware, it also encrypts photographs, music records, business reports, pdf, docs and all other data by using encryption techniques like AES/RSA.
To lock any file, the ransomware always adds the .tro extension. For example, filename.jpg encrypts and changes to filename.jpg.tro.
Typically, it spreads after it hacks into remote network computers and desktop services. It should also be noted that this dangerous ransomware encrypts mapped network drives, unmapped networks, host drives and shared virtual machines.
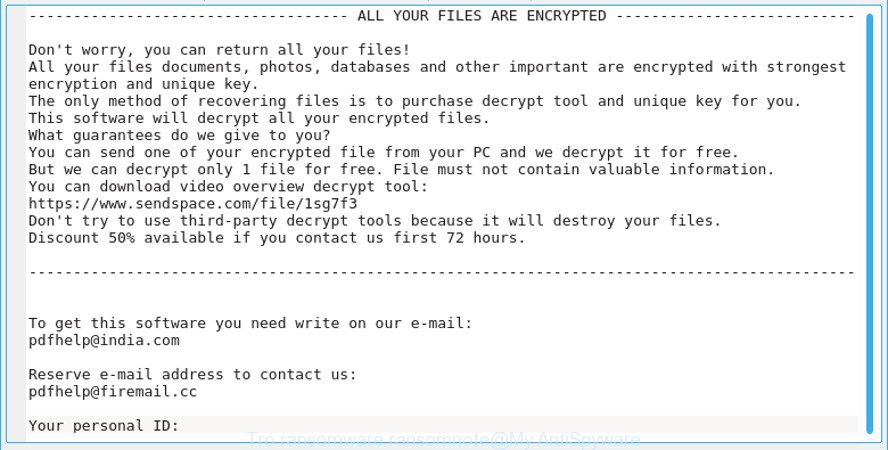
On clicking any locked file, a ransom note named _openme.txt opens. Like every other note, the message tells users to pay ransom in bitcoins to get back the access to all the encrypted files.
Eventually, once the payment is done the ransomware developers in the note claims to free your system unharmed. However, from the reports by cybersecurity expert, this claim from .tro ransomware authors is wrong.
Like other ransomware, in .tro ransomware case, once the payment is done, the cyber attackers demand more money rather than leaving the system. We suggest you to never make payment and must find a way to delete .tro ransomware files.

Are There Decryptors For .tro Ransomware?
No, it is nearly impossible to recover all the locked files as the encryption algorithm is strong and runs on private keys of malicious programmers. Therefore, as of now, it is quite notable that forging out any decryption key and tool is not realistic.
Moreover, to make any decryption tool it is important to reverse engineer the program code of ransomware’s encryption mechanism. Unfortunately, more time is required to break down the encryption mechanism. Therefore, cybersecurity experts aren’t in a state to help victims in removing ransomware from the victim's computer.
As per security experts, presently .tro ransomware decryptor tool is not present and is yet to be developed. And if the keys exist on the first hand, it would be with the developers of .tro ransomware.
Since there is no decryption tool to recover your files, we recommend taking some preventive measures.
Note: Tro ransomware belongs to the family of Djvu ransomware.
Harmful Impacts of .tro Ransomware File Virus on Computer
- Alters your Windows-based computer files without your permission.
- Blocks some important applications like antiviruses, system settings, firewall settings and command prompt.
- This malware locks files of games, ppt, pdfs, docx,xlx and other files.
- Cyber attackers use names and logos of different trustworthy companies to make ransom note and make it believable to the users.
- It highly affects your web browsing experience and shows irrelevant search results.
- It tricks you into installing other malicious apps and malware which brings more problems.
- BSOD (Blue Screen of Death) errors in Windows.
- Keeps a record of your IP address, browser history and activities, passwords, bank account details, etc. in your system.
- Infect external media drivers.
Research shows that .tro files virus makes your computer vulnerable to remote attacks and use the following techniques to inject ransomware into your computer. It also posses some properties related to Cryptomix ransomware responsible for increasing botnets.
- Social Clickjacking
- Spam emails
- Torrents and P2P file sharing
- Bundling
- Freeware (fake software updates)
This let the attackers behind the ransomware obscure the contents of the computer such that users couldn’t recognize it nor could use it. We never advise victims of the .tro Ransomware to agree and cooperate with the criminals when they demand money.
Instead, we suggest victims to follow the below-mentioned .tro ransomware removal guide for deleting .tro ransomware completely from computers.
Gain Entry In Computer By Safe Mode with Command Prompt
Steps to be followed to enter the safe mode Win XP/Vista/7
- Click start, then shut down, then restart.
- While the computer is booting up at the very first screen start tapping F8 until you see the advanced boot options.
- In the advanced boot option’s, you need to select safe mode with Command prompt from the list of given options.
Steps to be followed to enter safe mode in Win 8/10
- On the windows login screen, you need to press the power option.
- Now, press and hold the shift key on the keyboard, and then click Restart.
- Now, among the list of options you need to select Troubleshoot, and then advanced options, then startup settings and finally press restart.
- Once your computer restarts and gives you the list of startup options you need to select Enable Safe Mode with Command prompt.
Restore System
- Once you see the command prompt windows, type in cd restore and hit enter on the keyboard.
- Now, type rstrui.exe and hit Enter again.
- Then you would see new windows, click on next over there and select a restore point that is before the date of infection.
- Then, click next and followed by yes.
At present, your computer is in a so-called safe state with backed up data at a safe restore point. We suggest you to make a copy of your backed up data into some external hard drive as if something goes wrong then at least your recovered data will be safe.
It is now time, to reinstall your Windows via an external source such as pen drive, CD or DVD. get a pen drive or CD having an original setup of Windows. Install the new windows and allocate disk space to C,D and E drive.
If asked to restore any files, select the restore point and get the backed up data into the new operating system. And if not, then use the external hard drive to copy the data back to your computer.
Your system format is complete. Now you must create a strong firewall against such hideous ransomware to prevent the future attacks.
If you do not have any security software, then download Malware Crusher to prevent .tro ransomware attacks.

Prevent Entry Of .tro Ransomware
Windows OS is the most popular target for cyberattackers not because Windows is not secure. But, it is due to the fact that Windows is widely used in every corner of the world. Almost all computers are networked with one other and this makes Windows a soft target.
If a user follows a removal guide in addition to Malware Crusher, then it would add benefits to their system security. Few benefits are given below:
- It’s real-time protection feature, performs a deep scan, detects malicious software and infected files within your system.
- The Quarantine feature of the tool removes all infected files from your computer. Additionally, keeps a record of all deleted malicious program.
- Malware Crusher also creates a shield against Ransomware, Adware, Malware, Browser Hijackers, Viruses, Extensions and Trojans.
- The 24X7 online protective shield works as an anti-exploit technology and blocks the ransomware component before they hold files as a hostage.
- Malware Crusher tirelessly visits all domains, URLs and web pages to secure your online presence from fraudulent entities.
- Malware Crusher becomes fiercer in detecting keylogging, remote connections and saving your session data from being recorded.
To get a better security awareness on preventing cyber attacks and cyber security threats keep visiting us, forget not to download Malware Crusher.
Its 5-minute function could be a savior for your Windows computer!
Tips to Prevent virus and malware from Infecting Your System:
- Enable your popup blocker: Pop-ups and ads on the websites are the most adoptable tactic used by cybercriminals or developers with the core intention to spread malicious programs.
So, avoid clicking uncertain sites, software offers, pop-ups etc. and Install a powerful ad- blocker for Chrome, Mozilla, and IE
- Keep your Windows Updated: To avoid such infections, we recommend that you should always keep your system updated through automatic windows update.By doing this you can keep your device free from virus.According to the survey, outdated/older versions of Windows operating system are an easy target.
- Third-party installation: Try to avoid freeware download websites as they usually install bundled of software with any installer or stub file.
- Regular Backup: Regular and periodical backup helps you to keep your data safe in case the system is infected by any kind of virus or any other infection.Thus always backup important files regularly on a cloud drive or an external hard drive.
- Always have an Anti-Virus: Precaution is better than cure. We recommend that you install an antivirus like ITL Total Security or a good Malware Removal Tool like Download Virus RemovalTool
